Our Websearch.live browser hijacker removal guide shows how victims of the dangerous computer virus can effectively restore their computers of the threat.
Remove Websearch.live Redirect and Restore PC
Manual Removal Guide
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Symptoms and Consequences of Websearch.live Infection
The websearch.live browser hijacker is dangerous computer threat that has been found to infect computers around the world. The current samples associated with it are being delivered primarily by toolbars and browser plugins. Upon infection with them the victims will find that the settings of their web applications are changed to redirect to the hacker-controlled site. The modifications include the default home page, new tabs page and search engine.
To maximize effectiveness the hackers usually include support for all popular browsers including the following: Mozilla Firefox, Google Chrome, Internet Explorer, Opera and Safari. As a side consequence of the infections in most cases the hackers also bundle malware code that is able to retrieve private data from the apps. Examples include any stored bookmarks, history, passwords, settings and account credentials. The information can be retrieved by the hackers and used in crimes like financial abuse and identity theft.
One of the main goals of the criminals is to make the users interact with the site by providing a familiar looking interface. In the center of the page the hackers have placed a search engine box that provides sponsored results. Any queries show links that do not display the best results but rather hacker-controlled sites or malware.
Below the search engine there is a grid layout of links to popular social media and popular web services. The intent here is to create a site that appears like a legitimate portal. Beware that any interaction with the site, linked services or affiliate network lead to the introduction of tracking cookies.
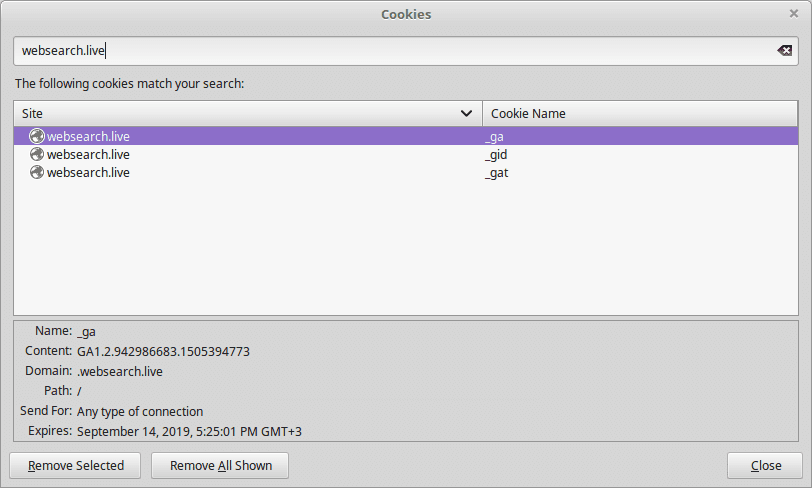
They are used by the hackers to track the behavior of the victims and collect sensitive information about them. More information about this tactic is available from the site’s privacy policy. According to the document the site is operated by a company called Traffisco LLC.
As soon as the data collection process is started the criminals automatically receive two types of information about the users:
- Personal Data ‒ The hackers obtain sensitive information about the victims which inclue their name, address, email address, telephone number, location and etc.
- Anonymous Information ‒ In-depth data collection about the browsers, settings and various configuration options are extracted and used for analytics purposes.
Note that using the tracking cookies and newer technology the criminals can also extract information about the hardware components, user preferences and specific softare configuration. Advanced malware code can be used for other purposes as well, including the following:
- Malware Delivery ‒ The websearch.live browser hijacker can be configured to deploy viruses to the victims, including dangerous ransomware samples.
- Surveillance ‒ By implementing Trojan modules the hacker operators can spy on the users actions, use keyloggers to track their keyboard and mouse input and take over control of the compromised machines at any time.
- Information Harvesting ‒ Advanced forms of the websearch.live browser hijackers can include modules that can download private files.
Where Did My PC Get Infected With The Websearch.live Browser Hijacker?
At the moment the computer criminals are using different tactics to infect victims with the Websearch.live browser hijacker. Depending on the configuration of each attack wave the hackers may opt to customize the associated behavior of the malware code. We presume that the most popular tactics are used with the Websearch.live browser hijacker installations.
An effective way of infecting computer users is the coordination of large-scale email spam campaigns. In most cases social engineering tricks are used alongside the template content to manipulate the targets into infecting themselves with the Websearch.live browser hijacker code. Depending on the scope and intended victims the email messages may be of different types. The operators may opt to use direct hyperlinks that link to a hacker-controlled site where a virus file that carries the infection is found. Another option is to integrate it in the email message itself as a file attachment.
The Websearch.live payload can also be found within infected software installers. They constitute legitimate files that have been downloaded from the vendors sites and then modified to include the malicious code that installs the Websearch.live browser hijacker. They are then usually uploaded to hacker-controlled sites that use images and content that mimic or even clone legitimate site. At the same time P2P networks like BitTorrent can also be utilized to spread the files. They are usually renamed to appear just like the original files. In certain cases it is possible to prevent the infection by unchecking certain checkboxes during the installation process.
Browser hijackers like the Websearch.live are often uploaded under fake developer profiles on the official plugin repositories of the major web browsers. Advanced forms may include videos, screenshots and elaborate descriptions as well as fake comments to boost their reputation.
Simpler forms of distribution usually fall down to redirects via ad networks and scripts found on spam or hacked sites.
Remove Websearch.live Redirect and Restore PC
WARNING! Manual removal of the Websearch.live browser hijacker requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Websearch.live – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Remove Websearch.live from Windows
Here’s a way to remove the program. This method will work regardless if you’re on Windows 10, 8, 7, Vista or XP. Simply selecting the program and pressing delete won’t work, as it’ll leave a lot of small files. That’s bad because these leftovers can linger on and cause all sorts of problems. The best way to delete a program is to uninstall it. Here’s how you can do that:
1. Hold the “Windows” button (It’s between CTRL and Alt on most keyboards) and press “R”. You’ll see a pop-up window.

2. In the textbox, type “appwiz.cpl”, then press“ Enter ”.

3. The “Programs and features” menu should now appear. It’s a list of all the programs installed on the PC. Here you can find the program, select it, and press “Uninstall“.

Remove Websearch.live Virus From Your Browser
Before resetting your browser’s settings, you should know that this action will wipe out all your recorded usernames, passwords, and other types of data. Make sure to save them in some way.
-
1. Start Mozilla Firefox. In the upper right corner, click on the Open menu icon and select “Add-ons“.

2. Inside the Add-ons Manager select “Extensions“. Search the list of extensions for suspicious entries. If you find any, select them and click “Remove“.

3. Click again on the Open menu icon, then click “Options“.

4. In the Options window, under “General” tab, click “Restore to Default“.

5. Select “Search” in the left menu, mark the unknown search engine and press “Remove”.

-
1. Start Google Chrome. On the upper-right corner, there a “Customize and Control” menu icon. Click on it, then click on “Settings“.

2. Click “Extensions” in the left menu. Then click on the trash bin icon to remove the suspicious extension.

3. Again in the left menu, under Chrome, Click on “Settings“. Go under “On Startup” and set a new page.

4. Afterward, scroll down to “Search“, click on “Manage search engines“.

5. In the default search settings list, find the unknown search engine and click on “X“. Then select your search engine of choice and click “Make default“. When you are ready click “Done” button in the right bottom corner.

2. In the “Manage add-ons” window, bellow “Add-on Types“, select “Toolbars and Extensions“. If you see a suspicious toolbar, select it and click “Remove“.

3. Then again in the “Manage Add-ons” window, in “Add-on Types“, Select “Search Providers“. Chose a search engine and click “Set as default“. Select the unknown search engine and click “Remove and Close”.

4. Open the Tools menu, select “Internet Options”.

5. In the “General” tab, in “Home page”, enter your preferred page. Click “Apply” and “OK”.

Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help



