An infection with the dangerous ExecutiveProduct leads to serious security issues. Victims can restore and protect their computers by following our complete removal guide.
Remove ExecutiveProduct and Secure macOS
ExecutiveProduct Manual Removal Guide
Skip all steps and download anti-malware tool that will safely scan and clean your Mac.
Run a free scan and check if your Mac is infected with malware.
SpyHunter for Mac Scanner feature is free. Other features are paid. Here you can review its EULA and Privacy Policy.
Distribution of ExecutiveProduct
ExecutiveProduct is a new malware that has been reported in various attacks worldwide. At the moment the security experts have not been able to identify a single tactic that is being used to infect the targets. We presume that the hackers are using several of the most important methods to carry out malicious campaigns.
A common way of setting browser hijacker attacks is the use of email spam messages. They may directly distribute malicious file attachments containing scripts that lead to an infection. Other cases can utilize complex social engineering tricks and hyperlinks that are specifically made to confuse the intended targets into infecting themselves. Two more scenarios that are used in combination with email messages rely on infected files used as payloads ‒ documents and software installers.
- Infected Software Installers ‒ The criminals craft malicious packages made out of legitimate software installers. They are taken from the official vendor download sites, modified, and then posted on online sites or attached (either as file attachments) or linked in the email messages.
- Infected Documents ‒ They represent dangerous files that usually come in the form of some of the most popular document types: rich text documents, spreadsheets, and databases. When the users open them up a notification prompt will ask them to enable the built-in scripts (macros). If this is done then the malware is installed on the victim computer.
The malware browser plugins can be uploaded to hacker-controlled sites and P2P networks like BitTorrent as well. The hacker operators frequently utilize template design, text, and images to create portals that look like legitimate download sources. They may also use domain names that are very similar to legitimate sites and advertise them via pop-ups or ad networks.
The browser hijacker code associated with the ExecutiveProduct can be found in numerous malware toolbars. They are usually made for the most popular web browsers: Mozilla Firefox, Google Chrome, Internet Explorer, Safari, Microsoft Edge. They can be distributed on such download sites or even on the browsers repositories (such as the Chrome Web Store for Google Chrome) using fake developer accounts.
Impact of ExecutiveProduct Mac PUP
The ExecutiveProduct virus as a dangerous PUP general category malware can lead to many malicious actions, many of them will be chosen depending on the individual characteristics of each machine. This means that at the start of the infections a data gathering operation will start, being able to steal user’s data, hijack operating system values and create a report of the installed hardware parts. All of this data can be processed by another component to create a unique ID for each compromised machine. Any stolen personal information can be used for identity and financial crimes.
The made system changes can be defined in several categories:
- Persistent Installation — The virus can edit the boot options and configuration to start the virus every time the computer is powered on. This action may additionally block access to the recovery boot options.
- Windows Registry Changes — Manipulations to values of programs and the operating system can lead to severe performance issues, the inability to start certain services, and other issues.
- Additional Infections — The ExecutiveProduct malware can be used to carry out other infections such as remote access Trojans or file-encrypting ransomware.
Remove ExecutiveProduct and Restore Mac
If your system is showing infection symptoms, you should definitely take action and remove ExecutiveProduct and related files from your macOS. The sooner the better! Below you can find our step-by-step Mac virus removal instructions that give you the opportunity to get rid of ExecutiveProduct either manually or automatically. If you don’t feel comfortable with manual instructions, download a reliable ExecutiveProduct removal tool that will scan your Mac system for malware and clean it safely for you. If any questions arise, or additional help is needed leave us a comment.
How to Remove ExecutiveProduct on a Mac Manually
Remove ExecutiveProduct and related files from OSX.
- 1. Force Quit all suspicious applications.
Go to the Apple menu in the upper-left corner of your screen and choose Force Quit option.
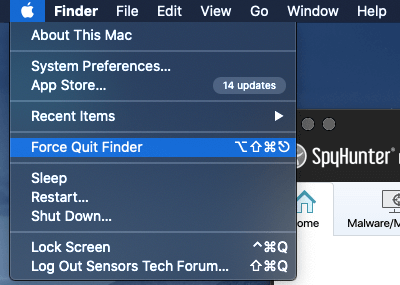
You will see a list of all currently running applications. Go find ExecutiveProduct, select it and then navigate to the “Force Quit” button. You can also find the last application you installed on your Mac and stop it as well.
Since software bundling is a common propagation method, the ExecutiveProduct may get installed along with the lastly installed application and their activities on the system may be related.
- 2. Remove ExecutiveProduct and other related potentially unwanted applications from the Applications folder.
Open the Finder and select the Applications menu. Then search for the unwanted application and drag it to the Trash.

- 3. Мanually look for ExecutiveProduct in the Libraries of your Mac.
WARNING! You are about to tamper with Library files on Mac. Make sure that you know the name of the virus file. Deleting the wrong file may cause irreversible damage to your MacOS.
Select Go from the top menu bar and navigate to Go to Folder…
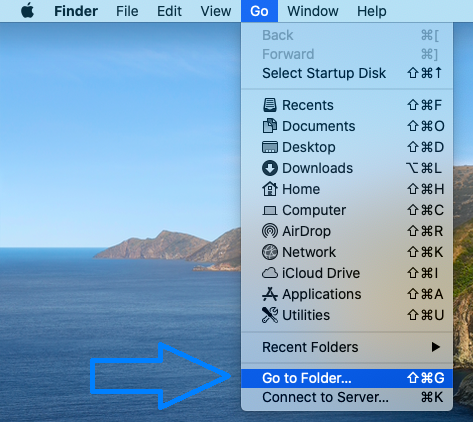
When the window appear start entering the following folder locations one by one:
/Library/Application Support
/Library/LaunchDaemons
~/Library/LaunchAgents
In each folder look for any recently-added suspicious files and move them to the Trash. Examples of files generated by adware:
- installmac.AppRemoval.plist
- myppes.download.plist
- mykotlerino.ltvbit.plist
- kuklorest.update.plist
Remove ExecutiveProduct From Your Browser
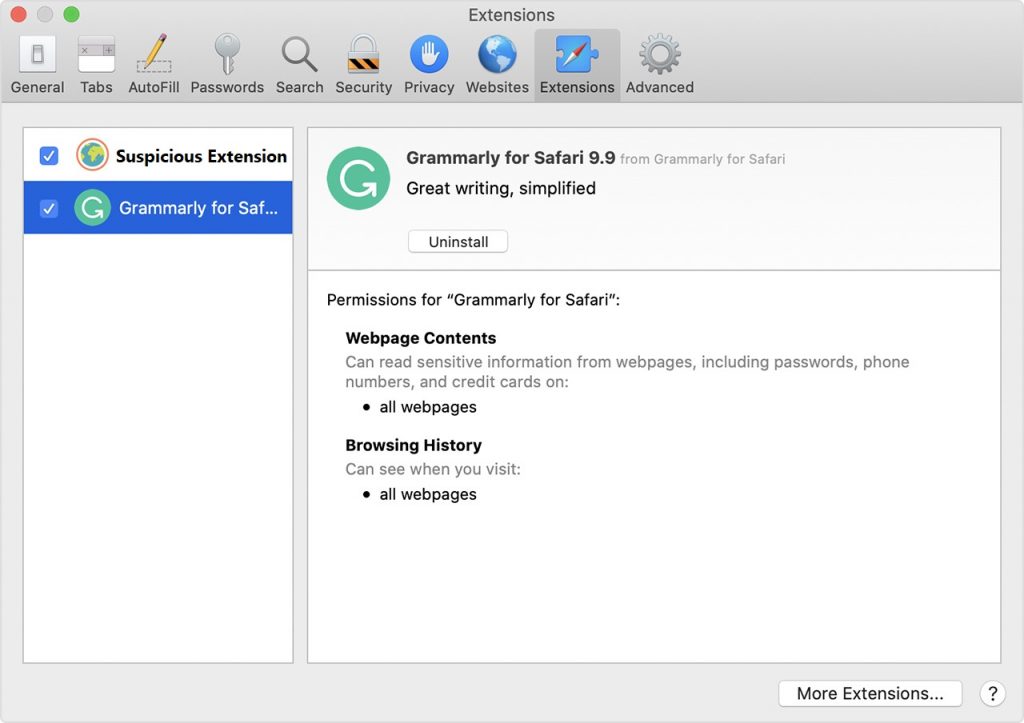
Remove suspicious browser extensions that can be responsible for the appearance of invasive pop-ups and browser redirects.
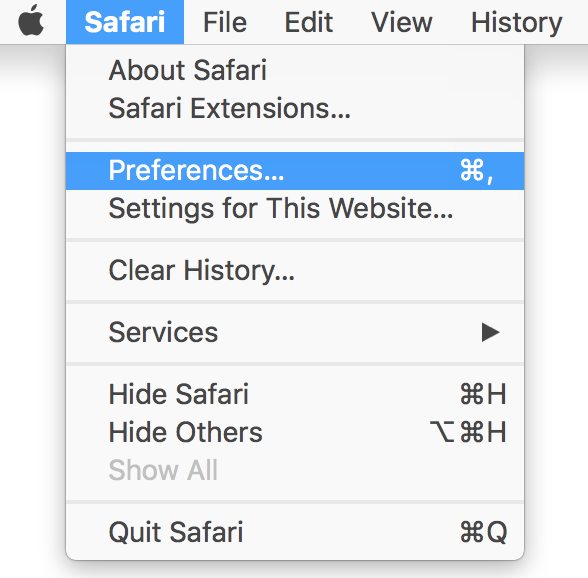
2. Click on the “Extensions” tab. If you see a suspicious or unwanted extension, select it and click “Uninstall“.
3. Reset Safari web browser. Beware that this step will remove the history as well as some of your saved data. Before you proceed we recommend that you make sure to write down all passwords, logins and important details.
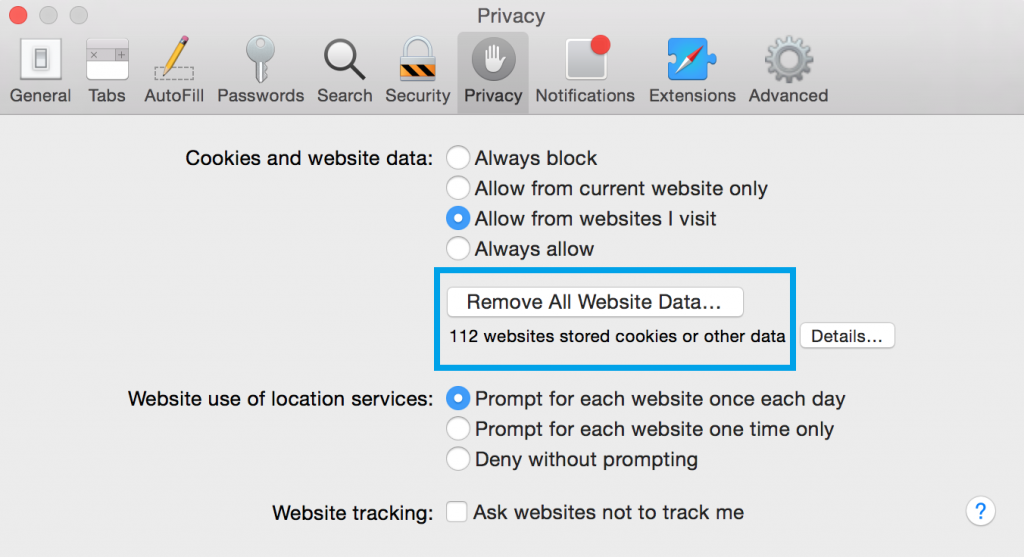
If you are using Safari version 9 or higher open the browser and go to “Preferences“. Then select the “Privacy” tab. When the window appears on screen click on the “Remove All Website Data” button.
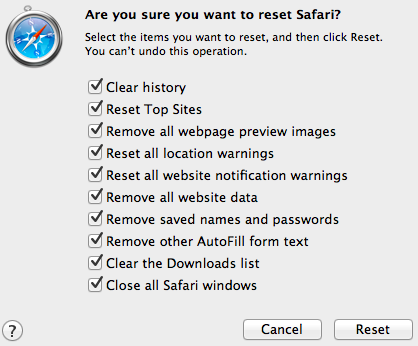
In case that your Safari web browser is running a version from 5 to 8, then just select Safari on the top menu bar and click on “Reset Safari” option. Choose which data to be cleaned from the browser.

2. Click “Extensions” in the left menu. Then click on the trash bin icon to remove the suspicious extension.

3. Again in the left menu, under Chrome, Click on “Settings“. Go under “On Startup” and set a new page.

4. Afterward, scroll down to “Search“, click on “Manage search engines“.

5. In the default search settings list, find the unknown search engine and click on “X“. Then select your search engine of choice and click “Make default“. When you are ready click “Done” button in the right bottom corner.
1. Start Mozilla Firefox. In the upper right corner, click on the Open menu icon and select “Add-ons“.

2. Inside the Add-ons Manager select “Extensions“. Search the list of extensions for suspicious entries. If you find any, select them and click “Remove“.

3. Click again on the Open menu icon, then click “Options“.

4. In the Options window, under “General” tab, click “Restore to Default“.

5. Select “Search” in the left menu, mark the unknown search engine and press “Remove”.

Remove ExecutiveProduct from a Mac Automatically
While the above steps work very well in most of the cases when users’ OSX is infected with PUP or malware, sometimes the Mac virus removal requires the help of a professional application. This anti-malware tool will scan and remove malware from your Mac. It offers an active protection shield and comes with a variety of handy features that will keep your system fast, clean, and secure.
DOWNLOAD Antivirus for MacSpyHunter for Mac Scanner feature is free. Other features are paid. Here you can review its EULA and Privacy Policy.



