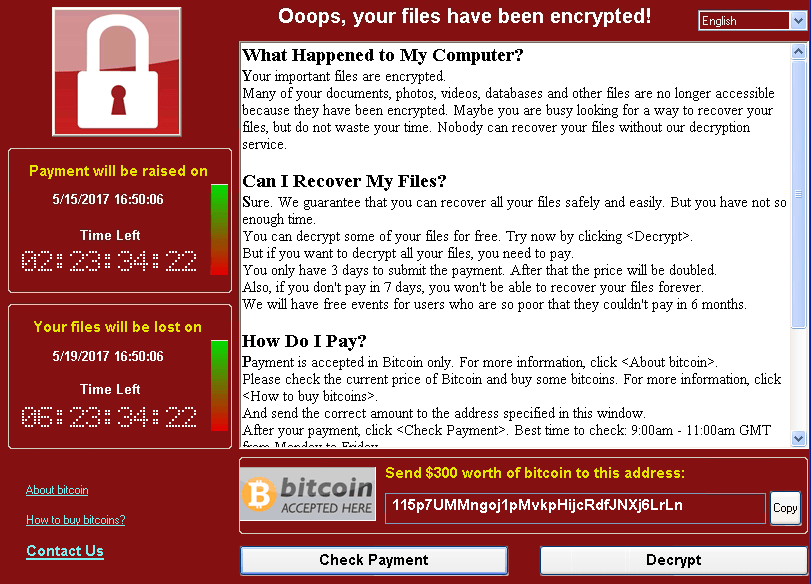
A pop up that starts with the phrase “Oops, your files have been encrypted!” displayed on your PC screen is a sign of WannaCry ransomware virus infection that is running on the machine. WannaCry virus targets vulnerable Windows systems all around the world aiming to encrypt sensitive data and extort victims for around $300 ransom payment. We strongly suggest you to not pay that sum to the cyber criminals. Instead, remove WannaCry immediately from your system and only then try to recover your encrypted files.
Manual Removal Guide
Recover .WNCRY Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Update: New “Ooops, Your Important Files Are Encrypted” Ransomware May Not Be Related to WannaCry
New “Ooops, Your Important Files Are Encrypted” ransomware has been spread lately (End of June, 2017). Researchers say it may be a WannaCry-like variant, however that new version uses a different ransom message that looks like this:
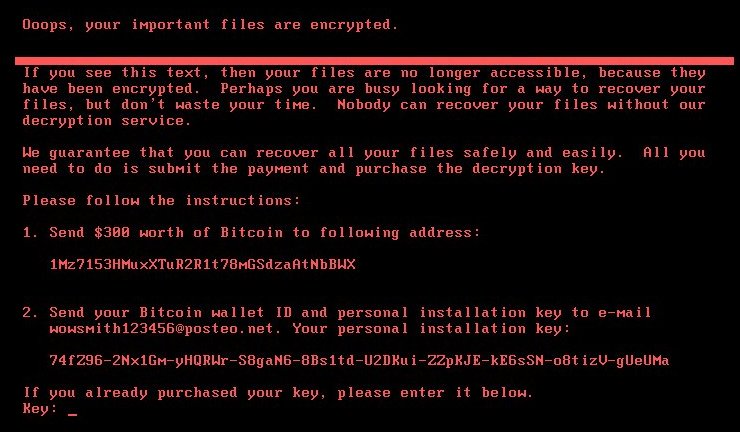
And it reads like this:
Ooops, your important files are encrypted.
If you see this text, then your files are no longer accessible, because they have been encrypted. Perhaps you are busy looking for a way to recover your files, but don’t waste your time. Nobody can recover your files without our decryption service.
We guarantee that you can recover all your files safely and easily. All you need to do is submit the payment and purchase the decryption key.
Please follow the instructions:
1. Send $300 worth of Bitcoin to following address:
1Mz7153HMuxXTuR2R1t78mGSdzaAtNbBWX
2. Send your Bitcoin wallet ID and personal installation key to e-mail [email protected]. Your personal installation key:
****-*****-*****-*****-*****-*****-*****-*****-*****-****
If you already purchased your key, please enter it below.
Key:
It appears that this new crypto virus is a new strain of Petya ransomware. The attack has so far hit over 12 000 machines in around 65 countries around the world.
While WannaCry ransomware locks individual files, this new variant of Petya ransomware virus is locking the whole hard drive making it completely unusable. Hackers demand that victims should pay $300 in bitcoins to unlock encrypted files. However, the advice of the security industry is:
Don’t pay the ransom because actually, you’re not going to get your files back.
Follow our removal guide and remove Petya ransomware completely from the infected host.
Oops, Your Files Have Been Encrypted! – All Before and After This Event
The “Oops, your files have been encrypted!” ransom note is part of malware infection known as WannaCry ransomware. Ransomware is a type of malware that restricts access to computer files and demands online ransom payment in order to remove the restrictions. This specific one is also known under the names WannaCrypt, WanaCrypt0r, Wana Decrypt0r, WCrypt, or WCRY. WannaCry virus removal is essential for the overall PC security.
A well-crafted dropper installs the ransomware on the PC the infection flow is triggered by an executable file mssecsvc.exe. Once the file is running on the system WannaCry virus performs various system modifications and encrypts the data set in its target list. The initial encryption of the data is implemented via AES cipher algorithm. According to some security specialists’ researches, each encrypted file is locked by a different key which is then also encrypted with RSA algorithm. The corrupted files receive one of the following malicious file extensions .WNCRY .WCRY or .WNCRYT and are no longer usable. Generally, WannaCry virus is believed to encrypt the following file types:
.123, .jpeg , .rb , .602 , .jpg , .rtf , .doc , .js , .sch , .3dm , .jsp , .sh , .3ds , .key , .sldm , .3g2 , .lay , .sldm , .mkv , .std , .asp , .mml , .sti , .avi , .mov , .stw , .backup , .mp3 , .suo , .bak , .mp4 , .svg , .bat , .mpeg , .swf , .bmp , .mpg , .sxc , .brd , .msg , .sxd , .bz2 , .myd , .sxi , .c , .myi , .sxm , .cgm , .nef , .sxw , .class , .odb , .tar , .cmd , .odg , .tbk , .cpp , .odp , .tgz , .crt , .ods , .tif , .3gp , .lay6 , .sldx , .7z , .ldf , .slk , .accdb , .m3u , .sln , .aes , .m4u , .snt , .ai , .max , .sql , .ARC , .mdb , .sqlite3 , .asc , .mdf , .sqlitedb , .asf , .mid , .stc , .asm , .cs , .odt , .tiff , .csr , .onetoc2 , .txt , .csv , .pas , .vmx , .docb , .pdf , .vob , .docm , .pem , .vsd , .docx , .pfx , .vsdx , .dot , .php , .wav , .dotm , .pl , .wb2 , .dotx , .png , .wk1 , .dwg , .pot , .wks , .edb , .potm , .wma , .eml , .potx , .wmv , .fla , .ppam , .xlc , .flv , .pps , .xlm , .frm , .ppsm , .xls , .gif , .ppsx , .xlsb , .gpg , .ppt , .xlsm , .gz , .pptm , .xlsx , .h , .pptx , .xlt , .hwp , .ps1 , .xltm , .ibd , .psd , .xltx , .iso , .pst , .xlw , .jar , .rar , .zip , .java , .raw., .ost , .uop , .db , .otg , .uot , .dbf , .otp , .vb , .dch , .ots , .vbs , .der” , .ott , .vcd , .dif , .p12 , .vdi , .dip , .PAQ , .vmdk , .djvu
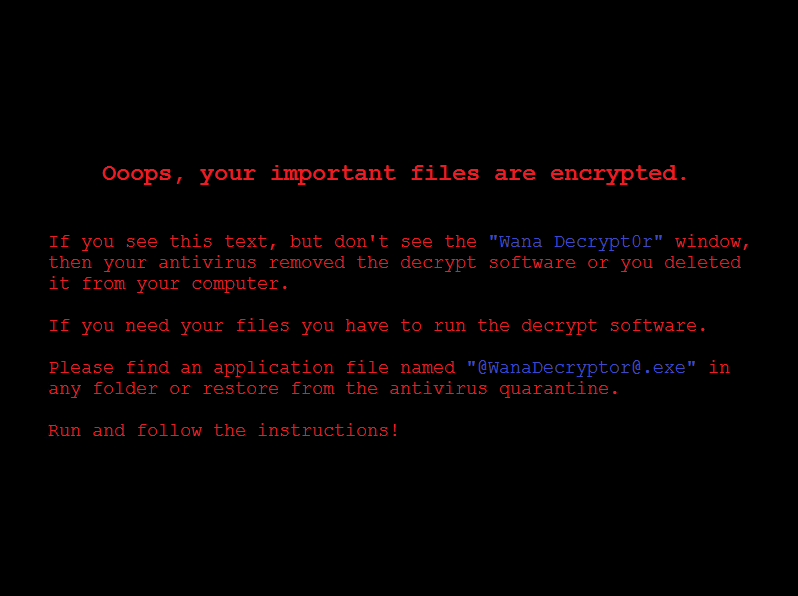
The ransomware also creates a ransom note file named @[email protected] in every folder which contains encrypted files. By modifying Windows registry, the virus replaces the desktop wallpaper with the ransom note. It depicts a ransom message that reads:
Ooops, your important files are encrypted.
If you see this text, but don’t see the “Wanna Decrypt0r” window,
then your antivirus removed the decrypt software or you deleted
it from your computer.If you need your files you have to run the decrypt software.
Please find an application file named “@[email protected]” in
any folder or restore from the antivirus quarantine.Run and follow the instructions!
WannaCry ransomware virus also runs an executable displaying the “Oops, your files have been encrypted!” window that contains another ransom message. Hackers indicate victims to pay $300 ransom in Bitcoins to a predefined Bitcoin address in a particular time frame.
Upon the encryption process, the ransomware deletes volume shadow copies by running the following command:
cmd.exe /c vssadmin delete shadows /all /quiet
By deleting shadow volume copies, the ransomware prevents one of the possible data recovery approaches.
Furthermore, WannaCry virus modifies and creates new values in Windows registries that enable its automatic execution each time the system is started. The following keys and sub keys are targeted by WannaCry malicious code:
HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run
HKCU\Control Panel\Desktop\Wallpaper
HKCU\Software\WanaCrypt0r
All mentioned malicious files and objects could be removed by yourself. Below you can find a detailed step-by-step guide how to remove WannaCry ransomware virus and proceed further with data recovery attempts. Have in mind that many victims have paid the ransom that appears to be a not working decision. Hackers probably lost many of the decryption keys and are sending wrong decryption keys that do nothing but steal your money.
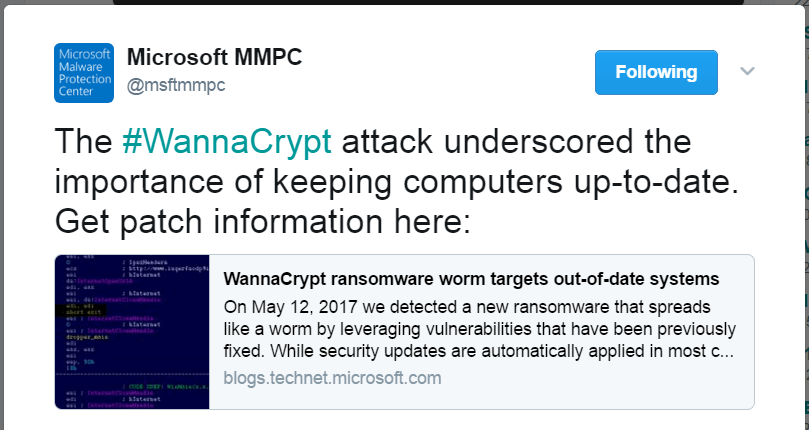
WannaCry Targets Out-Of-Date Systems
Usually, hackers leverage social engineering emails as a primary attack vector. They rely on your will to download and execute the malicious WannaCry payload. The crafted emails are likely to contain clickable links in the content or downloadable attachments. A single click on the link may result in an unnoticed download of WannaCry payloads on the computer. The attachments may be presented as commonly files like PDF, TXT, DOC, DOCX, and JPG. However, all these files may contain crafted malware code in them so once they are opened, they automatically install the WannaCry virus payload on the computer.
Once the malware infects the system, it starts the data encryption process. Furthermore, WannaCry has a worm spreading functionality that allows it to attack all vulnerable systems of the same network via SMB exploit. Ransomware handlers used ExternalBlue to exploit a critical vulnerability in Windows SMB protocol. The ExternalBlue exploit is believed to have been developed by the U.S. National Security Agency (NSA). Unfortunately, it was leaked by a hacker group that allows malicious intenders to use it as part of the worldwide WannaCry ransomware attack.
The vulnerability exploited by WannaCry ransomware virus was fixed with the release of the MS17-010 security bulletin that is part of Microsoft March patch. An attack of the critical SMB vulnerability CVE-2017-0145 could lead to remote code execution or leak of information stored on the server. Once the dropper Trojan infects a PC with WannaCry virus, it attempts to exploit the SMB CVE-2017-0145 vulnerability in other computers connected to the same network.
Related: Microsoft March 2017 Security Bulletins Patch 47 Critical Vulnerabilities
This attack is expected to evolve over time, so except ExternalBlue other exploits may also be used during the infection flow.
Remove WannaCry Virus and Restore Encrypted Files
WARNING! Manual removal of the WannaCry ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
WannaCry Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover .WNCRY Files
WARNING! All files and objects associated with WannaCry ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD WannaCry Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



