Right now, the biggest fish in the virus ocean is the Cerber ransomware. Cerber is a ransomware service, meaning that cyber-criminals rent the virus and then distribute it by themselves. The ransomware was massively successful, bringing almost a million dollars for the scammers.
Why Is the Cerber Ransomware So Successful?
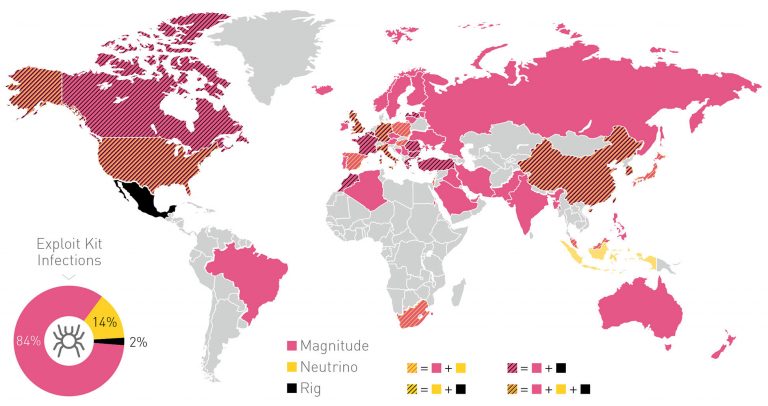
A joint study by the Israeli cyber-security firms CheckPoint and Intsights reveals the proportions of the Cerber ransomware operation. The report states that the deciding factor in Cerber’s success is the effective use of exploit kits by the criminals. The ransomware is also reported to run around 160 active campaigns, infecting 150 thousand users in 201 countries worldwide. These estimates are recent, and the overall number of infected users is much higher.
A map of the spread of the Cerber operation:
The developers of Cerber and the cyber-criminals who rent the virus split the profits. The developers get 40% while the affiliates keep the rest. That’s a huge sum of money, considering the service made $195,000 last month. Cerber’s usual ransom fee is 1 BTC which is slightly under $600 as of now.
How are the crooks getting away with it? By using a complex Bitcoin laundering scheme involving thousands of wallets. The mysterious Bitcoin currency is very popular among criminals because of its hard-to-trace nature (it’s still unknown who’s even responsible for its invention.) Cyber-criminals and scammers aren’t the only ones who use it, as there are rumors of ISIS utilizing the currency. The wallet scheme scrambles the payments to make them untraceable.
Ransomware Services Like Cerber Are Only Going to Get Worse
Ransomware services are becoming more popular in the cyber-underworld. Virus authors make the ransomware, and then scammers spread it. It’s a dangerous trend, as spreading a ready-made ransomware is much easier than making one from scratch. The massive amount of financial reward and the low risk of getting caught make internet scamming a very popular trend in the criminal world. Services like Cerber also have a low-requirements in terms of tech skills, which makes it even more accessible to crooks. Yesterday, we reported another ransomware service, the Shark ransomware project which promises affiliates who spread the virus an even bigger share of the profit, 80%. In addition to that, Shark is free-to-download. That’s bound to attract more cyber-criminals, though Shark could also be disingenuous, and not actually pay its affiliates. It’s a scam in more ways than one.
Businesses, hospitals, and other establishments are more vulnerable to ransomware campaigns, though it’s still possible for individual users to get infected. Sadly, some people prefer to pay the criminals as quickly as possible and get back to work instead of clearing their systems in a more efficient way. Users often panic and don’t want to risk losing their files, especially if they’re related to work. Paying, however, can be riskier than waiting for a decrypter or removing the ransomware by other means, as scammers aren’t obligated to keep their word and decrypt the locked files.
Protection Against Cerber and Other Ransomware Viruses
You can find guides of how to remove Cerber and Cerber2. As big as Cerber is right now, it’s only a drop in the ransomware bucket. The market is worth millions and chances are only going to get worse as time goes on. The usual point from virus protection applies: get an anti-virus or anti-malware tool, avoid email spam and shady advertisings, and try to get the virus removed before paying the ransom. Always check for a decrypter or other software than can help you in the fight against ransomware viruses. Don’t just give money to cyber criminals. As this article proves, they’re already making too much undeserved money as it is.



