The malicious extension .merry is associated with the Merry Christmas crypto virus that first appeared in December last year. The threat is also known by the name Merry X-Mas and belongs to the ransomware category. Thus .merry virus file extension is part of advanced malicious software that aims to compromise computers and encrypt particular data stored on all disks and drives. The .merry virus demands all victims to pay a ransom in order to restore their compromised data.
In case that your system is infected with the .merry file virus extension there is no doubt that you should not finance the crooks by paying the ransom and better try to remove the ransomware’s strains from your system in order to use the computer in a safe manner again. This article will be of a help with the removal process of all malicious files and objects created by the .merry ransomware. Once your system is completely clean, safe and protected you could attempt to restore .merry encrypted files.
| Name |
Merry Christmas Ransomware |
| File Extensions |
.merry |
Previous variants |
.MRCR1 malicious extension; .RMCM1 malicious extension |
| Ransom |
Varies |
| Solution #1 |
Use the help of an anti-malware tool to remove .merry virus and any additional cyber-security threats. |
|
Solution #2 |
Remove Merry Christmas ransomware manually by following the guidelines of our step-by-step guide below. |
| Distribution |
Spam emails, malicious URLs, malicious attacments, exploit kits, freeware. |
Infection Techniques Used by .Merry Virus File
The crooks may implement several infection techniques in order to be sure that their malicious software will reach and infect as many users as possible. The ways that you may get infected with Merry Christmas ransomware include:
- Phishing e-mail – the sender of such e-mail usually poses as a legitimate source. The message of the e-mail is most likely to attempt to convince you that the case is urgent and you should interact with a file that is attached to the letter. The attachment may contain .zip archive that once extracted can lead to infection with Merry X-Mas ransomware. The malicious payloads of the threat may be imported in the code of a malicious web page and another way of distribution may be a link presented in the message that once clicked lands on the malicious page and activates the infection process of .merry virus file.
- Malicious advertisements – they may come in the form of a banner, pop up, pop up window or link in a message. Again they contain a malicious link to a web page that one entered may automatically start a drive-by download attack and the infection may start even without noticing that something wrong is happening before you see the ransom notification and your data locked by .merry file extension.
- Freeware installation – the malicious files that cause infection with Merry Christmas ransomware may come bundled with the installation package of free software.
These techniques are among the most commonly used for ransomware infection campaigns. However, as users get more security aware, thus, able to recognize the situations that hide the potential risk of malware infection, crooks are constantly searching for new ways to mislead their victims and enforce various infection techniques.
Detailed Information of .Merry Ransomware
The .merry virus file extension is a trait of the so-called Merry Christmas ransomware. This crypto virus is written in Delphi and uses custom encryption algorithm. Once the threat is running on the computer it will scan all disks and drives for particular data that is set as a target in its code. The target data list may include the following types of files:
- Documents.- .docx, .doc , .dox , .pdf, .pptx, .txt, etc.
- Music and other audio – .mp3, .wma, .amr, etc.
- Photos – .jpg, .png, .jpeg, .svg and other
- Videos – .mp4, .avi, .flv, etc.
- Files associated with games
- Files linked to other commonly used Software
All encrypted data gets the file extension .merry appended after the file name. The files can’t be open by any program and remain unusable until the specific decryption key is applied. The decryptor and the decryption key are held by the malicious intenders and they demand a ransom in order to deliver them to the victims.
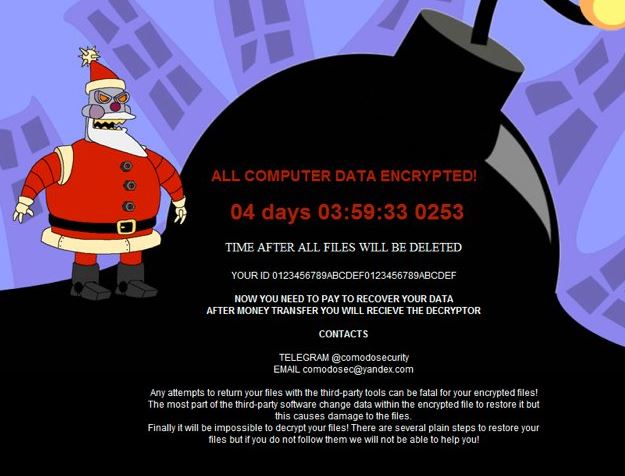
A ransom note is yet another Merry Christmas ransomware feature. The threat is programmed to drop a file named MERRY_I_LOVE_YOU_BRUCE.HTA that serves as a message from the ransomware creators. The source code of the threat is programmed to open automatically the file and display it as dynamic desktop wallpaper. It is dynamic as there is a timer that is counting down the remaining time before all encrypted files will be deleted. Тhe wallpaper depicts thematically an evil Santa robot and huge bomb that is going to explode. The whole ransom text reads:
“ALL COMPUTER DATA ENCRYPTED
TIME AFTER ALL FILES WILL BE DELETED
YOUR ID
NOW YOU NEED TO PAY TO RECOVER YOUR DATA
AFTER MONEY TRANSFER YOU WILL RECIEVE THE DECRYPTOR
CONTACTS
TELEGRAM @comodosecunty
EMAIL [email protected]
Any attempts to return your files with the third-party tools can be fatal for your encrypted files! The most part of the third-party software change data within the encrypted file to restore it but this causes damage to the files.
Finally, it will be impossible to decrypt your files! There are several plain steps to restore your files but if you do not follow them we will not be able to help you!”
There is no information about the exact ransom amount but it is probably required to be in BTC. However, we advise all victims to avoid contact the crooks using the stated addresses.
How to Remove .Merry Virus File and Restore Data
The removal instructions below will guide you through the removal process of .merry virus file and Merry Christmas ransomware. You could choose whether to take manual or automatic removal approach.
And once your computer is malware free it’s time to focus on the recovery process. Before making any attempts ensure to have copies of all encrypted files with the .merry file extension. This step will avoid the loss of the data in case that something goes wrong during the recovery. The good news is that the previous versions of Merry Christmas ransomware are successfully decrypted. So, it is highly possible to restore your .merry files with the help of the free decrypter for Marry Christmas ransomware versions released by Emsisoft.
Merry Christmas Ransomware Removal
For a faster solution, you can run a scan with an advanced malware removal tool and delete Merry Christmas completely with a few mouse clicks.
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Merry Christmas Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
-
1) Use present backups
2) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
Don’t hesitate to contact us for further help! , BSS Team



