Computer security researchers have discovered a new strain of the Cerber malware family dubbed Updated Red Cerber 2017 ransomware which has already been used in live attacks. Our removal guide will give you the technical details about the new threat and will show you how to easily remove existing infections and protect yourself from possible attacks.
Updated Red Cerber 2017 Ransomware Description
The Cerber threat is not over. The virus has been one of the most popular malware families and its dangers continue to grow. Now security researchers have discovered a new strain known as the Updated Red Cerber 2017 Ransomware.
As Of March 2017 this virus continues to be one of the most popular ransomware strains used by the computer hackers to launch attacks against both individual computer users, companies and government institutions. The fact that the virus engine creates files that resemble legitimate data makes it easier for the virus to evade detection if the security staff have not been trained to look out for such advanced forms of ransomware. In practice it would be very difficult to prevent or restore affected data without the use of a quality anti-spyware solution.
Upon infection with the binary payload dropper the ransomware is downloaded to the local computer. Then the usual behavior pattern is activated. The dropper downloads files that resemble system data and ordinary files. They modify the settings of the Windows operating system and create new processes to create a persistent environment.
Multiple files are dropped on the host computer and Cerber modifies the wscript.exe script host to modify important files located in the %System32% and %Microsoft% directories. Some of them include the following: rsaenh.dll, WScript.exe, WScript.exe.mui, sortdefault.nls, wshom.ocx, stdole2.tlb, KERNELBASE.dll.mui, msxml3.dll.
The Updated Red Cerber 2017 Ransomware was found that it doesn’t delete the shadow volume copies of the infected host. This means that data recovery using suitable software is possible.
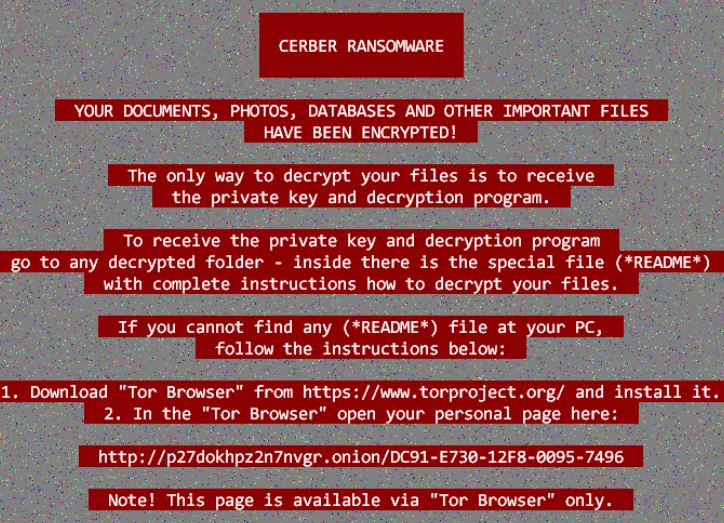
There are no changes to the usual ransomware note it still displays the same contents:
CERBER RANSOMWARE
YOUR DOCUMENTS, PHOTOS, DATABASES AND OTHER IMPORTANT FILES HAVE BEEN ENCRYPTED1
The only way to decrypt your files is to receive
the private key and decryption program.To receive the private key and decryption program
go to any decrypted folder – inside there is the special file (*README*)
with complete instructions how to decrypt your files.If you cannot find any (*README*) file at your PC,
follow the instructions below:1. Download “Tor Browser” from https://www.torproject.org/ and install it.
2. In the “Tor Browser” open your personal page:http://p27dokhpz2n2nvgr.onion/DC91-E730-12F8-0095-7496
Note! This page is available via “Tor browser” only.
Example Red Cerber 2017 Ransomware Infection
Upon infection the malware assigns a custom ID to the target host. This associated each victim computer with its own private decryption key meaning that an universal decryptor would be very difficult to make.
The built-in encryption engine uses a strong AES cipher which is unbreakable without the use of a supercomputer. Infected computers should resort to the use of a trusted anti-spyware tool to mitigate the effects of the virus and protect themselves in any future attacks.
It is known that the Cerber ransomware family targets the most widely used file types – all kinds of multimedia data (photos, videos, music), databases, office documents and etc.
We would like to give you an example of an actual attack. A victim computer has been infected with the Updated Red Cerber 2017 Ransomware strain and has received the .ba99 extension .
Here are how the files are being affected:
- C:\eula.txt to asdq23rvsa.ba99
- C:\mydocument.doc to vepr124zac.ba99
- C:\mydocument.docx to qsa04pr0ht.ba99
- C:\examplefile.hwp to oqcft9b0ra.ba99
- C:\documentfile.pdf to zo59cxorp1.ba99
- C:\mybandmusic.mp3 to nekq4m69bf.ba99
- C:\presentation.pptx to 75xodjaqcp.ba99
- C:\thefinvoces.xls to 0ho2pajwvp.ba99
Updated Red Cerber 2017 Ransomware Distribution
The Cerber uses the combination of the Rig (RIG-V version) exploit kit and the Nemucod payload dropper (also known as the Nemucod downloader).
These two hacking utilities use spam email messages that are sent in bulk to infect the victims using .JS files. They are concealed to appear as legitimate documents, finacial statements or other types of data that the user can access.
In some of the captured malware samples the malicious files have been placed in archives such as .rar or .zip . The criminal operators of the new Cerber strain have used the social engineering trick of placing the password in the body of the text to appear as a legitimate email.
Other sources of infection include infected and counterfeit software installers, games and updates downloaded from untrusted download sites or BitTorrent trackers.
How To Prevent Further Red Cerber 2017 Infections?
The method of infections of Red Cerber isn’t a complex one. The crooks simply rely on simple tricks that can’t fool a system with good anti-malware protection on his computer. You can download a good tool from this link:
Summary
| Name |
Updated Red Cerber 2017 |
| File Extensions |
Four-character randomly generated string |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove Updated Red Cerber 2017 ransomware with the help of an anti-malware tool. |
|
Manual Solution |
Updated Red Cerber 2017 ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
Updated Red Cerber 2017 Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Updated Red Cerber 2017 Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
-
1) Use present backups
2) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.



