Cerber2 is the latest variant of Cerber ransomware. It appends the extension .cerber2 to the encrypted files. Then Cerber2 locks the screen and an image that displays the ransom message appears. Cerber2 ransomware was discovered by a security researcher from Trend Micro. The cyber criminals have made significant changes in the code of Cerber2 so it could not be decrypted by the released decryption tool for Cerber.
| Name |
Cerber2 Ransomware |
| File Extensions |
.cerber2 |
| Ransom |
0.30 to 1 Bitcoins |
| Solution #1 |
Cerber2 ransomware can be removed easily with the help of an anti-malware tool, a program that will clean your computer from the virus, remove any additional cyber-security threats, and protect you in the future. |
|
Solution #2 |
Cerber2 Ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
The ransomware may be spread with spam email campaigns. |
Features of Cerber2 Ransomware
The researcher @panicall from TrendMicro has received samples of Cerber2 and analyzed it in detail. One of the observed changes is that the new variant uses packer that wrap the files. As a result Cerber2 is harder to detect and analyze. The ransomware can shut down some active processes and thus successfully infects the system.
The list of file extensions that are encrypted after infection with Cerber2 is pretty long. It scans the hard drives and encrypts all files that have one of the following extensions:
After the encryption process the extension .cerber2 is appended to the files. The names of the files are replaced with ten random characters. one of the changes in Cerber version 2 is the way of generating the key now it uses Microsoft API CryptGenRandom. The generated key is 32 bytes instead of 16 bytes as in the previous version.
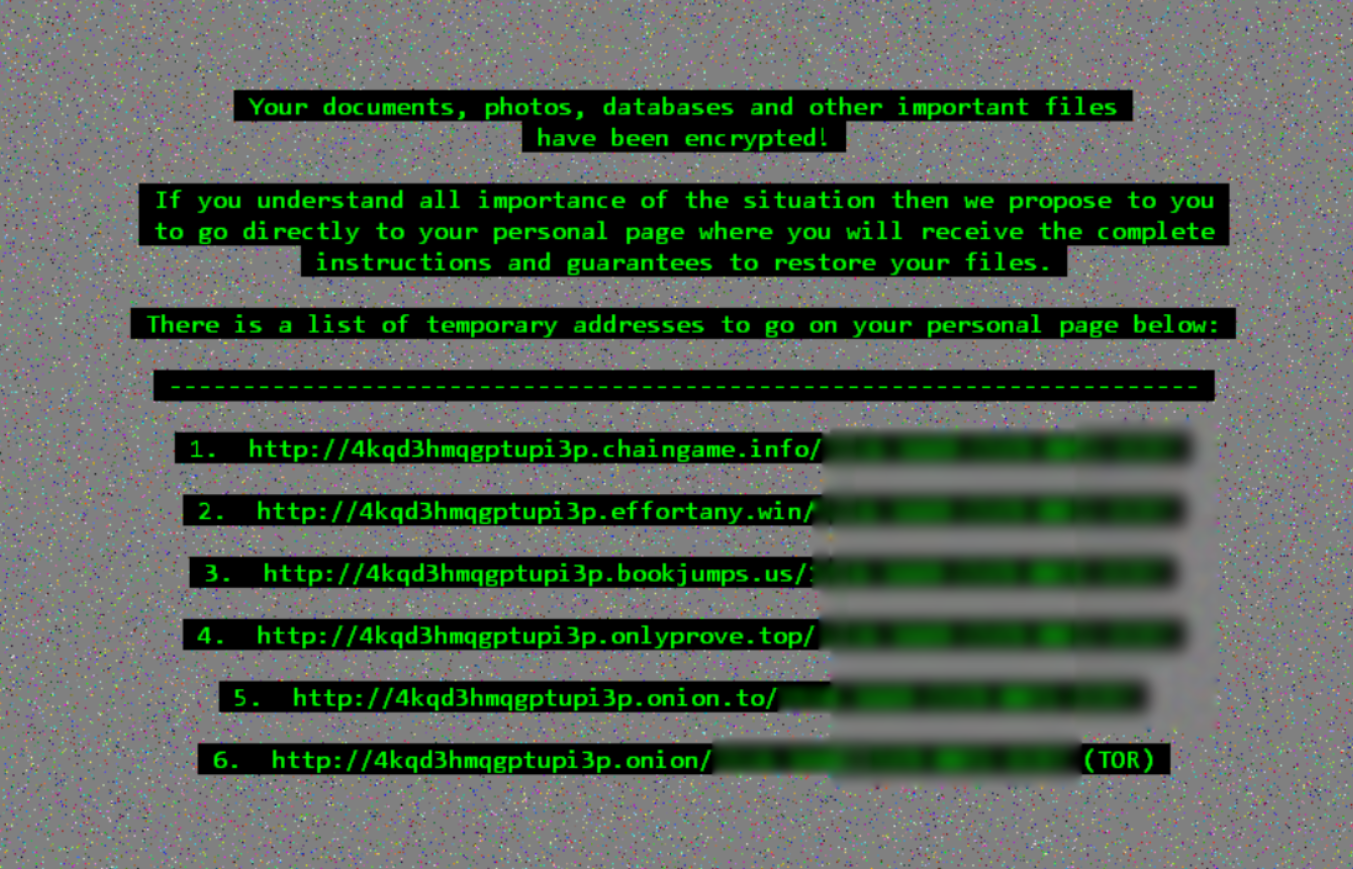
At the next stage of infection Cerber2 locks the computer screen and an image with the ransom message appears. This is the ransom image used by Cerber2:
Here is what the text on the image says:
Your documents, photos, databases, and other important files have been encrypted!
If you understand all importance of the situation then we propose to you to go directly to your personal page where you will receive the complete instructions and guarantees to restore your files.
There is a list of temporary addresses to go on your personal page below:
During the first five days after the infection, cyber criminals want 0.30 Bitcoins that amounts to 175 US dollars. After the fifth day victims could get the decryption key for their .cerber2 files at a price of 0.61 Bitcoins or around 350 US dollars. Anyway paying the ransom is not advisable because there is no guarantee that the crooks will send a working key that will decrypt the files. Furthermore, such payment can only support their malicious actions and encourage them to continue the development of new threats.
Cerber2 – Spread Methods
Cerber2 can be hidden in an icon of a video game character “Anka”.
![]() The icon contains executable files that infect the system with the ransomware. The ransomware may be spread with spam email campaigns. It is not advised to open emails and download attachments that seem suspicious. Cerber2 may infect the system through compromised websites, file-sharing services and suspicious links on social media websites.
The icon contains executable files that infect the system with the ransomware. The ransomware may be spread with spam email campaigns. It is not advised to open emails and download attachments that seem suspicious. Cerber2 may infect the system through compromised websites, file-sharing services and suspicious links on social media websites.
Remove Cerber2 Ransomware and .cerber2 Extension
If you are a victim of Cerber2 ransomware, you should instantly remove it from the system. We have provided manual instructions how to remove Cerber2 from your computer. Furthermore, you can use reliable anti-malware program that will eliminate the threat automatically and will prevent the computer from future attacks.
Step-by-step manual instructions:
Try to Load Your PC in Safe Mode
For various Windows OS’s:
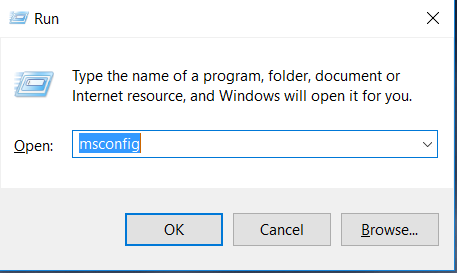
1) Hit WIN Key + R

2) A Run window will appear. In it, write “msconfig” and then press Enter.
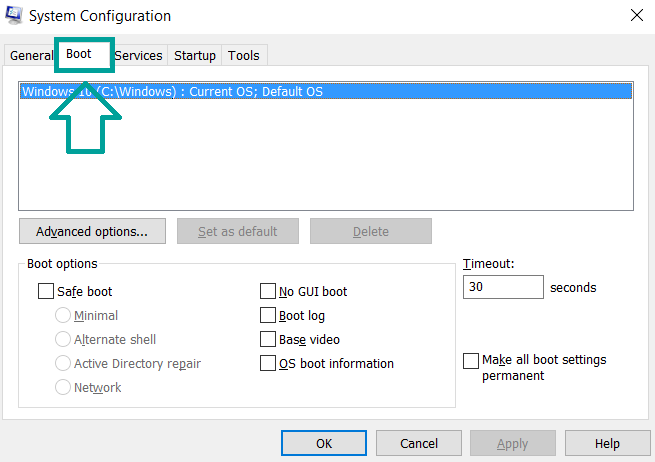
3) A Configuration box shall appear. In it Choose the menu named “Boot”.
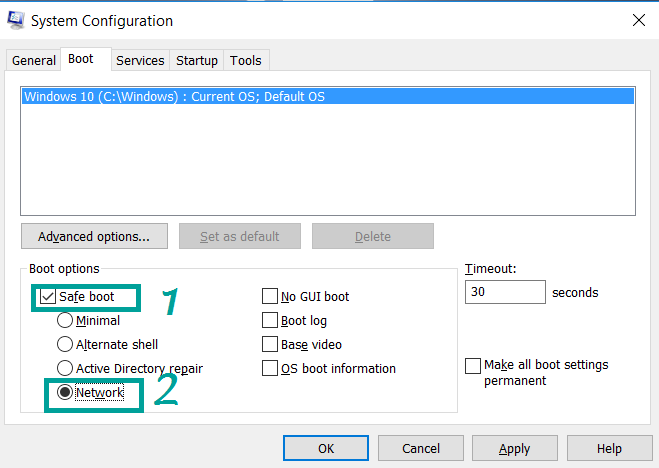
4) Choose the Safe Boot preference and then go to Network under it to tick it.
Eliminate the malicious processes
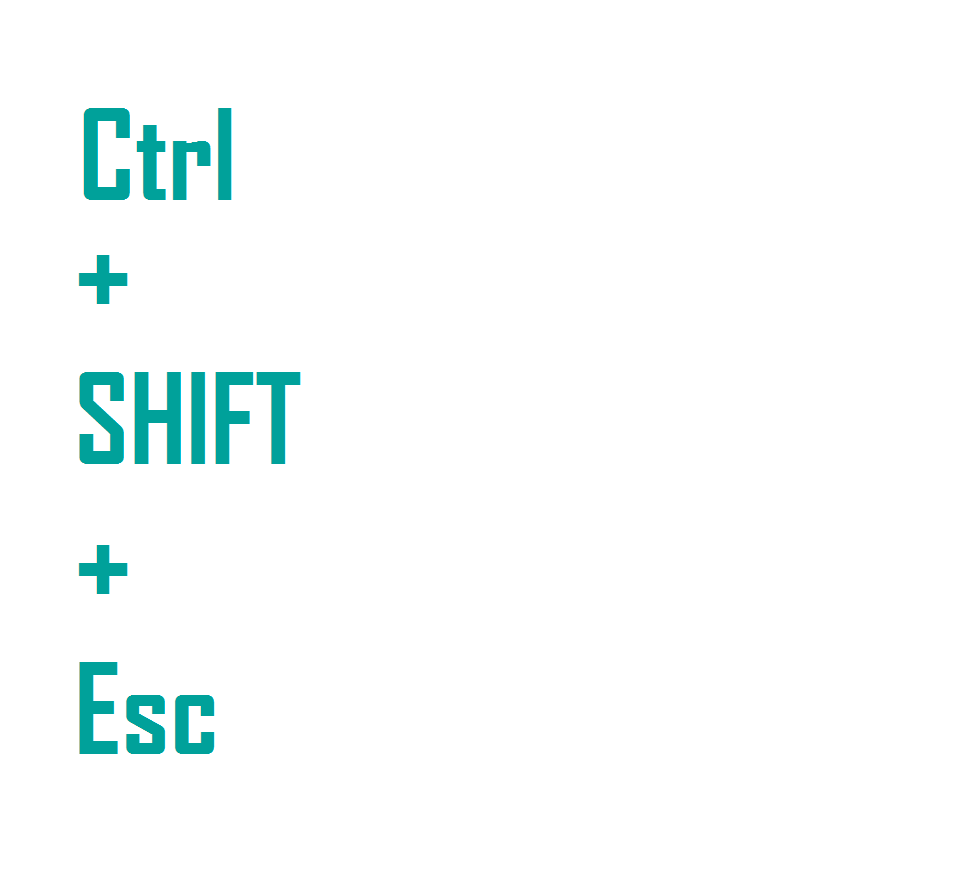
1) hit the following key combination: CTRL+ESC+SHIFT
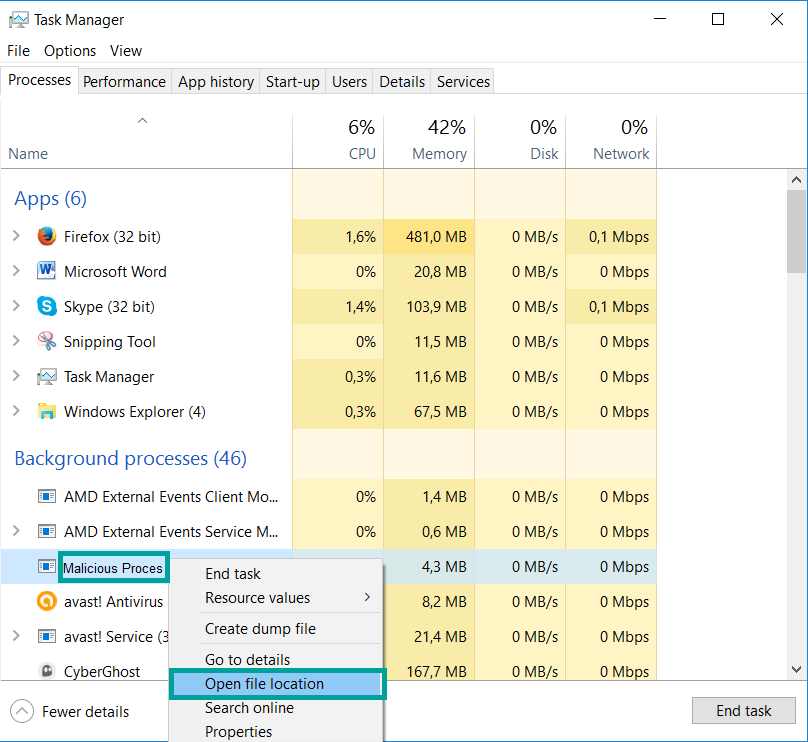
2) Get over to Processes.
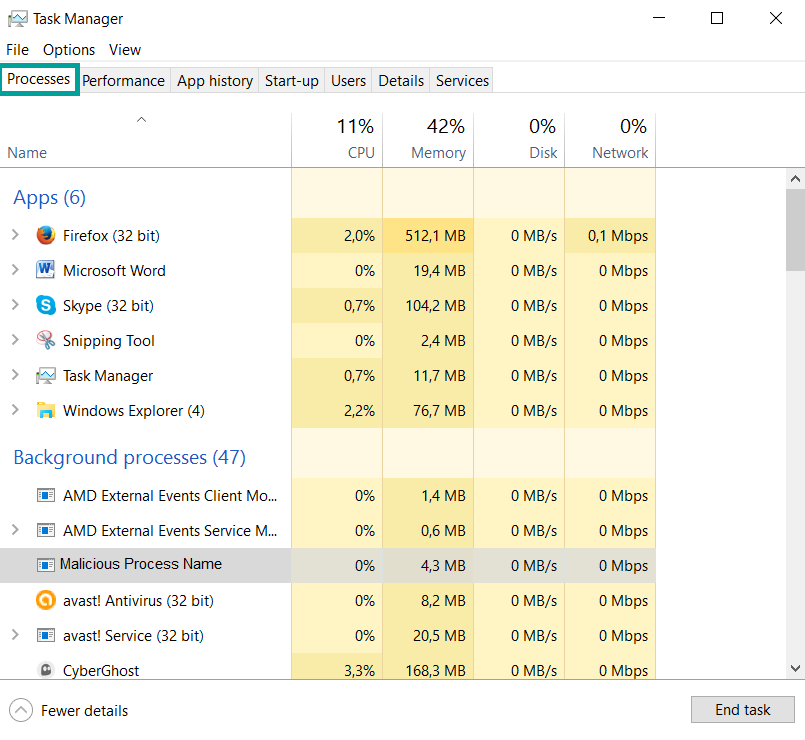
3) Choose the suspicious process if you have found it and then right click it after which click on “Open File Location”.
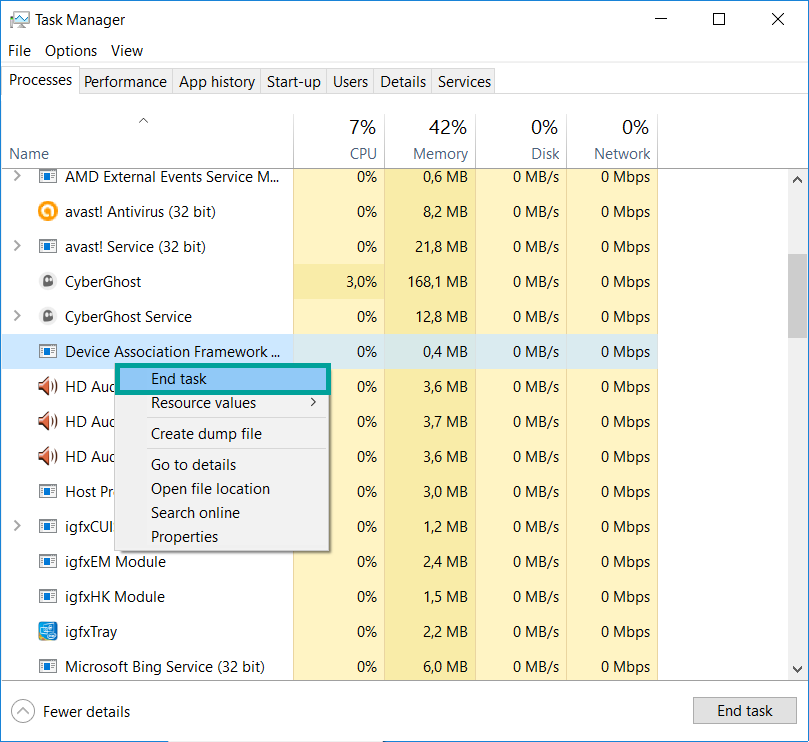
4) End the malicious process by again right-clicking and choosing “End Process”.
Delete registry objects created by the Hitler ransomware virus.
For all Windows versions:
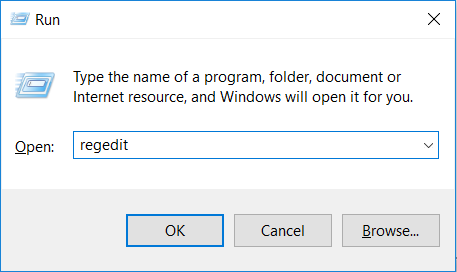
1) Again type simultaneously the Windows Button + R. key combination.

2) In the type box, write “regedit”(without the inverted comas) and hit Enter.
3) Type the CTRL+F key combination and then write the malicious name in the search type field to locate the malicious executable.
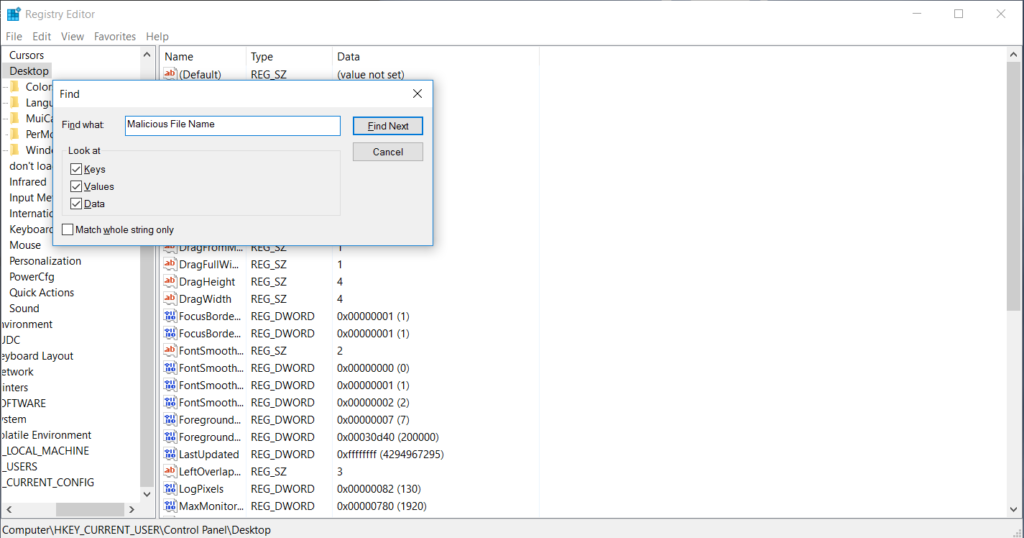
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys.
Recover files encrypted by Crypto-Vriuses.
If you want to try recovering files yourself, you have several options:
Option One: By using Windows’s System Restore
1) Hit the Windows Button + R. key combination.

2) After the “Run” Window pops up, write “rstrui” and hit on the Enter button.
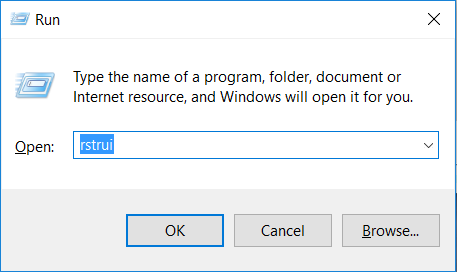
Choose a restore point and continue.
IMPORTANT: If you want to be more effective, we strongly suggest booting in safe mode if you are to do this!
Option Two: By using Windows’s Shadow Volume Copies
To access shadow volume copies you may require a program, like Shadow Explorer. Install it open it and make it scan for shadow copies. If you have them enabled, this method will work, in case the crypto-virus has not deleted them.
Option Three: By using various Recovery Software
This option will not ensure maximum effectiveness and recovery rate but still, you may restore several files. Most data recovery programs are available for free online, simply Google “Data Recovery Software”.
Prevent viruses from damaging your files in the future.
To protect your important data we suggest that you store it in the cloud. Programs that makes online backup possible also enable you to schedule auto backup on different time periods and this way, even if you lose your data, you can find it uploaded in securely encrypted account, access to which only you have.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter