The criminals behind the dreaded Cerber ransomware have released an update to the malware source code that renders the known decryptors useless. They have also tightened security measures in defending the criminal software from security experts.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
The Newest Version of Cerber Is Even More Sophisticated
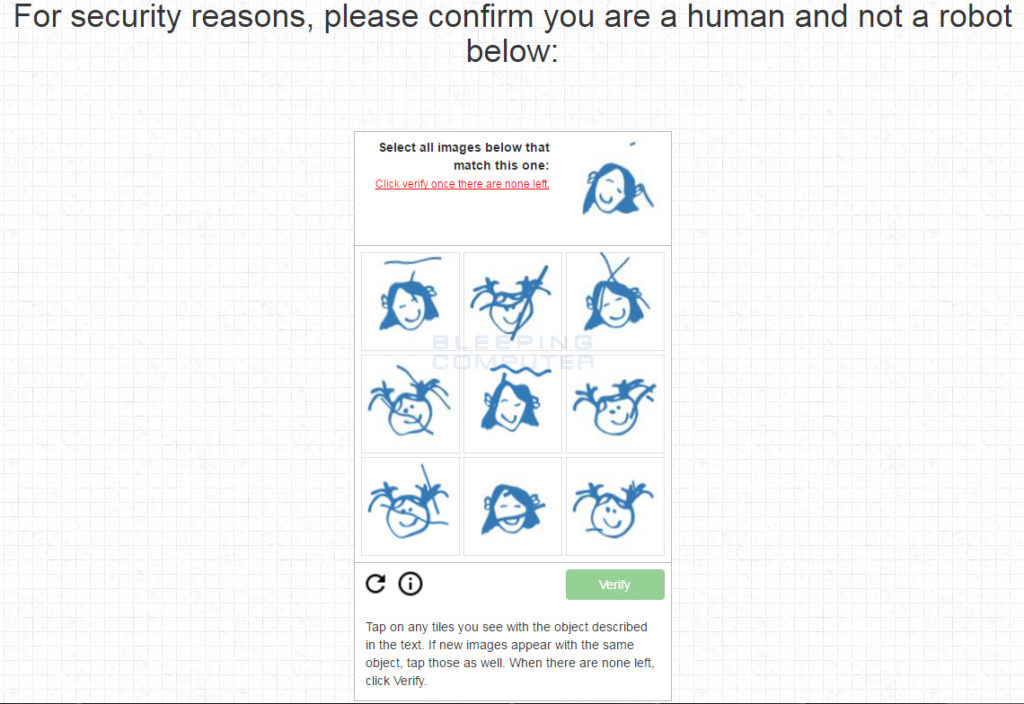
The newest iteration of Cerber has updated code, and the developers have taken security measures that prevent countermeasures made by security experts and vendors. The newest update blocks a well-known tool that decrypted the ransom files from the victim computers. At the same time the malicious users behind the Cerber ransomware have added a new CAPTCHA form to their payment system to the login page.
This makes impossible the automated exploitation of security flaws located on the criminal remote servers. The working solution to this point relied on a security vulnerability that was exploited by the security experts. The CAPTCHA form prevents that from happening and thus renders the decryptor useless.
The team behind the decyptor has not revealed details about how their software works. The CAPTCHA might be an additional security measures created by the malware developers, or it might be the issue that is blocking the decrypting algorithm.
Still no master key to the encryption scheme is known for all versions of the Cerber ransomware.
For more information on Cerber2 check out our guide.