BlueHowl ransomware virus is a newly discovered lockscreen ransomware that encrypts user and system data, as well as modifies essential Windows settings. To eliminated the threat victims can read our full BlueHowl removal guide that also includes detailed instructions on restoring the files the affected data using a professional data recovery software.
Manual Removal Guide
Recover BlueHowl Virus Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How Does BlueHowl Ransomware Virus Infiltrate the System?
The captured BlueHowl ransomware samples do not indicate the primary infection strategy. This means that the hackers can use different methods to spread it .
One of the primary tactics is the use of social engineering tricks via email messages. The hackers customize the contents so that they appear as being sent by legitimate companies or institutions. The payload may be either attached or linked in the body.
Infected office documents or software installers are another source of BlueHowl ransomware infections. They are created by the criminals and include scripts that automatically download the malware from a remote server in a compressed form and execute it. Such a delivery can sometimes evade anti-virus detection. This is the reason why we recommend the use of a quality anti-spyware solution that can prevent possible infections.
The criminals behind the BlueHowl ransomware can also opt to create and maintain malicious download sites or portals that resemble legitimate sources. All users of P2P networks like BitTorrent should be extra careful – BlueHowl virus and other ransomware are frequently masked as pirate content.
The criminals can opt to directly launch attacks against by attempting to find vulnerable programs. This is the reason why we recommend that all computer users update their operating system and installed applications.
Related: WannaCry Ransomware, Jaff Ransomware Virus
Infection Flow of BlueHowl Ransomware Virus
The BlueHowl virus is a new locksreen ransomware that has been detected in an ongoing attack wave. The security analysis shows that it is an independent creation as it signatures do not show any correlation with any of the famous malware families.
Upon infection with the BlueHowl virus it starts to execute several preliminary checks before proceeding with the encryption process. Other malware threats usually start the file modification module immediately without doing anything else. This threat however enforces several system changes to increase the inflicted damage on the compromised machines.
The following behavior patterns are linked with the initial infection:
- Process Information Query – The virus engine of the BlueHowl virus is able to query information related to the running processes. This can be done both for stealth protection purposes or for gathering values from running programs. The hackers can steal information by hooking to the running programs.
- Internet Cache Modification – The BlueHowl virus has a malicious engine that provides functionality that is similar to the infamous browser hijackers. Once installed the ransomware can query and modify the Internet cache. Such actions are done to hide the infection footprints or stealing account data, bookmarks and other user activity.
- System Information Harvesting – Upon infection unique machine information is harvested. This includes the active computer name, supported languages, the cryptograhic machine ID, Windows configuration files and etc.
- System Monitoring – The virus is able to monitor for any settings or registry changes. The malware can modify boot options, Windows settings and the registry to set up a persistent environment. The changes render manual removal impossible as Bluehowl virus can restore itself automatically. In these cases proper elimination of the malware can only be done using a quality anti-spyware solution.
- Network Communication – BlueHowl contacts the hacker-controlled servers to report the infection and may also send private information to the hackers. Some samples may even contain Trojan modules that can allow the criminals to take control over the infected machines.
- File Modification – The virus is able to mount partitions and attached removable storage devices, as well as delete files at will.
Once this is done the encryption process is started. BlueHowl virus starts to modify data based on a predefined list of file type extensions. It can be customized based on the attack campaign. In most cases ransomware such as this one seek to process as many file types as possible impacting documents, photos, music, archives, backup, databases and etc.
The BlueHowl virus is adept at spying on the user as it routes all network traffic through a hacker-controlled proxy server. Along with the harvested system and browser information this provides an opportunity for both data retrieval and identity theft.
A standard ransomware message is presented through a lockscreen – a software component that prohibits ordianry computer interaction until the malware is completely removed. The message reads the following:
You have 72 hours to recover your files!!!
If you don’t pay before 72 hours or you turn off this computer, the files will be delete.
If you wamt to recover your files, you have to pay 0.2 Bitcoin to this adress: 122iWPwDn2XbkSSs4g2usi1WuqyhzTKMo2
You will also pay with the QR code
You will receive a password to decrypt your files and you will recover your files
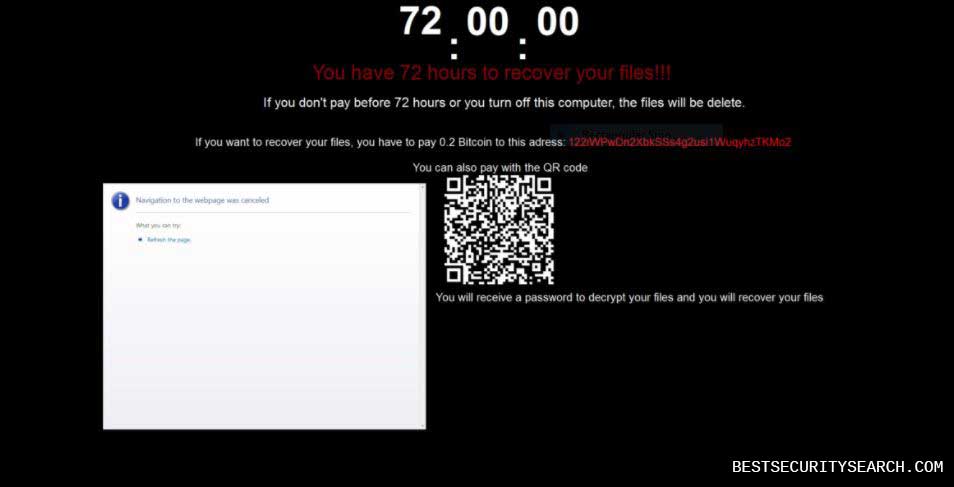
The hackers request that the victims pay them the sum of 0.2 Bitcoins which is about 510 US Dollars. All transactions done in the digital currency cannot be traced and can be quickly withdrawn by the recipients.
In addition the virus plays a Youtube video of “The Final Countdown” by Europe. An unusual characteristic of the virus is that it displays a QR code to redirect to the payment gateway. However the captured samples show an invalid code. We suspect that in future versions the virus will show a link to a site located on the TOR anonymous network.
Notice: The BlueHowl virus is a sophisticated ransomware that can be further modified to include even more modules.
Remove BlueHowl Virus and Restore Data
WARNING! Manual removal of BlueHowl Virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
BlueHowl Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover BlueHowl Virus Files
WARNING! All files and objects associated with BlueHowl Virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD BlueHowl Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



