
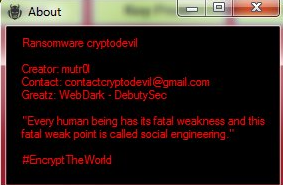
The CryptoDevil ransomware is a new independent malware threat created by a hacker known as mutr0, read our removal guide to learn more about it.
CryptoDevil Ransomware Description
We have received confirmation about the discovery of a new virus known as CryptoDevil ransomware which has been made by a hacker under the alias of mutr0. The security analysis does not show any similarities between its main engine code and any of the famous malware families which means that it is an independent creation.
The virus engages in the basic behaviour patterns utilized by all viruses of its type by starting an encryption engine which targets sensitive user data. Unlike some of the basic independent virus iterations the CryptoDevil ransomware does feature an extra – upon infection it starts a screenlocker which prohibits ordinary computer interaction. This is a widely used tactic among hackers as it effectively scares the victims and raises the paid users ratio significantly.
The encryption engine is started after the infection has been made. It targets the most wiely user data such as photos, documents, music, videos, archives, backups and etc. All of the affected file type extensions are renamed using .devil extension.
The ransomware’s screen shows the following message to the victims:
Your Computer Has Been Locked Your computer have been successfully locked you have up to 70 hours
to buy a key to unlock your contract ncase files will be deleted.
Email: [email protected]
Payment: Bitcoin 20
After the necessary unlock code has been entered (kjkszpj) the virus displays another screen:
Instruction! How To Remove my virus 1. Open Start Menu 2. Go to Startup 3. Delete CryptoDevil.exe End! Thanks for colaboration
By crafting such a note the hackers hope to confuse the victims by providing removal instructions of their own. The victims should not trust them as in many cases they are counterfeit and the virus engine remains installed on the computer hosts. This is a widely used tactic which attempts to make the users think that they are safe while the CryptoDevil ransomware remains intact.
Some of the reasons why this is done include the following:
- Deployment of additional threats – The virus may be used as a convenient payload dropper which can introduce other viruses upon infection or when a certain criteria is met, e.g. the unlock key is entered.
- Remote Access – The hacker behind the CryptoDevil ransomware (multr0) may use the infetion as a decoy for including a remote access Trojan.
- Information Harvesting – If the necessary modules are integrated the main engine can be used to transmit sensitive user data such as files, stored cookies, account credentials, browsing history and etc.
Do note that the hacker requests a very large ransomware sum – 20 Bitcoins which is about 21093 US Dollars.
CryptoDevil Ransomware Distribution
The first malware samples of the CryptoDevil ransomwar were detected in March 2017 and they mainly target English-speaking users. As the samples are limited in their attack waves the security experts were not able to pinpoint the main infection route. This is why we pressume that the hackers behind the attacks use the most widely used strategies:
- Download Sites, Portals & P2P Networks – Computer criminals frequently use hacker-controlled or compromised sites and portals to distribute the virus strains. As P2P networks are one of the primary download sources for a variety of content, the CryptoDevil Ransomware can also be found posing as legitimate software on BitTorrent trackers.
- Email Spam – Hackers utilize email messages which contain the virus as an attachment or link to infected files in the body of the message. There are different configurations, however one of the most popular ones employ infected Office documents that pose as being sent by a legitimate company or institution.
- Infected Software – The virus can be found in bundled software installers that pose as popular freeware and trial versions of well-known games, applications, utilities and patches.
- Dangerous Scripts – Mallicious scripts such as browser hijackers and ad redirects can lead to a malware infection via redirects or direct ransomware download code executed by the victim’s browser.
Summary of the CryptoDevil Ransomware
| Name |
CryptoDevil |
| File Extensions |
.devil |
| Ransom |
20 Bitcoins |
| Easy Solution |
You can skip all steps and remove CryptoDevil ransomware with the help of an anti-malware tool. |
|
Manual Solution |
CryptoDevil ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
CryptoDevil Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely CryptoDevil Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover CryptoDevil Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore CryptoDevil Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



