YOUR COMPUTER HAS BEEN BLOCKED
Error # 268D3
Please call us immediately at: …
Have you ever had the “Your (Windows) Computer Has Been Blocked” message on your screen? Typically, this message means your system has been infected by a virus that in most cases is a tech support scam or ransomware. Read further to learn how you probably got infected and how to remove “Your (Windows) Computer Has Been Blocked” virus.
Manual Removal Guide
Recover Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
More About the Your Computer Has Been Blocked Virus
Your Computer Has Been Blocked message is a sure sign of a virus infection. This message can be placed in a notification window or a pop-up and often can be accompanied by different extortion strategies, some of them include the following:
- Social Engineering Scams – Hackers try to trick the users into various financial scams by pretending to be law enforcement agencies or other high-profile government or private institutions.
- Infection Explanation – Other threats go straight to the point and inform the computer users that they have been the victim of a hacker attack. And even though the machine has been severely compromised, the hackers often lure the victims downloading counterfeit anti-virus tools or “fixes” that place additional malware on the compromised machines.
- Technical Support Scam – One popular message used by scammers is that there’s something wrong with the operating system of the computer. Read our in-depth guide Tech Support Scammers – Tricks and Protection.
Common “Your Computer Has Been Blocked” Virus Cases
Commonly tech support scams are the reason of the message “Your Computer Has Been Blocked” to be displayed on your screen. The message can appear while you are browsing as a new website page. It can also occur in the form of a system notification, an error or a pop-up message. In some cases, the “Your Computer Has Been Blocked” virus message can lock your browser or computer screen convincing you that the only way to fix the problem is to contact Microsoft or another well-known company by calling a support telephone number.
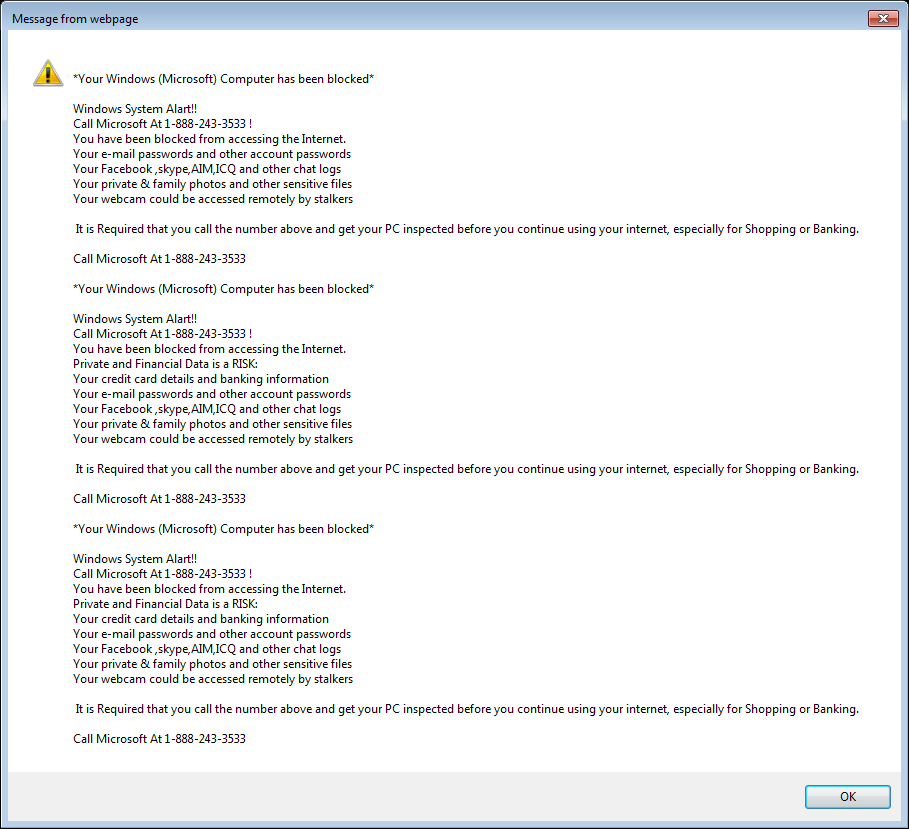
One of the more popular tech support scams masks itself as a service of Microsoft. The scammers urge you to call the 1-888-243-3533 number. This seems like a low-effort attempt, as the scam doesn’t use the slick Microsoft interface. Instead, the message appears in the form similar to that of an error:
Microsoft is a worldwide company, and they don’t have a tech-support hotline. It would cost a lot of money to reach them in that way. It’s the reason why the official company avoids the service and the scammers who mask themselves as Microsoft love it.
Here’s the full text of the scam:
*Your Windows (Microsoft) Computer has been blocked*
Windows System Alert!!
Call Microsoft At 1-888-243-3533 !
You have been blocked from accessing the Internet.
Your e-mail passwords and other account passwords
Your Facebook ,skype,AIM,ICQ and other chat logs
Your private & family photos and other sensitive filesYour webcam could be accessed remotely by stalkers
It is Required that you call the number above and get your PC inspected before you continue using your internet, especially for Shopping or Banking.
Call Microsoft At 1-888-243-3533
This message will remain on your computer no matter how many times you try to close it or stop it from the Task Manager. The “error” is due to the scammers accessing your Windows Registry and editing your computer, so it automatically reloads the scam.
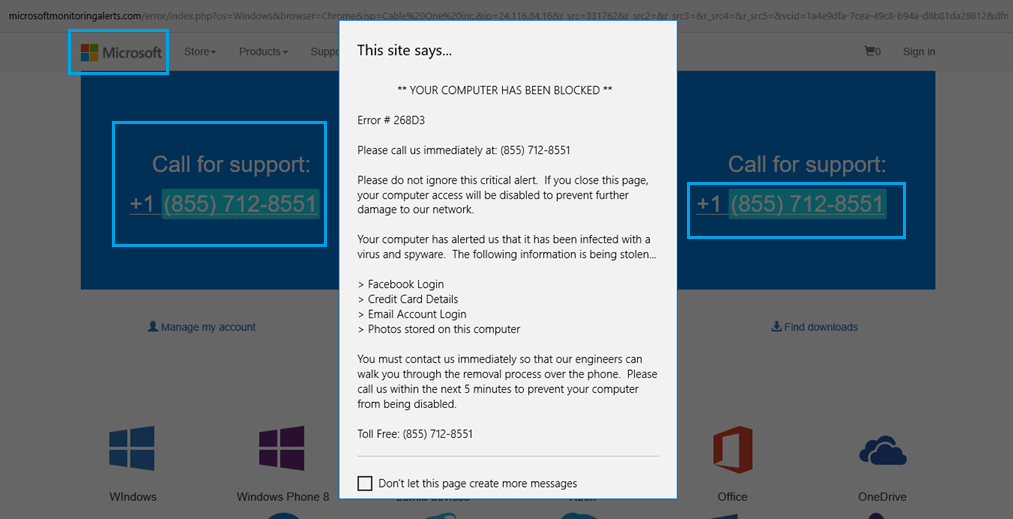
Error #268D3 (1-855-712-8551) is yet another tech support scam that is impersonating Microsoft Company. The scammers can try to call you using the number. You’re also likely to experience redirects and other difficulties while using your browser.
The scam uses a page that looks uncannily similar to the Microsoft’s main site. The page claims that the featured number is toll-free and that it connects you with a Microsoft tech support specialist.
In addition to tech support scams, ransomware viruses also use the same message after they lock your PC.. Some of them are scareware viruses – they don’t encrypt data but only try to trick victims into paying a ransom. A typical example is the Cockblocker ransomware.
How Viruses with “Your Computer Has Been Blocked” Message Are Distributed
Hackers use several methods to distribute viruses that display “Your Computer Has Been Blocked” message. Most of the installations occur through software bundles downloaded from the Internet. Computer users typically download “free” or “trial” versions of popular products from untrusted sites or P2P networks. Many of these files are actually infected files or even counterfeit programs that might imitate the real software packages. Depending on the case the user might not be able to actually install a piece of software or get a trial version. In either case, the malware has already infected the computer as it has been bundled with the program, installer or both.
Malvertising is the other primary distribution method of such malware threats. Malicious ads are often served on hacked sites or spam networks that the criminal users operate. Browser Hijackers and various adware toolbars are also responsible for a significant number of infections. If you have been the victim of a browser hijacker you browse our catalog of removal instructions here.
Consequences of the Your Computer Has Been Blocked Infections
When you see the Your Computer Has Been Blocked message then you are most likely infected with one or several malware strains. This is a cause for worry as the potential damage can be inflicted in several different vectors. Usually, the features of the malware include several damage-inflicting techniques:
- Spying of users – Most malware contain code that spies on the infected users by transferring their valuable data to remote malicious servers that are operated by the attackers. This may include sensitive personal information such as account passwords, confidential documents, photographs, personal photos and videos and other types of user data. Most browser hijackers also retrieve and send the browsing history, cookies, stored passwords and other information retrieved from the Internet browsers installed on the local computers. Malware also collect data such as geolocation, language settings, system data and other information that can create profiles of the victims.
- Remote Access Control – Some contemporary malware threats include Trojans that allow the hackers to attain full remote control access to the infected machines. This is a very dangerous circumstance as it allows the criminals to view what the users do while they work on the computer.
- Installation of Target Ads in the Infected Browsers – This tactic is especially popular with browser hijackers. The malware installs custom sponsored ads that generate income for the hackers when they are clicked on by the user. In several instances, these ads replace legitimate links when search engine queries are entered.
How to Prevent Your Computer Has Been Blocked Virus Infection
There are several ways used to prevent malware installations that lead to “Your (Windows) Computer Has Been Blocked” notifications and pop-ups:
- Check Installation Options of Software – When computer users install various products from untrusted sources, it is imperative that they always check all the options. Malware bundles that could lead to infections may be turned off in some instances by unchecking various tick boxes and toggles, often found in tabs labeled as “Advanced” or “Custom” settings. All programs should always be downloaded from official sources to prevent such threats from infecting computers.
- Follow Good Security Rules – Computer users need to be educated to use restricted accounts that prevent them from installing dangerous software by accident. Most hackers assume that home users use open accounts and use social engineering tricks to install malware. If the users run accounts with restricted access, then in many cases the installation attempts will fail.
- Use Trusted and Proven Anti-Spyware Software – Prevention is the best cure. If you would like to defend yourself from malware threats of any type, or are a victim, then you can use a trusted anti-spyware tool that has proven its effects.
All these pop-ups that state “YOUR (MICROSOFT) COMPUTER HAS BEEN BLOCKED” present false virus warnings sometimes accompanied by audio that repeats endlessly. Even though the message is trying to make you believe that your PC is full of errors that can be fixed only by Microsoft Tech agents who you should contact at provided tech support number, we want to remind you that Microsoft doesn’t offer such option so you should never call these numbers.
How to Remove Your Computer Has Been Blocked
WARNING! Manual removal of Your Computer Has Been Blocked virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Your Computer Has Been Blocked Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover Files
WARNING! All files and objects associated with Your Computer Has Been Blocked virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



