The Amnesia2 virus is a new iteration of the Amnesia malware family. The ransomware engine encrypts a wide range of victim files and renames them following a built-in pattern ending with the .TRMT extension. The affected computer users can restore their computers and files by following our complete removal guide.
Manual Removal Guide
Recover Encrypted Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How Does Amnesia2 Virus Infiltrate the System?
The researchers have not confirmed that the new Amnesia2 virus is made by the same hackers behind the original core threat. This means that the malware samples can be spread using different strategies.
A primary tactic is the use of email spam messages. They are made to appear as being sent by legitimate government agencies or famous companies. The users can get infected with the Amnesia2 virus by downloading file attachment containing the malicious payload or visiting links placed in the body contents. Such messages can also link or attach infected software installers or office documents. They are masked as legitimate copies of the original source content and contain built-in scripts that lead to an Amnesia2 virus infection.
The original Amnesia malware was spread using a large-scale botnet attack, it is possible that criminals can use related methods to infect victims with the new version.
Malicious web browser addons can also be used to deliver the Amnesia2 virus. They are known as browser hijackers and are usually made for the most popular ones: Mozilla Firefox, Google Chrome, Safari, Internet Explorer and Microsoft Edge. The addons are advertised on the relevant app stores or third-party sites as providing additional functionality. Upon installation they modify essential settings: the default home page, search engine and new tabs page. They point to a hacker-controlled site that leads to the infection. In addition the criminals are able to harvest sensitive information such as: stored cookies, passwords, form data, history and bookmarks.
The hackers can hack or create download sites and portals that resemble official sources of famous software or companies. In a similar manner we have detected numerous malicious and hacker-controlled ad networks and redirect scripts that are found on legitimate sites as well.
Related: .Wallet File Virus (Dharma Ransomware), Sage 2.0 Ransomware Virus
Infection Flow of Amnesia2 Virus
The Amnesia2 virus is the latest iteration of the Amnesia malware family. Previous versions of the threat have been used in a large-scale worldwide attack against IoT devices two months ago.
Like other samples that are derived from the core family it includes a sophisticated encryption engine that seeks to encrypt a lot of file type extensions. Depending on the configuration the built-in file list may be changed. In the majority of cases the people behind the Amnesia2 virus seek to process the most popular file type extensions: documents, music, videos, photos, archives, backups, databases and etc.
All affected data is renamed based on a template: [3g000000000random_name].[[email protected]].TRMT
. This is compromised of 3 elements:
- A randomly-generated string – Calculated based on harvested system data. This part of the ransomware extension is individual for each machine
- [email protected] – Contains the criminals email address used for contacting them.
- TRMT – New extension string added in the latest version of the Amnesia2 virus.
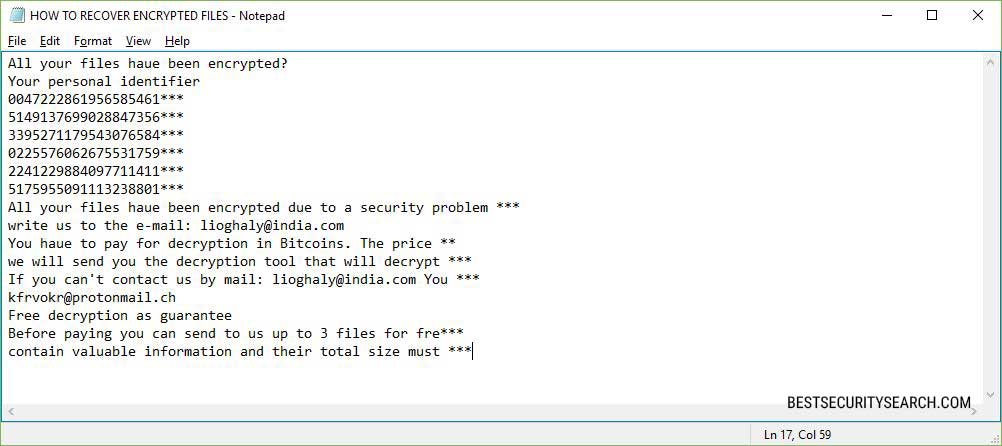
The ransomware note itself is crafted once the encryption process is complete. The file is named HOW TO RECOVER ENCRYPTED FILES.TXT and reads the folllowing message:
All your files haue been encrypted?
Your personal identifier
0047222861956585461***
5149137699028847356***
3395271179543076584***
0225576062675531759***
2241229884097711411***
5175955091113238801***
All your files haue been encrypted due to a security problem ***
write us to the e-mail: [email protected]
You haue to pay for decryption in Bitcoins. The price **
we will send you the decryption tool that will decrypt ***
If you can’t contact us by mail: [email protected] You ***
[email protected]
Free decryption as guarantee
Before paying you can send to us up to 3 files for fre***
contain valuable information and their total size must ***
The ransomware note is relatively standard in comparison to other similar threats. The Amnesia2 virus code crafts a very long identifier that is comprimised of randomly-generated strings along with numbers derived from system information. Examples of harvested information include hardware components, unique machine ID and other values.
The computer criminals behind the Amnesia2 virus request the victims to contact them by sending an email to a hacker-designated address. The ransomware sum is not specified, this is a popular strategy used to extort the victims. The computer criminals can adjust the price of decryption based on the contents of the affected user data. Like most ransomware the sum is requested in the Bitcoin digital currency which offers anonymous and practically untraceable transactions. To coerce the users to pay the hackers, the criminals offer 3 free decryption instances.
There are two email addresses associated with the captured samples: [email protected] and [email protected].
Remove Amnesia2 File Virus and Restore Data
Amnesia2 Virus – Manual Removal Steps
WARNING! Manual removal of Amnesia2 file virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
DOWNLOAD Amnesia2 Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Recover Encrypted Files
WARNING! All files and objects associated with Amnesia2 virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



