Security specialists uncovered a new version of WannaCrypt0r 2.0 ransomware virus which is derived from the WannaCry ransomware. It encrypts user data and marks it with the .wncry extension.Wana Decrypt0r 2.0 is the nickname of the WannaCrypt0r 2.0 ransomware virus. You can remove WannaCrypt0r 2.0 ransomware virus via:
Manual Removal Guide
Recover Encrypted Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
WannaCrypt0r 2.0 ransomware virus is a new version of the WannaCry ransomware family that has just been identified in an ongoing hacker-coordinated attack. Like its predecessor, it seeks to encrypt user sensitive user data and cause other types of damage to the affected hosts.
Upon infection the WannaCrypt0r 2.0 virus immediately starts to prepare the environment by creating a Windows autorun task. This means that every time the computer boots the WannaCrypt0r 2.0 ransomware virus will automatically start. It also changes key registry values and monitors for user modifications. This effectively prevents manual removal options and the victims can only remove the infection with an automated anti-malware solution.
Similar Viruses: CryptoDevil ransomware virus
It also reports the virus to the criminal operators and their C&C servers. After this is complete, WannaCrypt0r 2.0 virus starts to encrypt user data based on a predefined file type extensions list. We suspect that it remains relatively unchanged from its parent- the Wannacry ransomware virus. The following extensions are processed:
123, .3dm, .3ds, .3g2, .3gp, .602, .7z, .aes, .ai, .ARC, .asc, .asf, .asp, .avi, .backup, .bak, .bmp, .brd, .c, .cgm, .class,
.cpp, .crt, .cs, .csr, .csv, .db, .dbf, .dch, .dif, .dip, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dwg, .edb, .eml, .fla, .flv,
.frm, .gif, .gpg, .gz, .hwp, .ibd, .jar, .java, .jpeg, .jpg, .js, .jsp, .key, .lay, .lay6, .ldf, .m3u, .m4u, .max, .mdb, .mdf, .mid, .mkv,
.mml, .mov, .mp3, .mp4, .mpeg, .mpg, .msg, .myd, .myi, .n, .nef, .odb, .odg, .odp, .ods, .odt, .ost, .otg, .otp, .ots, .ott, .p12, .PAQ,
.pas, .pdf, .pem, .php, .pl, .png, .pot, .potm, .potx, .ppam, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .psd, .pst, .rar, .raw, .rb, .rtf,
.sch, .sh, .sin, .slk, .sql, .sqlite3, .sqlitedb, .stc, .std, .stw, .suo, .swf, .sxc, .sxd, .sxm, .sxw, .tar, .tarbz2, .tbk, .tgz, .tif,
.tiff, .txt, .uop, .uot, .vb, .vdi, .vmdk, .vmx, .vob, .vsd, .vsdx, .wav, .wb2, .wk1, .wks, .wma, .wmv, .xlc, .xlm, .xls, .xlsb, .xlsm,
.xlsx, .xlt, .xltm, .xltx, .xlw, .zip
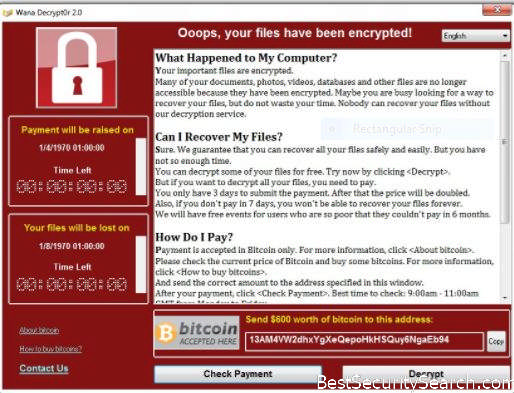
All affected data is renamed with the .wncry file extension. The ransomware note is displayed with a lockscreen which prevents ordinary user interaction until it is completely removed. It reads the following message:
Ooops, your files have been encrypted!
What Happened to My Computer?
Your important files are encrypted.
Many of your documents, photos, videos, databases and other files are no longer accessible because they have been encrypted. Maybe you are busy looking for a way to recover your files, but do not waste your time. Nobody can recover your files without our decryption engine.Can I Recover My Files?
Sure. We guarantee that you can recover all your files safely and easily. But you have not so enough time. You can decrypt some of your for free. Try now by clicking. But if you want to decrypt all your files, you need to pay. You only have 3 days to submit the payment. After that the price will be doubled. Also, if you don’t pay in 7 days, you won’t be able to recover your files forever. We will have free events for users who are so poor that they couldn’t pay in 6 months. How Do I Pay?
Payment is accepted in Bitcoin only. For more information click
. Please check the current price of Bitcoin and buy some bitcoins. For more information click . And send the correct amount to the address specified in this window.
After your payment click. Best time to check: 9:00am – 11:00am GMT.
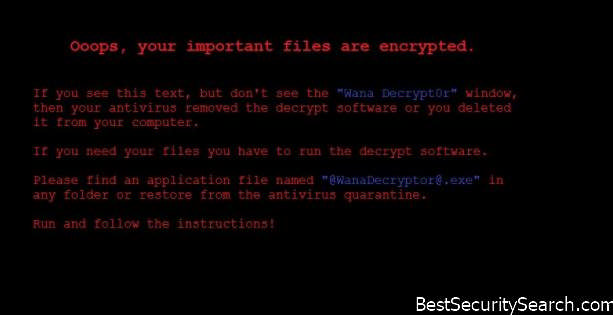
The noteworthy addition to the virus is the backup note. It is displayed in case the lockscreen is obstructed:
Ooops, your important files are encrypted.
If you see this text, but don’t see the “Wanna Decrypt0r” window,
then your antivirus removed the decrypt software or you deleted
it from your computer.If you need your files you have to run the decrypt software.
Please find an application file named “@[email protected]” in
any folder or restore from the antivirus quarantine.Run and follow the instructions!
The criminals use several methods to extort the victims for the payment:
Ransomware Fee Modification – The hackers employ a short time limit. If the payment is not done by then it is raised double.
Decryption Limit – If the WannaCrypt0r 2.0 ransomware virus fee is not paid completely until a certain time limit then the private decryption key is deleted from the remote servers. File recovery is possible if the WannaCrypt0r 2.0 ransomware virus is removed with a quality anti-malware solution and data recovery software is utilized.
Fixed Ransomware Sum – The hackers specify a fixed sum in US Dollars instead of Bitcoins.
Support Information – The criminals behind the WannaCrypt0r 2.0 ransomware virus have added information about buying the digital currency. Contact options are also available if the victims want to contact the hackers.
Depending on the hacker configuration the WannaCrypt0r 2.0 ransomware virus samples can also delete the found shadow volume copies. This renders data recovery possible only via professional grade software. It is possible that future iterations can include additional features.
We suspect that updates of the WannaCrypt0r 2.0 ransomware virus can cause further damage to the system. The virus engine can modify essential Microsoft Windows settings that can disable functionality or make certain applications and services stop working altogether. In the majority of cases, complex malware such as the WannaCrypt0r 2.0 ransomware virus also lead to significant performance issues. Threats like this one can also be used to deliver additional viruses to the infected hosts.
Evolved versions of the WannaCrypt0r 2.0 ransomware virus can be used to harvest sensitive information from the infected machines. The hackers can opt to take full control of the computers or spy on the users’ activities which include live video surveillance, keystroke recording and other types of malicious activities.
To calculate the time of the infection the virus engine uses several data extracted from the machine during the first phase of infection. As always the hackers have supplied detailed information about how the victims can obtain the digital currency and pay the fee to them.
WannaCrypt0r 2.0 Ransomware Virus Distribution Methods
The WannaCrypt0r 2.0 ransomware virus has been identified in an ongoing attack campaign around the world. At the moment we cannot judge what are the primary spread methods associated with the threat. However, we assume that the WannaCrypt0r 2.0 ransomware virus is going to spread via the most popular strategies.
Email spam campaigns are one of the primary carriers of prior versions of the virus family. They employ social engineering tricks that attempt to make the targets infect themselves with the malware. This is done by downloading and running the dangerous executable files that are either directly attached to the messages or linked in the body content.
The use of infected documents has become popular in the last few months. Computer hackers bundle the WannaCrypt0r 2.0 ransomware virus with software installers of famous applications, games, utilities and patches. The resulting files are then spread posing as the official packages.
Usually such instances are uploaded to various hacker-controlled download sites and portals. They may appear as the official domains, the victims can spot that they are fake by taking a closer look at their addresses. Usually, only a single letter or digit reveals the difference. P2P networks like BitTorrent are other options for spreading the WannaCrypt0r 2.0 ransomware virus. The trackers and other sites that deal in such software are usually used for distributing malware and pirate content.
Browser hijackers are also considered an option for spreading malware strains associated with the WannaCrypt0r 2.0 ransomware virus. They are particularly dangerous for the individual users as they modify important settings and endanger their privacy. One of the major behavior patterns that they follow is the modification of the default homepage, search engine, and new tabs page. In addition locally hosted user information can be uploaded at will including: cookies, history, form data, account credentials, settings and bookmarks. It also places a hacker-controlled site as the default homepage, search engine, and new tabs page.
Direct hacker intrusions are another possible source of WannaCrypt0r 2.0 ransomware virus infections. Computer criminals can use automated vulnerability testing frameworks to look out for outdated software versions. This is the reason why security specialist advise users to always update to the latest available versions.
Remove WannaCrypt0r 2.0 Ransomware Virus and Restore .wncry Encrypted Files
WARNING! Manual removal of the WannaCrypt0r 2.0 ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
WannaCrypt0r 2.0 Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover .WNCRY Files
WARNING! All files and objects associated with WannaCrypt0r 2.0 ransomware should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD WannaCrypt0r 2.0 Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



