Crypto-Blocker ransomware virus is a dangerous malware which encrypts user files and uses a non-orthodox payment scheme. Upon infection it starts its encryption engine which processes target user data and marks it with the .corrupted file extension. Users can follow our in-depth removal guide to delete active infections and prevent future intrusion attempts. There are two methods of removal and recovery:
DOWNLOAD CRYPTO-BLOCKER RANSOMWARE VIRUS REMOVAL TOOL.
You can then follow the steps below to restore your files.
How Can Crypto-Blocker Virus Infiltrate the PC?
The captured malware samples show that the Crypto-Blocker ransomware has been distributed as a single binary file called Crypto-Blocker.exe. The attack campaign that has been observed to carry the Crypto-Blocker ransomware virus has found that the operators target hosts all over the world. As the malware samples are of a small quantity there are several possible ways of distribution. The most popular ones include the following:
- Email Spam Messages – Crypto-Blocker ransomware virus is distributed in spam email messages that use social engineering tricks. They attempt to trick the targets into thinking that the sent messages come from legitimate companies or institutions. The contents either makes them download an attached file (which contains the virus) or click on a link that redirects to the malware binary.
- Infected Documents – One of the trends in the last few months is the use of malicious office documents. They are often found in email spam messages or download sites and pose as files of user interest. When the targets open them a notification prompt asks them to enable the built-in scripts. If this is done the virus is downloaded from a remote server and executed thus triggering the infection. An example of a large-scale infected documents attack is the massive South Korean campaign.
- Infected Software Installers – The Crypto-Blocker ransomware virus can be bundled in malicious software installers. Hackers usually download popular legitimate software installers and include the malicious code. The modified files are then distributed on hacker-controlled sites and P2P networks like BitTorrent.
- Hacker-Controlled Sites and BitTorrent Trackers – The virus binary alone or infected documents/installers can be distributed on various hacked or hacker-controlled sites. P2P networks like BitTorrent are another popular place for distributing the Crypto-Blocker ransomware virus samples.
- Browser Hijackers and Redirects – Malicious browser extensions made by criminals and site redirects can infect target machines with the Crypto-Blocker ransomware virus. The hijackers pose as useful toolbars or scripts that add functionality to the installed web browsers and are usually made for the most popular ones: Safari, Google Chrome, Mozilla Firefox, Microsoft Edge and Internet Explorer. Upon installation they change important settings such as the default home page, default search engine and new tabs page. In addition it harvests stored data such as cookies, history, stored account credentials, form data and the bookmarks.
- Direct Hacker Intrusion Attempts – Crypto-Blocker ransomware virus can be installed through direct hacker intrusion attempts. They are usually done by targeting older software installations with special hacker tools.
Crypto-Blocker Virus – Ransomware Features
Malware research shows that one of the latest threats that have been discovered is the Crypto-Blocker ransomware virus. During the initial security analysis the researchers were not able to find a connection between this virus and the other famous malware families. This means that this is a original virus made by the hackers.
When the Crypto-Blocker ransomware virus infects the target host, the malicious engine starts the encryption process. It uses a predefined list of file type extensions, depending on the configuration it may target a lot of files: music, photos, videos, databases, configuration files, archives, backups and etc. All affected data receive the .corrupted extension.
When the encryption process is complete the Crypto-Blocker ransomware virus launches a lockscreen application frame that prevents ordinary computer interaction. It also severely limits the computer victims in removing the virus manually without the use of a quality anti-malware solution. It is named “CRYPTO-BLOCKER ENCRYPT YOUR FILES” and reads the following message:
CRYPTO-BLOCKER ENCRYPT YOUR FILES !
Hello, User_name
This is the hacker company, we encrypt all your personal files (OS, Documents, Images,…)
This program is actually a ransomware, you’ve been hacked !
If you want to keep your PC alive, please pay 10 (dollars, euros, pounds, you choose the money type)
After paying, get your decryption key, this virus close by itself.
If you didnt pay after 5 hours then… your PC will crash or maybe unusable.
YOU HAVE 5 HOURS !
Type code here:
button [Pay]
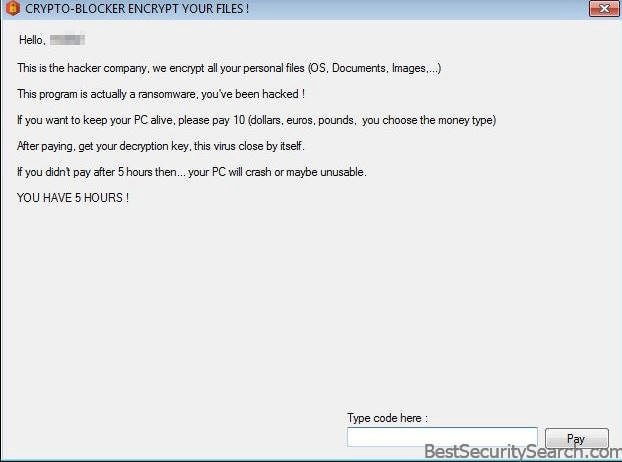
We can see that the hackers behind the the Crypto-Blocker ransomware virus have not specified a way to contact them. This likely means that the threat is still under development and that the released malware samples constitute test versions of it. The ransomware note follows the typical tradition of extorting the victims for a payment. The hackers promise that they will remove the virus and restore the files if the sum of 10 Dollars (or Euros/Pounds/another currency) is provided to them. As always this is a scam and users should only use a quality anti-spyware program to effectively remove the Crypto-Blocker ransomware virus code.
A time limit is also imposed on the victims which places further pressure on them to pay the sum to the hackers.
Crypto-Blocker Ransomware Virus Removal
Once you’re done with the removal process, there are some alternative data recovery solutions may help to restore sensitive .corrupted files. OK, let’s begin..
Ransomware Removal Steps
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Crypto-Blocker Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



