A screen named “D2+D Ransomware detected but don’t worry, this is harmless after purchase” that has blocked the access to the PC system is a trait of screen locker ransomware virus. The D2+D virus aims to trick victims into paying a ransom of $100 in Bitcoins so they can close the annoying program and restore encrypted files with a decryption key. In fact, D2+D virus only pretends to encrypt data but instead it only locks the screen trying to scare victims into paying the demanded fee. Find out how to deal with D2+D virus and remove it completely from the infected machine:
Manual Removal Guide
Recover Lost Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
The D2+D Virus Infection Flow
D2+D ransomware virus infects the PC via a malicious payload that lands on the system. The payload usually contains an executable file that triggers the malicious D2+D ransomware script. Upon infection, the D2+D virus can’t stay unnoticed as it loads a window that locks the PC screen. It contains a ransom note left by the culprits in which they urge victims to pay a ransom of $100 in Bitcoins (currently 0.04 BTC). What the whole message reads is:
WHAT THE HELL IS HAPPENING?
Your files are encrypted, you cannot close this progarm unless you have the key! This is a ransomware
What can i do?
You have to buy the key! don’t worry
Customers are treated well, we are reliable
Can you decrypt my files?
Yes, we can but we won’t do it
Enter the key yourself
You can check the F.A.Q in the link given below
http://bobdinh.hol.es
REMEMBER, THE TIME IS LIMITED you only have 3 day(s) to buy the key!
HOW TO PURCHASE?
Buy bitcoins and send to: DlEifiefiinn34n2i3 or buy me some cup of coffe or we could hang out together that is fine ! 🙂
don’t know how to create bitcoin account? check the F.A.Q or hang out with me!
[Send with love:] DlEifiefiinn34n2i3
Send 100$ worth of bitcoin, special offer: 50% discount for first 3 customers fot poor people offer: 90% off!!!
feel free to donate now: [Donate to D2+D ransom project now!!] button [Unlock now!]
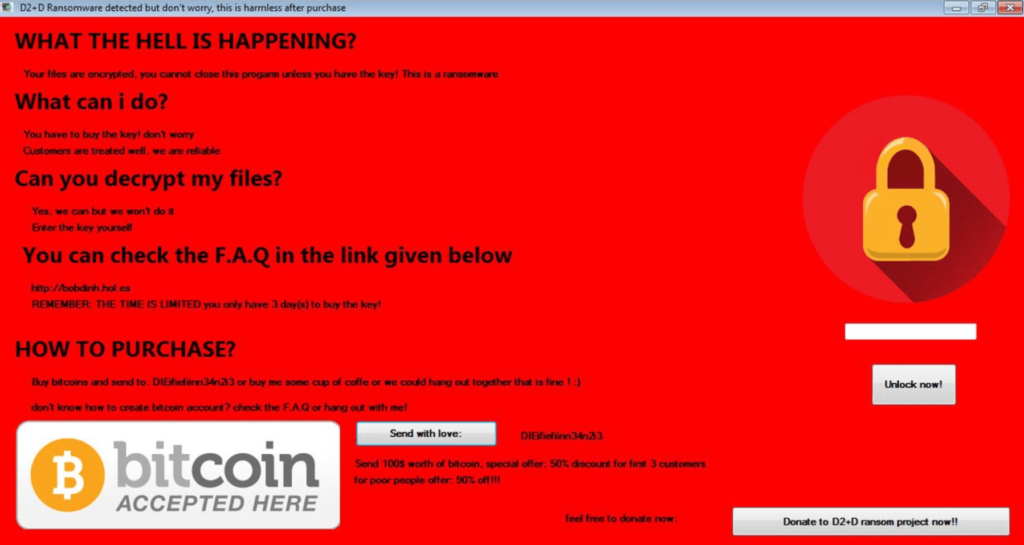
The good news is that D2+D crypto virus doesn’t encrypt any files but it only tries to trick victims into paying the ransom. The security researchers have cracked the D2+D ransomware code and let it out in public. Thus, it seems that when a victim of D2+D virus enters the password 215249148 in the indicated file, the monitor screen would unlock. However, the PC and all data stored on it continue to be at risk as long as D2+D virus files remain on the system. Furthermore, if the threat remains on the computer, it will appear each time the Windows is started due to registry modifications performed during the infection flow.
The complete removal of all malicious files and objects created by the D2+D virus is necessary as it will prevent the offensive window displayed by D2+D ransomware virus and protect data theft by crooks.
Ways of D2+D Virus Distribution
How can D2+D virus infection land on the PC? Cyber criminals may use several attack vectors for ransomware distribution. Commonly they choose to spread the malicious D2+D executable files via email campaigns. An attack email usually displays a link that may be embedded in a phrase, built-in a button or hidden in a picture. Now you may be wondering what could be wrong with such a link. Well, it may land you on a page crafted in a way to initiate an automatic download of malicious D2+D virus payloads on the PC. Some email campaigns are designed to mislead you to download and start a file attached to the email. Once you run the malicious file on the computer, it infects it and starts the D2+D infection. Another attack vector may be freeware bundling. This method allows hackers to hide the malicious D2+D payload in the installation setup of a freeware program so when you install it, you unnoticeably install the ransomware too.
Remove D2+D Ransomware Virus and Restore Your PC
WARNING! Manual removal of the D2+D ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
D2+D Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover Lost Files
WARNING! All files and objects associated with D2+D ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



