The Blooper virus is an encryption ransomware that uses a strong cipher to target user files. In comparison with similar malware it does not modify the file extension of the affected data. It poses as being made by Microsoft and is of unknown origin. Victims can recover their data by following our detailed removal guide.
Manual Removal Guide
Recover Encrypted Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How Does Blooper File Virus Infiltrate the System?
The Blooper virus is a ransomware that that encrypts system and user data based on a predefined list of target file type extensions. Its virus engine uses the AES encryption cipher to process the files. It is being distributed as single binary files (Blooper.exe) and bears a fake copyright attributed to Microsoft.
The initial security analysis does not show any similarity between the sample and any one of the known malware families. This means that it is an independent creation by the hacker or hacker collective behind it.
The Blooper virus starts to harvest system information such as the active computer name and cryptographic machine unique ID. In addition the Blooper virus analyzes the location settings of the compromised computers. Similar viruses use the information to display a different ransomware note based on the language of the installed operating system (Microsoft Windows).
Before the encryption process is started the Blooper virus engine queries the connected storage devices – this includes not only the hard drives, but also all placed removable storage (USB flash drives or external drives for example). Depending on the configuration network shares may also be affected.
During the analysis it has been discovered that the ransomware also initializes the .NET runtime environment and also modifies files in Windows system directory.
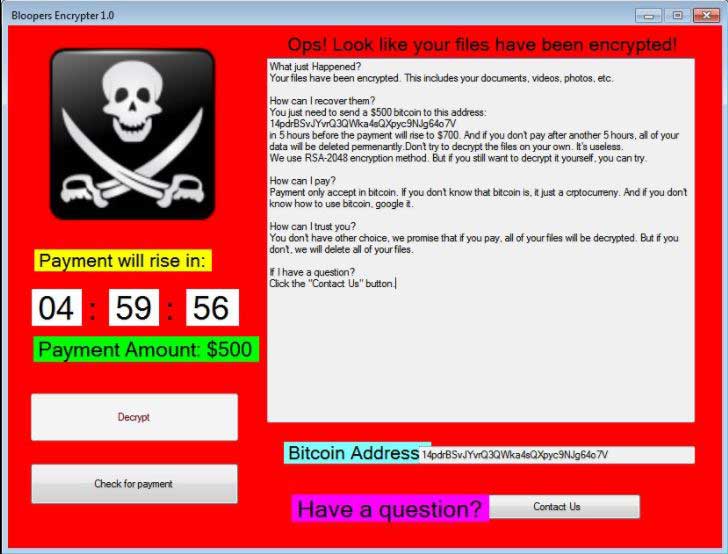
When all preliminary checks are made the encryption process is engaged. When this is started the application draws an application frame called “Bloopers Encrypter 1.0”. It displays a status window that reads “The software is now encrypting your files…”. When the process is done an error pop-up is displayed “Ops! Look like your files have been encrypted!”.
A screenlocker that prohibits ordinary computer interaction is instituted by the virus engine. It can only be removed by using a quality anti-spyware solution. By following our removal guide affected users can recover both their systems and restore their data. The screenlocker is similar to other malware that employ a template-based note. The engine draws a full-screen application frame that reads the following message:
Ops! Look like your files have been encrypted!
What just happened?
Your files have been encrypted. This includes your documents, videos, photos, etc.How can I recover them?
You just need to send a $500 bitcoin to this address:
14pdrBSvJYvrQ3QWka4sQXpyc9NJg64o7V
in 5 hours before the payment will rise to $700. And if you don’t pay after another 5 hours, all of your
data will be deleted permamently. Don’t try to decrypt the files on your own. It’s useless.
We will USE RSA-2048 encryption method. But if you still want to decrypt it yourself, you can try.How can I pay?
Payment onlt accept in bitcoin. If you don’t know that bitcoin is, it just a crptocurreny. And if you doný
know how to use bitcoin, google it.How can I Trust you?
You don’t have other choice, we promise that if you pay, all of your files will be decrypted. But if you
don’t, we will delete all of your files.If I have a question?
Click the “Contact Us” button.Bitcoin address: 14pdrBSvJYvrQ3QWka4sQXpyc9NJg64o7V
Have a question? Contact Us
Some of the captured malware samples have been confirmed as being fake. This means that the users can close the application frame and find that their files have not been encrypted.
Unlike other malware, the Blooper virus does not communicate with remote C&C servers in its current version. We suspect that future versions might include Trojan capabilities or other added features.
At the current moment that majority of the anti-virus products cannot detect the samples.
Related: D2+D Ransomware Virus, WannaCrypt0r 2.0 Ransomware Virus
Infection Flow of Blooper File Virus
The Blooper virus uses different tactics to infect the victim computers. The initial attack wave has been detected in the last days of May 2017 and according to the available research the hackers target mainly English-speaking users. As the ransomware spreads across the whole world, not just individual countries, the hackers behind it are able to use strategies that can have a high infection ratio.
As the Blooper virus is distributed in a single binary executable file (Blooper.exe) it is easy to distribute it in email spam campaigns. The hackers use social engineering tactics that confuse the victims into believing that the sent messages come from legitimate users, companies or insitutions. The Blooper virus payload may be directly attached or delivered as a hyperlink. Infected office documents containing malicious macros may also be used in large-scale campaigns. When the victims open them up a prompt appears that asks them to enable the built-in scripts. If this is done the virus is downloaded from a remote server and executed on the local machine.
The Blooper virus file can also be bundled in software bundles that are modified by the hackers. They are distributed on hacked or hacked-controlled sites as well as P2P networks like BitTorrent.
Malicious web browser addons, also known as browser hijackers, are another source of infections. Upon installation they change important settings such as the default home page, search engine and new tabs page. In addition they harvest the stored data: browser sessions, history, stored passwords, cache, bookmarks and form data.
Direct hacker intrusion attempts can be used to spread the Blooper virus. The criminals use automated vulnerability testing kits against large computer networks. They use software vulnerability payloads against outdated installations. This is the reason why security experts advise users to always update all installed applications and operating system.
Depending on the scale of the attacks the criminals may also opt to use web scripts and ad networks that can redirect to the file payloads.
Remove Blooper File Virus and Restore Data
WARNING! Manual removal of Blooper file virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Blooper File Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
DOWNLOAD Blooper Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Recover Encrypted Files
WARNING! All files and objects associated with Blooper file virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button
Preventive Security Measures
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



