Viki virus is ransomware that encrypts sensitive data found on the affected machines. The .viki file type extensions is used to mark all processed data. It is also known under the alias of CryptoViki. The computer users are extorted to pay a ransomware fee to restore access to their data. Victims can remove the Viki ransomware virus by using our in-depth removal guide. There are two ways of restoring your computer:
Manual Removal Guide
Recover .viki Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Viki Virus – All Before and After This Event
The Viki virus is a computer ransomware that has recently been discovered by malware researchers. At the moment the identity behind the Viki virus is not known. It may be a single person or a hacker collective. The collected malware samples do not indicate any similarity between the malware engine and any of the known malware families.
Upon infection the Viki ransomware virus performs several steps before starting its internal encryption engine. It sets up a persistent state of execution which effectively prevents manual removal. The virus is able to make Windows registry modifications and monitor it for any changes. This can also disable any running security software and operating system capabilities. One of the main goals of this is to run the Viki virus every time the computer boots.
Based on the predefined configuration the ransomware may also perform other dangerous modifications to the infected computers. Example modules may include the institution of surveillance functions and remote control by the criminal operators.
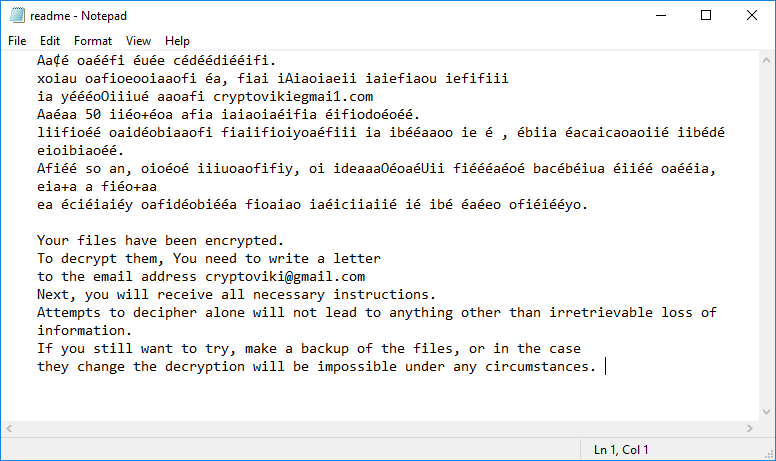
When all preparatory stages are complete the Viki ransomware virus continues with its built-in encryption module. It starts to process system and user data using a predefined fil type list that can be configured accroding to the targets. Potential files include music, photos, videos, documents archives, configuration files, databases and etc. The note displays the following content:
Aa¢é oaééfi éuée cédéédiééifi.
xoiau oafioeooiaaofi éa, fiai iAiaoiaeii iaiefiaou iefifiii
ia yéééoOiiiué aaoafi cryptovikiegmai1.com
Aaéaa 50 iiéo+éoa afia iaiaoiaéifia éifiodoéoéé.
liifioéé oaidéobiaaofi fiaiifioiyoaéfiii ia ibééaaoo ie é , ébiia éacaicaoaoiié iibédé
eioibiaoéé.
Afiéé so an, oioéoé iiiuoaofifiy, oi ideaaaOéoaéUii fiéééaéoé bacébéiua éiiéé oaééia,
eia+a a fiéo+aa
ea éciéiaiéy oafidéobiééa fioaiao iaéiciiaiié ié ibé éaéeo ofiéiééyo.Your files have been encrypted.
To decrypt them, You need to write a letter
to the email address [email protected]
Next, you will receive all necessary instructions.
Attempts to decipher alone will not lead to anything other than irretrievable loss of
information.
If you still want to try, make a backup of the files, or in the case
they change the decryption will be impossible under any circumstances.
As usual the hackers behind the Viki virus make the victims pay a ransomware fee. Unlike some other popular malware of this type they do not specify a fixed sum. Instead the criminal operators have supplied a contact e-mail address hosted on freely hosted Gmail service. It is very likely that this is used as a relay and decoy for another email inbox.
Computer hackers use the popular tactic of evaluating the needed sum to restore the files based on their contents. If it contains private and sensitive information then a high fee may be quoted. Ransomware viruses like Viki almost exclusively request the money to be paid in the Bitcoin digital currency. The transactions are made anonymous and cannot be traced to a specific individual.
In addition the Viki ransomware virus deletes all found Shadow volume copies. This means that data recovery is impossible without the use of a quality solution.
Viki Virus Distribution Tactics
The collected Viki ransomware virus samples have been found to infect computer users via different strategies. One of the main ones is the use of phishing emails. They use social engineering tricks that make the targets infect themselves with the binary. Depending on the used template the Viki virus may be directly attached to the messages or linked in the body contents.
Hackers may also opt to use infected software installers or office documents. They contain the Viki ransomware in a covert way and resemble legitimate content. Such files can be found on hacked or hacker-controlled download sites and P2P networks like BitTorrent.
Advanced ransomware strains and payload droppers, as well as web redirect scripts can also lead to a Viki virus infection.
Related: OnyonLock Ransomware Virus
Remove Viki Virus and Restore Encrypted Files
WARNING! Manual removal of the Viki ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Viki Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover .viki Files
WARNING! All files and objects associated with Viki ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



