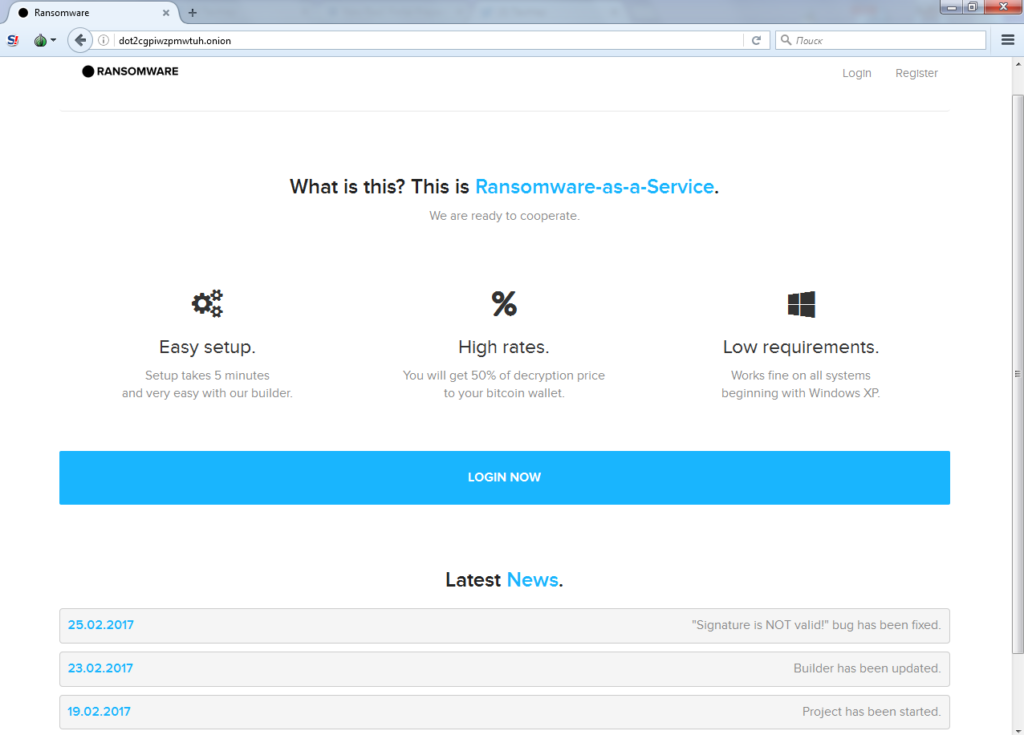
DotRansomware is RaaS (ransomware as a service) that is being spread to malicious intenders via dark web markets. Some security researchers claim it to be a sample of another threat that we reported last week – Unlock26 ransomware.
More About DotRansomware and Its Features
If you get infected your files will become encrypted afterward get a malicious extension. Being a RaaS, the DotRansomware kit allows extortionists to build custom versions of the threat. So the threat can be detected using various malicious extensions, ransom amounts, and bitcoin addresses.
It is well known that DotRansomware utilizes the AES encryption algorithm in order transform the files making them unusable before the decryption price in BitCoins is paid. The following list of file extensions presents all file types that DotRansomware can encrypt upon infection:
.001, .1dc, .3ds, .3fr, .7z, .a3s, .acb, .acbl, .accdb, .act, .ai, .ai3, .ai4, .ai5, .ai6, .ai7, .ai8, .aia, .aif, .aiff, .aip, .ait, .anim, .apk, .arch00, .ari, .art, .arw, .asc, .ase, .asef, .asp, .aspx, .asset, .avi, .bak, .bar, .bay, .bc6, .bc7, .bgeo, .big, .bik, .bkf, .bkp, .blob, .bmp, .bsa, .c, .c4d, .cap, .cas, .catpart, .catproduct, .cdr, .cef, .cer, .cfr, .cgm, .cha, .chr, .cld, .clx, .cpp, .cr2, .crt, .crw, .cs, .css, .csv, .cxx, .d3dbsp, .das, .dat, .dayzprofile, .dazip, .db, .db0, .dbf, .dbfv, .dcr, .dcs, .der, .desc, .dib, .dlc, .dle, .dlv, .dlv3, .dlv4, .dmp, .dng, .doc, .docm, .docx, .drf, .dvi, .dvr, .dwf, .dwg, .dxf, .dxg, .eip, .emf, .emz, .epf, .epk, .eps, .eps2, .eps3, .epsf, .epsp, .erf, .esm, .fbx, .ff, .fff, .fh10, .fh11, .fh7, .fh8, .fh9, .fig, .flt, .flv, .fmod, .forge, .fos, .fpk, .fsh, .ft8, .fxg, .gdb, .ge2, .geo, .gho, .gz, .h, .hip, .hipnc, .hkdb, .hkx, .hplg, .hpp, .hvpl, .hxx, .iam, .ibank, .icb, .icxs, .idea, .iff, .iiq, .indd, .ipt, .iros, .irs, .itdb, .itl, .itm, .iwd, .iwi, .j2k, .java, .jp2, .jpe, .jpeg, .jpf, .jpg, .jpx, .js, .k25, .kdb, .kdc, .kf, .kys, .layout, .lbf, .lex, .litemod, .lrf, .ltx, .lvl, .m, .m2, .m2t, .m2ts, .m3u, .m4a, .m4v, .ma, .map, .mat, .max, .mb, .mcfi, .mcfp, .mcgame, .mcmeta, .mdb, .mdbackup, .mdc, .mddata, .mdf, .mdl, .mdlp, .mef, .mel, .menu, .mkv, .mll, .mlx, .mn, .model, .mos, .mp, .mp4, .mpqge, .mrw, .mrwref, .mts, .mu, .mxf, .nb, .ncf, .nef, .nrw, .ntl, .obm, .ocdc, .odb, .odc, .odm, .odp, .ods, .odt, .omeg, .orf, .ott, .p12, .p7b, .p7c, .pak, .pct, .pcx, .pdd, .pdf, .pef, .pem, .pfx, .php, .php4, .php5, .pic, .picnc, .pkpass, .png, .ppd, .ppt, .pptm, .pptx, .prj, .prt, .prtl, .ps, .psb, .psd, .psf, .psid, .psk, .psq, .pst, .ptl, .ptx, .pwl, .pxn, .pxr, .py, .py, .qdf, .qic, .r3d, .raa, .raf, .rar, .raw, .rb, .rb, .re4, .rgss3a, .rim, .rofl, .rtf, .rtg, .rvt, .rw2, .rwl, .rwz, .sav, .sb, .sbx, .sc2save, .sdf, .shp, .sid, .sidd, .sidn, .sie, .sis, .skl, .skp, .sldasm, .sldprt, .slm, .slx, .slxp, .snx, .soft, .sqlite, .sqlite3, .sr2, .srf, .srw, .step, .stl, .stp, .sum, .svg, .svgz, .swatch, .syncdb, .t12, .t13, .tar, .tax, .tex, .tga, .tif, .tiff, .tor, .txt, .unity3d, .uof, .uos, .upk, .vda, .vdf, .vfl, .vfs0, .vpk, .vpp_pc, .vst, .vtf, .w3x, .wallet, .wav, .wb2, .wdx, .wma, .wmo, .wmv, .wotreplay, .wpd, .wps, .x3f, .xf, .xl, .xlk, .xls, .xlsb, .xlsm, .xlsx, .xvc, .xvz, .xxx, .ycbcra, .yuv, .zdct, .zip, .ztmp
The list is pretty long consisting of 380 file types that may get the malicious extension .locked for example. Thus you may found all your MS Office and PDF files, text files, images, music, videos, archives, etc. encrypted once hit by DotRansomware.
Another trait of DotRansomware infection is an HTML file that may be dropped on your desktop as well as other computer folders. The record serves as a message from the crooks to the victims and may automatically change your default desktop screen. Having the function of a ransom note, it is most likely to inform you about the main impact of the ransomware and urge you to act further to restore your encrypted data. No matter of the provided instructions and the demanded ransom amount we advise you to avoid any contact with the crooks and restrict any payment actions. Better stay on the state of security and try using secure recovery methods once you remove all malicious files and objects associated with DotRansomware (you could find help at the end of the article).
Furthermore, the DotRansomware crypto virus may disable Windows Startup Repair and Windows Error Recovery Screen on Startup using the bcdedit command. Windows Startup Repair tool could repair the Windows by replacing essential operating system files that might be damaged or missing and Windows Error Recovery offers Safe Mode options, Last Known Good Configuration (advanced), or Start Windows Normally when the system didn’t shut down properly the last time it was used. However, in the removal instructions below you can find an efficient way to boot the PC in safe mode in order to eliminate the DotRansomware infection.
DotRansomware may disable volume shadow copy backup using vssadmin application with the following command:
vssadmin delete shadows /all /quiet
So it may be impossible to restore some files using the Shadow Explorer software. Anyway, you could find some alternative methods to get your encrypted files back to normal.
How Could DotRansomware Infect Your System?
Having the RaaS kit for DotRansomware cyber criminals can either keep the original settings or implement their custom settings. Afterward, they should carry out malicious campaign against target users.
Commonly crooks distribute the threat via spam email that either contains malicious code in the message being a suspicious link, button, image or malicious attachment – document, zip archive file that contains the malicious payload of DotRansomware.
DotRansomware may infect your system by being bundled with any freeware that you have recently downloaded. A click on aggressive ads, banners, pop-ups that are injected with malicious payloads of the ransomware could also result in a crypto virus infection of your data and computer.
DotRansomware – Remove the Threat Completely from the Computer
In case you are a victim of this vicious threat, there is no doubt that you should remove all traits and proceed using your computer in a secure manner. By following the detailed removal guide below, you could do it by yourself.
Following the removal process make backup copies of all encrypted files before making any recovery approaches.
Summary of the DotRansomware
| Name |
DotRansomware |
| File Extensions |
Unknown |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove DotRansomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
DotRansomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam email campaigns, malicious ads & etc. |
DotRansomware Removal Guide
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely DotRansomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
-
1) Use present backups
2) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.



