The Clouded ransomware virus aims to encrypt sensitive user data in order to demand a ransom from the victims. The virus is designed to add the malicious extension .cloud to each corrupted file. Upon encryption, all target files are inaccessible until a ransom sum of at least 0.1 BTC (currently $157.95) is transferred to crooks’ Bitcoin address.You can remove Clouded virus by:
- Following our manual removal guide at bottom of the article, or
- Using a quality virus removal tool.
DOWNLOAD CLOUDED RANSOMWARE VIRUS REMOVAL TOOL.
You can then follow the steps below to restore your files.
How Can Clouded Virus Infiltrate the PC?
Crooks who disseminate Clouded virus are likely to use spam emails with attached files, compromised links in the text or combination of both. Beware that even if the sender seems to be a legit one such as your friend, we advise you to be alert before initiating further actions. One way to do this is via online malware scanning services (VirusTotal, ZipeZip). Moreover, always think twice before clicking on links on social media networks and advertisements (pop-ups, banners, links, thumbnails,etc.) as Clouded virus as well as many other malware threats like Cerber ransomware and Zeus Trojan virus are stalking to infect your PC.
Another way to stay protected from Clouded virus is having an installed and up-to-date anti-malware tool.
Clouded Virus – Ransomware Features
Clouded virus is a data locker ransomware, and as such it enforces a built-in encryption module to modify sensitive data and restrict any access to it. The infection process starts the moment clouded.exe is executed in the system. The clouded.exe file is likely to create new files and access some Windows system libraries intending to utilize functions and processes that will ensure its permanent existence on the infected PC. Significant Windows folders may be set as destinations of the malicious files:
- %USERPROFILE%
- %TEMP%
- %APPDATA%
- %LOCALAPPDATA%
Once established, Clouded ransomware virus enforces a scanning process of searching for all files that match the predefined types set by its creators. All target files get encrypted via cipher algorithm so that victims are no longer able to use them. A notable trait of the Clouded virus is the malicious extension .cloud it appends to all encrypted files. The files that Clouded ransomware virus may encrypt are photos, images, documents, text files, videos, MS Office files, databases, backups, archives, etc.
Also, Clouded ransomware may modify some Windows registry keys like RUN and RUNONCE. These keys control all processes that should start on each Windows boot up and also allow Clouded virus to display its ransom note upon the encryption process.
The ransom note is written in a way to urge victims to pay the demanded amount if they want to restore .cloud files. Actually, hackers request to transfer the ransom to them in exchange for unique decryption keys which are generated during the encryption stage of Clouded infection. It is notable that the Clouded ransomware is designed to produce a separate one-of-a-kind key for each encrypted file. These keys are believable to decrypt all .cloud files. However, we remind all victims that the attack is triggered by cyber criminals so for the sake of your security it is better to avoid any negotiations with them and choose not to rely on what they promise.
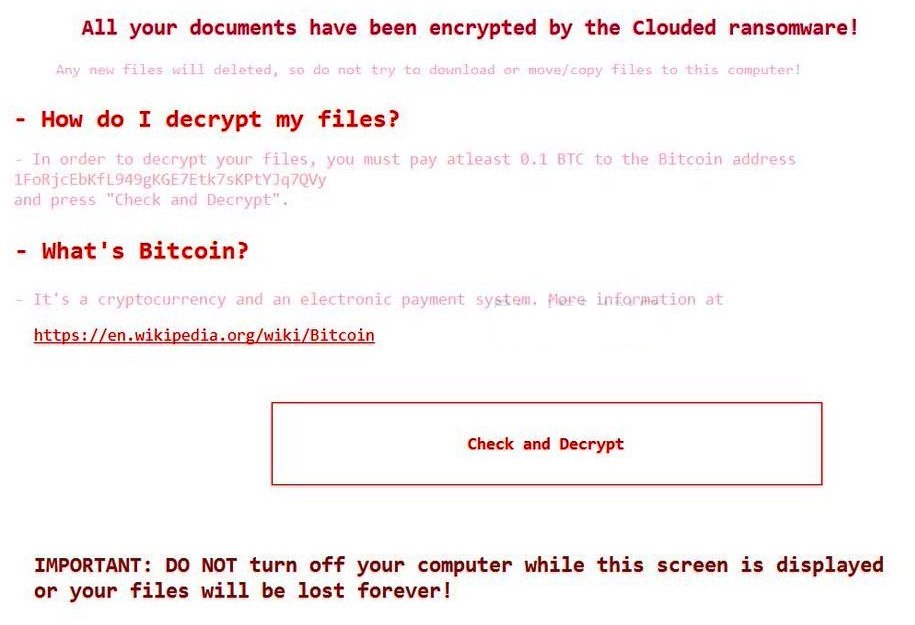
Here is the entire message that Clouded virus ransom note states to the infected users:
All your documents have been encrypted by the Clouded ransomware!
Any new files will deleted, so do not try to download or move/copy files to this computer!
– How do I decrypt my files?
– In order to decrypt your files, you must pay atleast 0.1 BTC to the Bitcoin address
1FoRjcEbKfL949gKGE7Etk7sKPtYJq7QVy and press “Check and Decrypt”.
– What’s Bitcoin?
– It’s a cryptocurrency and an electronic payment system. More information at
https://en.wikipedia.org/wiki/Bitcoinbutton [Check and Decrypt]
IMPORTANT: DO NOT turn off your computer while this screen is displayed or your files will be lost forever!
Clouded Ransomware Virus Removal
Clouded virus pretends that it will delete all files from the infected PC once it is turned off which makes the removal process of the threat rather a delicate task. In the removal guide below, we will reveal how to remove Clouded ransomware virus step-by-step in a way to save your data.
Once you’re done with the removal process, some alternative data recovery solutions may help to restore sensitive .cloud files. OK, let’s begin..
Ransomware Removal Steps
STEP I:
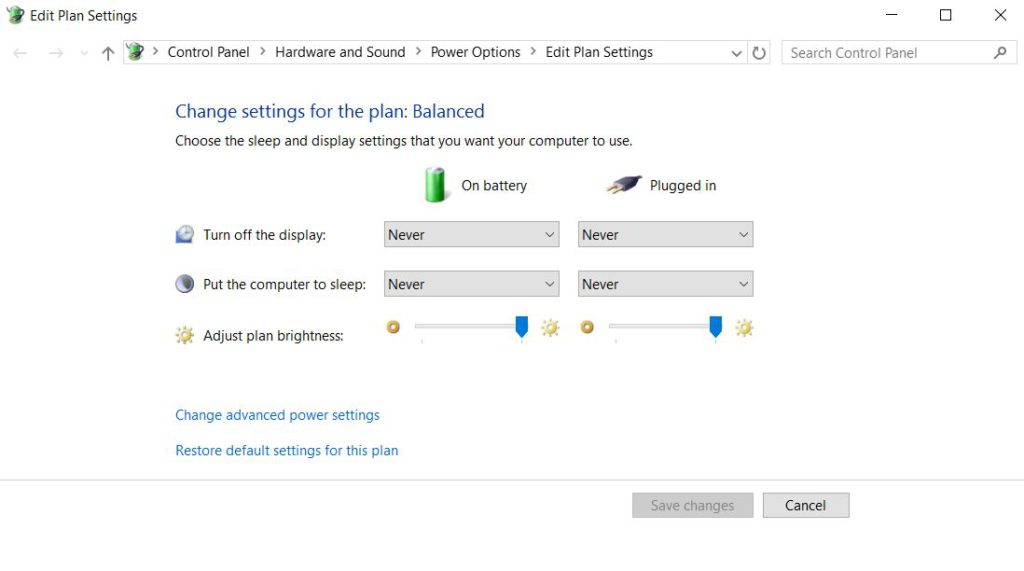
STEP I: Prevent System Power Off
- 1) Click the Windows button and start typing Power and Sleep settings.
2) When the result appears, click on it. Set everything to Never and assure that your battery is fully charged.
- 3) Then find all encrypted .cloud files and backup them on an external drive.
4) Switch the drive from another device and check if all corrupted are saved.
Once you are sure that all files are correctly saved on the external drive, you need to remove all malicious files and objects created on the system by the Clouded virus.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP II: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP III: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP VI: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP V: Remove Completely Clouded Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP VI: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VII: Recover Encrypted Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
STEP VIII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



