An infection with the dangerous Payment virus leads to serious security issues. Victims can restore and protect their computers by following our complete removal guide.
Remove Payment virus and Restore PC
Manual Removal Guide
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Distribution of Payment virus
The Payment virus is a new virus which has been sighted in a limited attack campaign. At the moment the security researchers cannot determine the primary infection strategy. We presume that the most widely used tactics are going to be employed.
Among them are the email messages created in an automated way and sent to large lists of potential victims. The Payment virus can be directly attached to the messages. This is one of the easiest way for the criminals to attempt the infection. However a lot of email hosting providers usually capture the signatures of the virus and as such discard such messages or label them as dangerous or spam. Other infection methods related to this one is the option of inserting hyperlinks in the body content of the messages. The links are usually labeled as leading to a familiar website or a file of user interest. Redirects can redirect to hacker-controlled sites, infected payloads or other instances that can lead to an Payment virus infection.
The computer criminals behind the malware can create malicious sites or download portals which distribute malware of different kinds, including the Payment virus. A popular option is the use of infected documents which may be of different types ‒ spreadsheets, rich text documents, presentations and databases. They are modified to initiate the virus once the built-in scripts are run. Usually when the files are opened a notification will ask the users to run the macros (scripts). If this is done the infection follows.
The hacker-controlled sites are specialist portals that have been created either manually or automatically by the criminals behind the Payment virus. They can either directly distribute the threat by initiating various scripts or automated operations or link to such instances. Redirects are usually caused by email interaction, ad networks or other browsing activity. However one of the main sources is the availability of browser hijackers. They are malicious addons made for the most popular web browsers ‒ Mozilla Firefox, Google Chrome, Internet Explorer, Opera, Microsoft Edge and Safari. Once installed they not only infect the users with the malware, but also redirect the victims to a hacker-controlled site. Depending on the configuration the browser hijackers can also steal sensitive information such as any stored passwords, account credentials, history, bookmarks, form data and settings.
Impact of Payment virus
The Payment virus is a recently discovered malware threat of unknown origin. The security experts that reported the infections signal that the initial code analysis did not find any correlation with any of the famous virus families. The most likely scenario is that the hacker or criminal collective behind it are the ones that have made it. The captured samples and the current attack wave seem to target Spanish-speaking users at the moment.
The identified behavior of the Payment virus shows some signs of advanced malware operations. After the infection has been instituted on the victim computer through any one of the distribution strategies. The Payment virus has been identified to open and manipulate system-specific files and settings in order to facilitate its installation deep into the host. This allows the hacker operators to conduct a persistent installation as any critical changes to the system with the combination of a capable infection engine can actively prevent the users from using manual removal methods. In addition if properly configured it can also protect itself from certain security software including basic anti-virus tools, firewalls and IDS systems. The Payment virus can either disable them or delete itself to avoid detection.
The Windows registry is also affected by the Payment virus — entries are modified, others are added containing values related to the operations of the malware. At the same time several processes are created and terminated when complete. The security experts have also observed that the main Payment virus engine is modular as it is able to load and execute additioanl modules both carried together with the virus payload itself or loaded externally.
Future versions might integrated in themselves a Trojan component which gives the operators the ability to spy on the victims, as well as record their mouse movement and keystrokes. Some versions can even allow the execution of arbitrary commands at all times. The Payment virus is an useful tool to deploy additional threats to the victim computers.
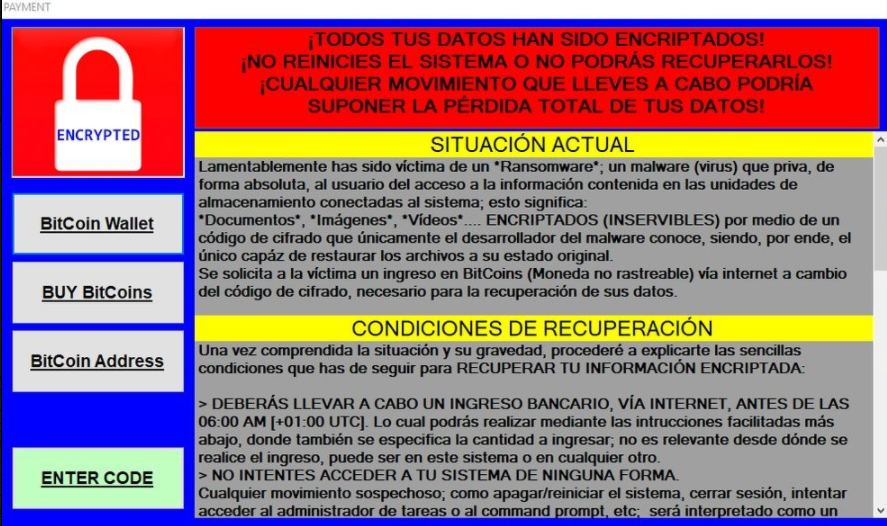
Once all prerequisite steps have been taken the Payment virus launches its ransomware process by processing target file type extensions based on a built-in list. Examples include the following; archives, documents, backups, images, videos, music, configuration files and etc. Once this is done a locksreen is instituted which is superimposed on top of all other applications and prevents ordinary computer interaction until the threat has been completely removed. It shows the following message to the victims:
¡TODOS TUS DATOS HAN SIDO ENCRIPTADOS!
¡NO REINICIES EL SISTEMA O NO PODRÁS RECUPERARLOS!
¡CUALQUIER MOVIMIENTO QUE LLEVES A CABO PODRÍA
SUPONER LA PÉRDIDA TOTAL DE TUS DATOS!
—————————————-
SITUACIÓN ACTUAL
—————————————-
Lamentablemente has sido víctima de un *Ransomware*; un malware (virus) que priva, de forma absoluta, al usuario del acceso a la información contenida en las unidades de almacenamiento conectadas al sistema; esto significa:
*Documentos*, *Imágenes*, *Vídeos*…. ENCRIPTADOS (INSERVIBLES) por medio de un código de cifrado que únicamente el desarrollador del malware conoce, siendo, por ende, el único capáz de restaurar los archivos a su estado original.
Se solicita a la víctima un ingreso en BitCoins (Moneda no rastreable) vía internet a cambio del código de cifrado, necesario para la recuperación de sus datos.
—————————————-
CONDICIONES DE RECUPERACIÓN
—————————————-
Una vez comprendida la situación y su gravedad, procederé a explicarte las sencillas condiciones que has de seguir para RECUPERAR TU INFORMACIÓN ENCRIPTADA:
> DEBERÁS LLEVAR A CABO UN INGRESO BANCARIO, VÍA INTERNET, ANTES DE LAS 06:00 AM [+01:00 UTC]. Lo cual podrás realizar mediante las intrucciones facilitadas más abajo, donde también se especifica la cantidad a ingresar; no es relevante desde dónde se realice el ingreso, puede ser en este sistema o en cualquier otro.
> NO INTENTES ACCEDER A TU SISTEMA DE NINGUNA FORMA
Cualquier movimiento sospechoso; como apagar/reiniciar el sistema, cerrar sesión, intentar acceder al administrador de tareas o al command prompt. etc; será interpretado como un …
—
A machine-translated version of it reads the following:
ALL YOUR DATA HAVE BEEN ENCRYPTED!
DO NOT RESET THE SYSTEM OR YOU WILL NOT BE ABLE TO RECOVER THEM!
ANY MOVEMENT YOU CARRY OUT COULD
SUPPORT THE TOTAL LOSS OF YOUR DATA!
—————————————-
CURRENT SITUATION
—————————————-
Unfortunately you have been a victim of a * Ransomware *; a malware (virus) that absolutely deprives the user of access to the information contained in the storage units connected to the system; this means:
* Documents *, * Images *, * Videos * …. ENCRYPTED (INSERVIBLE) by means of an encryption code that only the malware developer knows, being, therefore, the only ability to restore the files to their original state .
The victim is requested to enter BitCoins (non-traceable currency) via internet in exchange for the encryption code, necessary for the recovery of their data.
—————————————-
CONDITIONS OF RECOVERY
—————————————-
Once the situation and its seriousness are understood, I will proceed to explain the simple conditions that you have to follow to RECOVER YOUR ENCRYPTIONED INFORMATION:
> YOU WILL HAVE TO CARRY OUT A BANK INCOME, VIA THE INTERNET, BEFORE 06:00 AM [+01: 00 UTC]. Which you can do through the instructions provided below, where you also specify the amount to enter; It is not relevant from where the income is made, it can be in this system or in any other.
> DO NOT ATTEMPT TO ACCESS YOUR SYSTEM IN ANY WAY
Any suspicious movement; how to turn off / restart the system, log out, try to access the task manager or the command prompt. etc; will be interpreted as a …
—
We recommend that all users abstain from communicating with the hackers and use our full Payment virus removal guide below to recover their data and delete the active infections.
Remove Payment virus and Restore PC
WARNING! Manual removal of the Payment virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Payment virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Remove Payment from Windows
Here’s a way to remove the program. This method will work regardless if you’re on Windows 10, 8, 7, Vista or XP. Simply selecting the program and pressing delete won’t work, as it’ll leave a lot of small files. That’s bad because these leftovers can linger on and cause all sorts of problems. The best way to delete a program is to uninstall it. Here’s how you can do that:
1. Hold the “Windows” button (It’s between CTRL and Alt on most keyboards) and press “R”. You’ll see a pop-up window.

2. In the textbox, type “appwiz.cpl”, then press“ Enter ”.

3. The “Programs and features” menu should now appear. It’s a list of all the programs installed on the PC. Here you can find the program, select it, and press “Uninstall“.

Remove Payment Virus From Your Browser
Before resetting your browser’s settings, you should know that this action will wipe out all your recorded usernames, passwords, and other types of data. Make sure to save them in some way.
-
1. Start Mozilla Firefox. In the upper right corner, click on the Open menu icon and select “Add-ons“.

2. Inside the Add-ons Manager select “Extensions“. Search the list of extensions for suspicious entries. If you find any, select them and click “Remove“.

3. Click again on the Open menu icon, then click “Options“.

4. In the Options window, under “General” tab, click “Restore to Default“.

5. Select “Search” in the left menu, mark the unknown search engine and press “Remove”.

-
1. Start Google Chrome. On the upper-right corner, there a “Customize and Control” menu icon. Click on it, then click on “Settings“.

2. Click “Extensions” in the left menu. Then click on the trash bin icon to remove the suspicious extension.

3. Again in the left menu, under Chrome, Click on “Settings“. Go under “On Startup” and set a new page.

4. Afterward, scroll down to “Search“, click on “Manage search engines“.

5. In the default search settings list, find the unknown search engine and click on “X“. Then select your search engine of choice and click “Make default“. When you are ready click “Done” button in the right bottom corner.

2. In the “Manage add-ons” window, bellow “Add-on Types“, select “Toolbars and Extensions“. If you see a suspicious toolbar, select it and click “Remove“.

3. Then again in the “Manage Add-ons” window, in “Add-on Types“, Select “Search Providers“. Chose a search engine and click “Set as default“. Select the unknown search engine and click “Remove and Close”.

4. Open the Tools menu, select “Internet Options”.

5. In the “General” tab, in “Home page”, enter your preferred page. Click “Apply” and “OK”.

Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help



