The Nemesis ransomware is a new type of encrypting malware that uses the AES cipher to compromise valuable user data and extort the victims for a ransom payment. Our removal guide will show you how you can remove the existing infection from your computer and protect yourself in the future.
Manual Removal Guide
Recover Encrypted Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Nemesis Ransomware Description
Nemesis ransomware shares the same ransomware family as CryptON and X3M crypto viruses. It uses the typical infection patterns of a data locker ransomware by activating its encryption engine upon infection.
Once the malicious Nemesis ransomware payloads are on the computer, it initiates the infection process. The ransomware ensures its sustainable presence on the PC by creating files and accessing different system libraries that allow it to perform various functions. The Nemesis ransomware associated files may plague essential Windows OS folders like:
%AppData%
%Windows%
%Local%
%Roaming%
Afterward, it initiates scanning process and encrypts all files set as its target utilizing the AES-256 encryption algorithm. The encrypted files may be marked with malicious extensions that include hackers’ email and four or five randomly generated symbols at the end like .v8dp, .63vc4, etc. Viruses like this one usually target commonly used and important file types – various multimedia files (audio, video, and photos), backup images, configuration files, office documents and more.
Some of the captured samples were shown to encrypt a generic list of file type extensions. Depending on the infection it might target the following data:
PNG .PSD .PSPIMAGE .TGA .THM .TIF .TIFF .YUV .AI .EPS .PS .SVG .INDD .PCT .PDF .XLR .XLS .XLSX
.ACCDB .DB .DBF .MDB .PDB .SQL .APK .APP .BAT .CGI .COM .EXE .GADGET .JAR .PIF .WSF .DEM .GAM .NES
.ROM .SAV CAD Files .DWG .DXF GIS Files .GPX .KML .KMZ .ASP .ASPX .CER .CFM .CSR .CSS .HTM .HTML .JS
.JSP .PHP .RSS .XHTML. DOC .DOCX .LOG .MSG .ODT .PAGES .RTF .TEX .TXT .WPD .WPS .CSV .DAT .GED .KEY
.KEYCHAIN .PPS .PPT .PPTX ..INI .PRF Encoded Files .HQX .MIM .UUE .7Z .CBR .DEB .GZ .PKG .RAR .RPM
.SITX .TAR.GZ .ZIP .ZIPX .BIN .CUE .DMG .ISO .MDF .TOAST .VCD SDF .TAR .TAX2014 .TAX2015 .VCF
.XML Audio Files .AIF .IFF .M3U .M4A .MID .MP3 .MPA .WAV .WMA Video Files .3G2 .3GP .ASF .AVI .FLV
.M4V .MOV .MP4 .MPG .RM .SRT .SWF .VOB .WMV 3D .3DM .3DS .MAX .OBJ R.BMP .DDS .GIF .JPG ..CRX .PLUGIN
.FNT .FON .OTF .TTF .CAB .CPL .CUR .DESKTHEMEPACK .DLL .DMP .DRV .ICNS .ICO .LNK .SYS .CFG
Nemesis is also able to connect its remote command and control server to transfer the decryption key so that only crooks possess it and blackmail victims for a ransom payment. So after the encryption process, the threat is designed to drop a ransom note in a file called “### DECRYPT MY FILES ###.html” that is automatically displayed on the victim’s screen. The text is encouraging victims to pay the ransom for the decryption key and all it could read is:
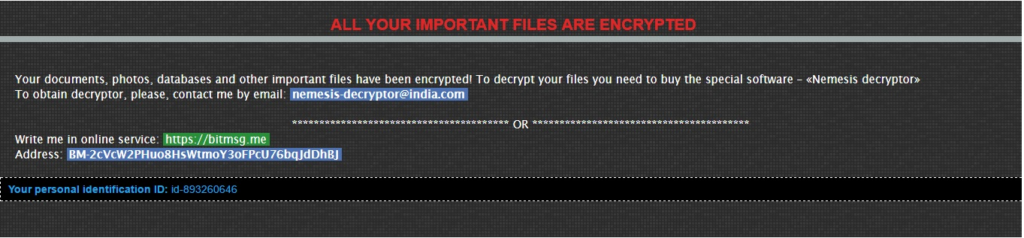
ALL YOUR IMPORTANT FILES ARE ENCRYPTED
Your documents, photos, databases and other important fíles have been encrypted! To decrypt your files you need to buy the special software – «Nemesis decrypt»
To obtain decryptor, please, contact me by email: [email protected]
********************OR******************
Write me in online Service: https://bitmsg.me
Address: BM-2cVcW2PHuo8HsWtmoY3oFPcU76bqJ*****
Your personál identification ID: id-8932*****
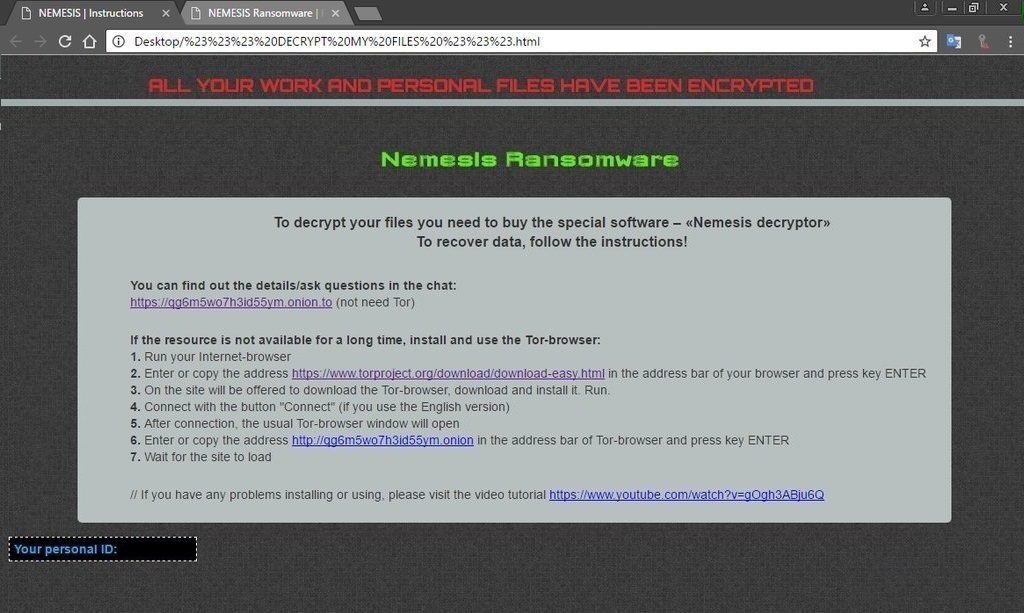
ALL YOUR WORK AND PERSONAL FILES HAVE BEEN ENCRYPTED
Nemesis Ransomware
To decrypt your files you need to buy the special software – «Nemesis decryptor»
To recover data, follow the instructions!
You can find out the details/ask questions in the chat:
h**ps://qg6m5wo7h3id55ym.onion.to (not need Tor)
If the resource is not available for a long time, install and use the Tor-browser:
1. Run your Internet-browser
2. Enter or copy the address hxxps://www.torproject.org/download/download-easy.html in the address bar of your browser and press key ENTER
3. On the site will be offered to download the Tor-browser, download and install it. Run.
4. Connect with the button “Connect” (if you use the English version)
5. After connection, the usual Tor-browser window will open
6. Enter or copy the address h**p://qg6m5wo7h3id55ym.onion in the address bar of Tor-browser and press key ENTER
7. Wait for the site to load
// If you have any problems installing or using, please visit the video tutorial h**ps://www.youtube.com/watch?v=gOgh3ABju6Q
The file could be found on the desktop as well as any other folder with encrypted files. Like other related threats, the Nemesis ransomware appends a unique victim id to every infected host. The ransom is demanded in Bitcoins, however, there is no specified amount.
The latest reports about the Nemesis ransomware reveal that the threat is likely to have a new variant that uses a long extension that contains several random hexadecimal characters and the .onion.to._ malicious extension at the end of the file name. Security researchers are currently investigating the ransomware samples so our advice is to save your encrypted data and wait for a possible breakthrough. Meanwhile, some alternative data recovery solutions may be of help to restore critical data – look at step six in the removal guide at the end.
Nemesis Ransomware CryptOn Strain Decryption Instructions
Several research reports indicate that a large amount of Nemesis ransomware strains have been found to be a variant of the CryptOn malware family. This allowed the specialists to create a special decryptor that may be used to restore the affected files. Note that this might not work in all cases. Our readers are advised to use a quality anti-spyware solution to remove the malicious components and afterwards use the decryptor to attempt to recover their files. Another alternative would be to use the data recovery software listed in our instructions below. You can download the decryptor by clicking here.
Nemesis Ransomware Distribution
The first Nemesis ransomware infections were reported by victims on January 8. It is not known which infection method is primarily used by its operators, however, we can assume that spam email campaigns and infected software bundles, as well as updates and games downloaded from hacked or malicious sites or BitTorrent peers, may be the primary medium. It appears that Nemesis ransomware primarily targets English-speaking users.
The email spam messages in most cases employ social engineering tricks. The aim of the criminals is to make the targets infect themselves with the malware by using templates that pose as legitimate companies. The Nemesis ransomware is usually attached or linked in the body contents.
Browser hijackers can also lead to a successful Nemesis ransomware infection as part of the initial attack. These malicious add-ons seek to change important settings of the most popular web browsers: Google Chrome, Microsoft Edge, Mozilla Firefox, Internet Explorer, Safari and Opera. The default search engine, new tabs page and search engine are changed to point to a hacker-specified address (usually a malicious portal) where the malware can be acquired.
Remove Nemesis Ransomware Virus and Restore Your PC
WARNING! Manual removal of the Nemesis ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Nemesis Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover Encrypted Files
WARNING! All files and objects associated with Nemesis ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD Nemesis Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



