May ransomware virus targets predefined data and upon infection encrypts them with strong cipher algorithm. All corrupted files receive the malicious extension .maysomware at the end of their names. The .maysomware virus files cannot be accessed by any app except the unique decryption software possessed by culprits. They attempt to extort from victims a ransom payment of 1.5 BTC for the decryption of the .maysomware file.
Manual Removal Guide
Recover .maysomware Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How May Ransomware Virus Harms the PC
May ransomware virus is a data locker type of malware that transforms certain data and renders it unusable. So once the malicious payload that starts the infection process is running on the computer, May virus occupies the system and performs various modifications.
It all begins with a file named May.exe sometimes May_ransomware.exe running on the computer. However, if you choose to remove May virus manually, have in mind that the threat creates and drops new malicious files and then deletes the initial infection file making its detection harder. It could even hide its malicious files in legal processes that are currently running on the system. Some files created by May ransomware virus are likely to be dropped in Windows folders:
%USERPROFILE%
%APPDATA%
The next infection stage is a scanning process of all computer drives in search of target file types that May virus aims to encrypt. For the encryption, May ransomware virus is believed to utilize a combination of two strong algorithms – AES-256 and RSA-4096. During the encoding process, May virus is supposed to encrypt images, videos, documents, text files, archives, configuration files, databases and other. Upon encryption, May crypto virus generates unique decryption key that unlocks all enciphered files. They all have appended the malicious file extension .maysomware and their original names may be transformed into a random string of symbols. We do not recommend victims to pay the ransom as there is no guarantee that crooks will send the decryption key as it could be broken or missing at all.
How much is the ransom? It is 1.5 BTC which currently equals to 3289.38 US Dollars. For the final infection stage cyber criminals have created a file called Restore_maysomware_files.html which is dropped on every infected system. The malicious source code of May ransomware virus is designed to modify Windows registry keys and sub keys so the file Restore_maysomware_files.html gets displayed automatically on victims’ screens. The file contains a ransom message that guides victims how to act further to receive the decryption key. What the ransom note of May ransomware virus reads is:
RANSOMWARE
All your files have been encrypted with May Ransomware. For encrypt we use AES256+RSA4096. You have 5 days for decrypt your files. Don`t try recover your files.
Decrypt Manual
1) Make your bitcoin wallet on block.io or blockchain.info and buy 1,5 bitcoins on BTC Exchange Sites (https://goo.gl/1PE96T)
2) Send 1,5 bitcoin to adress 3Gw6b57A3E34nAph3mzGbKAj8sTSgD8GP9
3) Write to us on email [email protected]. In subject write this identificator *****
4) After receive bitcoins and your email, we contact with you.
— YOU MIGHT DECRYPT 2 FILES FOR FREE. Send it to email [email protected]. In Subject, write your UNIQUE Identificator.
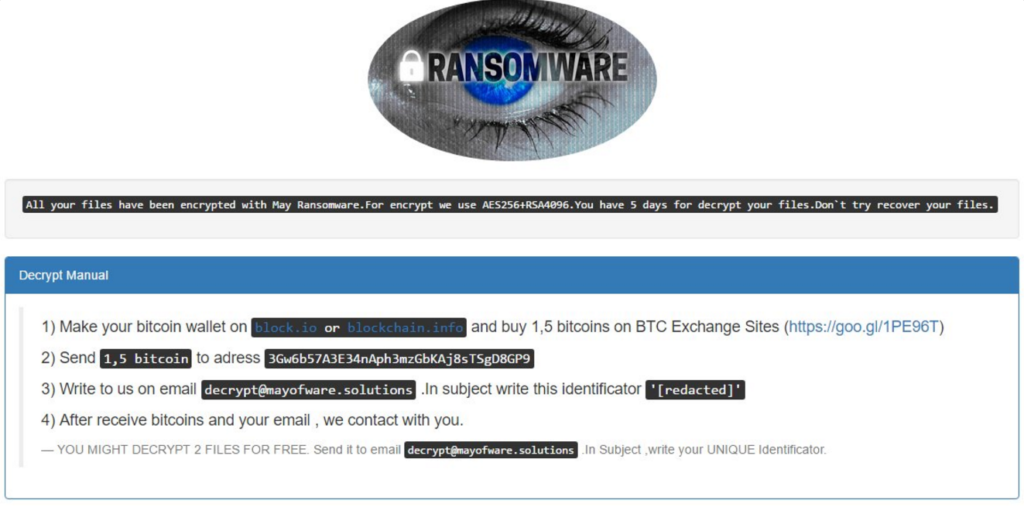
To make it even more urgent culprits give five days for the ransom amount transaction with no information what they plan when that period expires. In any cases, it is better to avoid contacting them at the shown email and remove May ransomware virus by following the guide below. Once you remove completely the virus, there is a chance to restore .maysomware files with the help of alternative data recovery tools.
The Shadow Explorer method will not be working in this case because May ransomware virus uses the Command Prompt to write the command line:
vssadmin delete shadows /all /quiet
By doing this, it removes all shadow volume copies stored on the infected PC, and they are no longer accessible by Shadow Explorer software. However, there are other ways to recover .maysomware files. Some of them are also included in the consistent step-by-step removal guide below.
How May Ransomware Virus Lands on the PC
The May ransomware payload may be hidden in a file attached to a spam email that seems totally legit. It may also be integrated into a website that once entered starts an automatic download of the payload. So again a spam email or a message on the social media or an ad may present you the malicious link that infects the PC with May crypto virus. In some cases, crooks may bundle May.exe with the installation package of a freeware program.
Related: OnyonLock Ransomware Virus
Remove May Ransomware Virus and Restore Encrypted Files
WARNING! Manual removal of the May ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
May Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover .maysomware Files
WARNING! All files and objects associated with May ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



