The GPUChanger ransomware virus is a counterfeit system utility that is being distributed by computer hackers worldwide. The malware is able to conduct many dangerous activities on the infected machines. The victims can remove the GPUChanger virus by using one of the following methods:
Once GPUChanger virus is removed successfully you can try to restore your corrupted files following our instructions below.
DOWNLOAD GPUChanger Removal Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
GPUChanger Ransomware Virus Description – Effects On The System
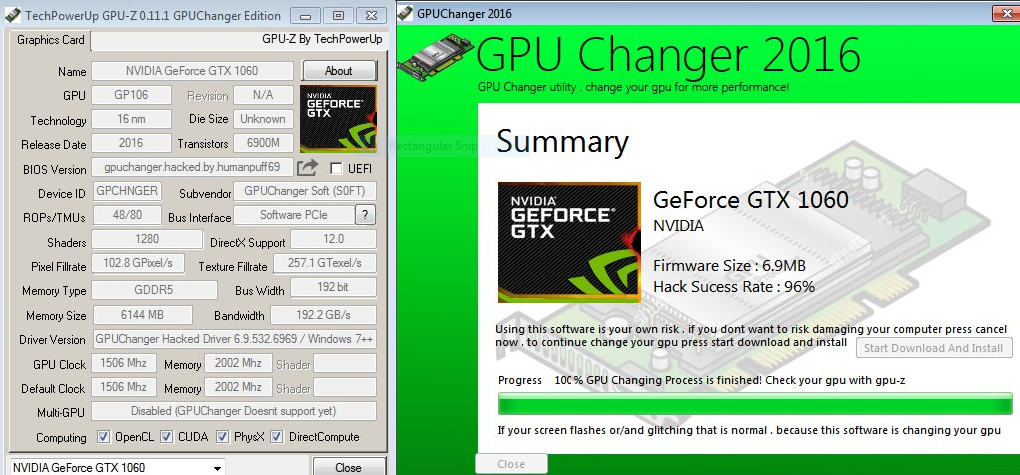
GPUChanger Virus is a fake system utility that poses as a useful video card performance tuner. The malware is made to look like popular freeware system utilities that display hardware components data and fine tune the performane of the computers.
The GpuChanger virus can cause all types of damage to the affected computers. The infected hosts all have their sensitive data downloaded by the engine – both hardware and user information. GpuChanger virus’ functions are similar to computer worms that have the ability to propagate across the operating system, applications and user data. We assume that other malicious modules are also included:
- Additional Payload Delivery – The GPUChanger ransomware virus is able to download additional threats to the infected computers.
- System Harvesting – In-depth system information can be performed by the virus. The hackers can modify the binaries so that the virus can harvest account credentials, passwords and sensitive files similar to browser hijackers.
- System Modification – The application can modify the compromised machines and cause performance issues and Windows boot errors.
GPUChanger ransomware includes a popular freeware utility called GPU-Z that shows detailed information about the graphics card. The computer hackers behind it bundle the application in the core threat to fool the victims into thinking that the GPUChanger malware. The computer users can easily remove the GPUChanger virus by following our in-depth instructions.
GPUChanger Ransomware Virus Distribution Tactics
GPUChanger virus can be distributed via different methods depending on the hackers campaign. At the moment the number of captured samples is relatively low. This does not give a clear indication of the main strategy that the hackers are using.
One of them is the use of email spam messages. They use social engineering tricks that attempt to make the victims infect themselves with the GPUChanger virus. The binary files associated with it can be attached directly to the messages or linked in the body contents.
Infected office documents that resemble files of user interest such as invoices and letters. Once the users open them a notification prompt appears which asks them to enable the built-in macros. If this is done the GPUChanger ransomware virus is downloaded to the victim computer and the infection begins.
Another source is through payload droppers and browser hijackers. They not only deliver the GPUChanger ransomware virus to the target system but also modify the operating system. The malicious browser add-ons, also known as hijackers, also modify the settings of the applications to redirect to a hacker-cotrolled site. They change the default home page, search engine and new tabs page. Upon infection they can also extract sensitive data such as stored form data, cookies, history, account credentials and settings.
Related: Crypto-Blocker Ransomware Virus
Remove GPUChanger Ransomware Virus and Restore Encrypted Files
WARNING! Manual removal of the GPUChanger virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
GPUChanger Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover Affected Files
WARNING! All files and objects associated with GPUChanger virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



