UPDATE! Zeus Virus has been associated with a tech support scam which is activated when you click on an infected website. Read further below for details.
Zeus trojan virus was first detected in July 2007. It’s main use is to steal information from the United States Department of Transportation. Zeus virus is also known under the names ZeuS and Zbot. It is part of one of the most successful botnet software in the world and from its first release till now Zeus has infected millions of machines. Furthermore, its code was used for other similar pieces of malware like Floki Bot. Zeus virus is a sophisticated threat that can cause massive damage to the computer and gain access to critical privacy data.
Manual Removal Guide
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Zeus Trojan Virus – Detailed Description
Zeus virus, also known as Zbot Trojan is a nasty malware that can perform various system modifications once it’s activated. It can be used to steal personally identifiable information as well as banking credentials, usernames and passwords for trading accounts, social networks accounts, and online payment accounts. Once Zeus virus gathers the information, it can employ remote commands and send it to its Command and Control server.
Zeus can also be dropped by Sundown or RIG exploit kits as a way of ransomware or other malware distribution.
Computers that are running different Microsoft Windows versions are primarily affected by Zeus Trojan. However, security researchers have found some new versions of the malware on Android, BlackBerry and Symbian devices. Zeus has evolved over time and currently it continues to be used in various attack campaigns.
Traits of Zeus Trojan Virus Infection
Let’s reveal some technical consequences of Zeus infection. The location it chooses for its installation is determined by the account level privileges of the logged-in user at the time of the attack. When it accesses the admin user profile it places the files in the %System% folder or else the files are copied to %UserProfile%\Application Data. The files may set the HIDDEN attribute that will hide them from casual inspection.
The executable file that triggers Zeus virus may vary. Past records of its samples reveal the usage of following file names:
- twext.exe
- sdra64.exe
- ntos.exe
- oembios.exe
- pdfupd.exe
Latest payloads of ZeuS Chthonic variant are detected using the malicious executable file 73mendjd.exe.
The Zeus trojan virus can further inject itself into currently running services like winlogon.exe and explorer.exe (depending on the user account privileges). It can also compromise the svchost.exe service which will later allow it to steal banking information.
The Zeus malware is notable for enforcing a stealth detection module. It is able to detect if there are any sandbox or debug environments active on the infected host. If such are detected or an anti-virus product is found, then the Zeus trojan virus automatically deletes itself to prevent detection. This is done by checking the installed programs, folders and Windows registry for the following strings: AntivirusProduct (generic identifier), McAfee, Symantec, Norton, Kaspersky, Avast and “antivirus”. The malicious engine has been found to take over process ownership and modify the anti-virus real time engines or configuration files. Some viruses have also been found to even hijack the anti-virus products and remove them entirely. In other cases they are are disabled but still present on the machines. The false sense of security is essential to some attack campaigns.
Detailed information about the infected systems is harvested during the first stages of Zeus trojan virus infections: detailed running process data, hardware information, active name, operating system information and configuration values.
The advanced Zeus trojan virus samples actively communicate with the hackers via specially created C&C servers. Depending on the strain the traffic may be encrypted or routed through hacker-controlled gateways and proxies. The Zeus virus engine can launch commands and execute actions ordered by the hackers at will.
Possible consequences of an infection include also the modification of files, the creation of new data, connection to hardware and misconfiguration of attached devices.
Infected users who are using an account with Administrator rights may witness the presence of the following files created in the following directories:
- %systemroot%\system32\sdra64.exe (the malware)
- %systemroot%\system32\lowsec
- %systemroot%\system32\lowsec\user.ds
- %systemroot%\system32\lowsec\user.ds.lll
- %systemroot%\system32\lowsec\local.ds
Victims who are using an account without Administrator rights may check for the following malicious files:
- %appdata%\sdra64.exe
- %appdata%\lowsec
- %appdata%\lowsec\local.ds
- %appdata%\lowsec\user.ds
- %appdata%\lowsec\user.ds.lll
Additionally, Zeus virus adds registry keys that allow it starts on every Windows boot-up. The modifications again depend on the account privileges. If the account has administrative privileges, Zeus uses the subkey:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\
When the account has limited privileges, Zeus uses the subkey:
HKEY_CURRENT_USER\ SOFTWARE \Microsoft\Windows\CurrentVersion\Run\
Zeus trojan virus can also be used as part of a toolkit. In this case, the attacker can establish a connection with his command and control server and control the Trojan’s malicious actions. So it can shut down or reboot the computer, download and execute further files, or even delete system files which may cause permanent system damage.
Chthonic Trojan Is the Latest Zeus Version
Zeus Trojan has evolved over time and there are many variants of the threat. The latest version of Zeus virus is called Chthonic. It was used in a large-scale attack against 150 banks in 15 countries back in 2015. The malicious Chthonic code is able to insert itself into the msiexec.exe process. Once this happens, it installs various malicious modules on the infected computer. These modules can collect system information, steal passwords that have been saved, record log keystrokes, enable remote access and then send the data to crooks command and control servers.
Zeus Trojan Virus – Distribution
Zeus virus infects victims’ machines via several techniques. It is mainly spread through phishing schemes and drive-by-download attacks. Phishing schemes often guide users to enter a fake website that is much similar to the legitimate one. Typically spam emails, instant messages on social networks and pop-up messages are used to exploit the weaknesses in current web and PC security.
The spam emails may spoof you claiming that the message is sent by any social website, bank, IT administrator, online payment service, Microsoft, PayPal, etc. Any interaction with the presented content in the email may redirect you to a website infected with malware. The result will be a stealth download of the malicious Zeus Trojan virus on your computer.

Last year we reported several techniques used to spread Zeus virus. At the end of July, PayPal spam email campaigns were spreading Chthonic – the latest Zeus virus variant. After that in October MSG images were also employed by hackers as a way to infect users with the devastating Zeus Trojan.
The customized spam emails may also have an attached file that is designed to exploit specified vulnerabilities in any installed app or the Windows OS. The crafted file can trigger a Zeus infection once it is opened.
Security Tip: Whenever you are wondering whether to act further with suspicious content (such as links, attachments, etc.), you can use online malware scanning services like VirusTotal and ZipeZip. They will analyze the component and provide information about its security status. The usage of such services will help you prevent eventual infections with Zeus and other malware.
UPDATE! We have just encountered traits of Zeus being used in a tech support scam. You may run into Zeus virus now by clicking on a website which has been injected with a script leading to a tech support scam. In case a message shows up on your screen stating that you should call Microsoft Technical Department, do have in mind that Microsoft does not make unsolicited phone calls to help you fix your computer. You may also receive a message stating the following:
*****************************************
RDN/YahLover.worm!055BCCAC9FEC Infection
*****************************************
Windows Defender Alert: Zeus Virus Detected In Your Computer
!!
Please Do Not Shut Down or Reset Your Computer.
The following data will be compromised if you continue:
1. Passwords
2. Browser History
3. Credit Card Information
4. Local Hard Disk Files.
This virus is well known for complete identity and credit theft. Further action through this computer or any computer on the network will reveal private information and involve serious risks.
Call Microsoft Technical Department: (888) 359-4379 (Toll Free)
Keep in mind that this message is also part of the scam campaign with Zeus virus.
The Zeus Trojan is also being delivered in an ongoing wave that poses as a pending invoice. The attackers send out template messsages that attempt to lure the targets into downloading an infected attachment. The files are randomly named and all follow a template naming scheme: INVOICE-
Dear Sir,
Please kindly view the attached invoice and cross check with your accounts to clarify if we still have some pending balance to pay you as our side is clear.
We want to make new order, so check and let revert back please.
Regards,
Yusuf REZAQ
Chief Accountant
PACIFIC PIPES CO., LTD
skype y90-rezaq
Tell: +86738899377
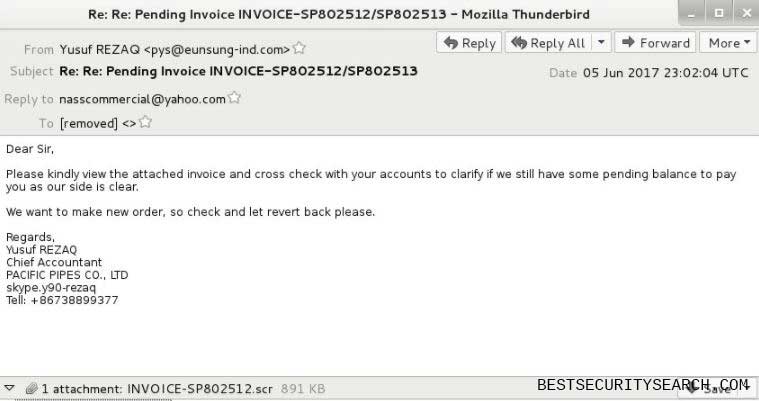
The invoice file is a hidden binary executable file that serves as a payload downloader for the Zeus virus threat.
Remove Zeus Trojan Virus from Windows PC
Zeus Trojan virus is not easy to remove. Its manual removal can be challenging even for the tech savvy guys. However, there is no doubt that you should delete the threat as soon as possible from your computer. Otherwise, your sensitive data, the whole system as well as other computer systems are exposed to a serious risk of Zeus infection. Security specialists recommend the usage of an anti-malware tool for the best removal results.
WARNING! Manual removal of the Zeus trojan virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Prevention is Better Than Cure
Make sure that your operating system, as well as any installed software, is fully patched. You can select the automatic update preferences if they are available. Do also a check of your antivirus and firewall software and update them if there are any recent updates. Otherwise, you left your computer vulnerable to Zeus Trojan attacks.
Zeus Trojan Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help



