Spora ransomware virus has recently been discovered to deliver a serious damage to infected hosts in all Windows versions. Once activated, it encrypts important files and demands a fee in exchange for a decryption key. Spora is quite flexible – depending on the infected computer and the victim, it may display a message on a specific language, requesting a custom for that victim amount.
Manual Removal Guide
Recover Encrypted Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Spora Ransomware Virus Description
Spora ransomware virus is a newly discovered malware family that will probably take on popularity by spawning new variants. The core threat contains a lot of features that are not typical of other ransomware and this is why it it important to know all and understand how damaging it can be.
The analyses of Spora virus samples show that it can create new directories and files, write remote processes and spawn a lot of processes during the infection flow. The ransomware is likely to drop and create some of its malicious files in the following folders:
- %APPDATA%
- %LOCALAPPDATA%
- %System32%
- %TEMP%
The Spora virus is written in the C programming language and packed using an UPX executable packer. A major distinction between this and other ransomware families is that it doesn’t rename the affected files by using a specific extension. The virus just employs a powerful AES + RSA encryption engine which targets specific target user files, generates private decryption key and urge the victims to transfer a ransomware payment.
The full list of file extensions targeted by Spora ransomware virus includes:
.xls, .doc, .xlsx, .docx, .rtf, .odt, .pdf, .psd, .dwg, .cdr, .cd, .mdb, .1cd, .dbf, .sqlite, .accdb, .jpg, .jpeg, .tiff, .zip, .rar, .7z, .backup
When these file extensions are detected, Spora encrypts them and files are no longer able to be opened. If the encryption process is successful, Spora generates an .html file, placing it in all folders that contain encrypted files. This file contains a message from cyber criminals. The text presents instructions how to pay the ransom for the recovery keys. Depending on the victim’s geographical location the virus creates a different ransom note according to the following pattern:
- USXXX-XXXXX-XXXXX-XXXXX.HTML – for victims located in the United States of America.
- RUXXX-XXXXX-XXXXX-XXXXX.HTML – for victims located in Russia
- FRXXX-XXXXX-XXXXX-XXXXX.HTML – for victims located in France.
Other country code prefixes are used depending on the location. A typical Spora ransomware note looks like this:

And it reads the following:
SPORA rANSOMWARE
All your work and personal files were encrypted
To restore data, obtaining guarantees and support, follow the instructions in your account.
Personal Area
xxxxs: //spora.bz>
USXXX-XXXXX-XXXXX-XXXXX
What happened?
1. Only we can restore your files.
Your files have been modified using RSA-1024 algorithm. Reverse recovery process is called decryption. This requires your unique key. Choose or “hack” it is impossible.
2. Do not turn to intermediaries!
All recovery keys stored only in our country, respectively, if you someone will offer to restore the information, in the best case, he first buys the key here, then you will sell it at a premium.
If you can not find your Sync Key
Click here.
The Spora ransomware virus deletes all Shadow Volume Copies of the affected machine which prevents data recovery. This is done using the following command:
vssadmin.exe delete shadows /all /quiet
In addition it disables the Windows Startup Repair and changes the BootStatusPolicy which is a serious system modification by issuing the following commands:
bcdedit.exe /set {default} recoveryenabled no
bcdedit.exe /set {default} bootstatuspolicy ignoreallfailures
The virus’s engine also scans for popular security software and employs several stealth detection techniques to install itself to the target host. It is able to harvest important system information.
In order to display the ransom message during the infection flow and control its automatic start each time the Windows starts up, Spora ransomware may create and change values under the following registry keys:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Each infected user is greeted with a gateway crafted page which uses the TOR anonymous network. Each host receives their own unique victim ID which allows the computer users to buy their own dedicated private decryption key.
The criminals who operate the Spora ransomware allow for several payment “packages” that have a different price depending on the service offered:
- FULL RESTORE – Fully restores the affected files.
- IMMUNITY – Guarantees immunity from malware.
- REMOVAL – Removes the malicious payload from the system.
- FILE RESTORE – Restores individual files.
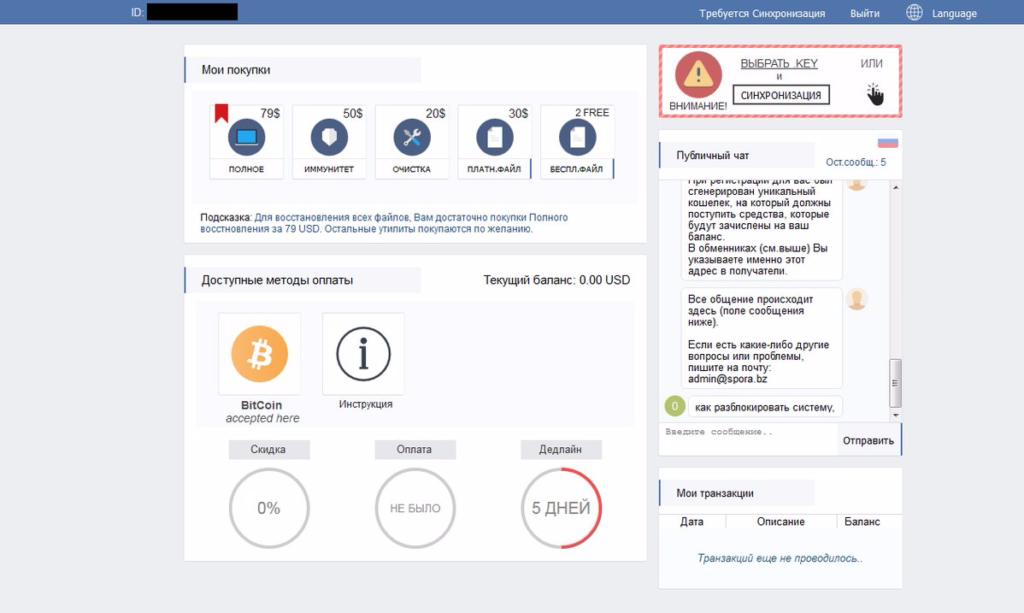
The price for the “FULL RESTORE” option could vary among $79 and $280 and when victim wants to restore only individual files he should pay $30 for each. The “REMOVAL” is offered for an extra $20. Cyber criminals also offer the free decryption of 2 files as another way to temp victims sending the ransom at the Bitcoin address.
We should acknowledge that offering unique payment options is really tricky and is likely to attract more victims. However, better avoid trusting cyber criminals who tell you that guarantee immunity from malware and security just after they have compromised all your important data as well as the whole system. Contacting them is also an option that is better to be avoided.
The security experts have noticed that the gateway page also has a built-in live chat function which allows the victims to communicate with the virus operators. It was observed that they have answered in a prompt and timely manner.
Furthermore, all victims have a deadline for the money transaction displayed on Spora’s website. Once the time comes to an end the unique decyption keys are permanently deleted. However, according to information based on real negotiations with the extortionists standing behind Spora ransomware attacks, they are inclined to extend the time for the ransom paying.
If you are a victim of Spora ransomware you may be tempted to purchase the decryption key but doing so is one of the ways to encourage the crooks to continue and get better at their malicious operations.
Spora Ransomware Distribution
The first Spore ransomware samples were identified in the beginning of January 2017. Today Spora ransomware propagators continue to spread the malicious Spora payloads via various attack vectors searching for new victims. This is a multi-language computer threat which is used to attack various individuals and companies worldwide.
Primary infection methods include spam email campaigns and infected software bundles. They usually carry the binary payload which contains the dangerous Spora ransomware.
Right now a major email spam campaign is underway which uses phishing tactics to infect hosts. The Spora ransomware is contained in messages that pose as coming from 1C, a very popular accounting software used in Russia and other former USSR countries. The subjects and contents pose as containing invoices and some example filenames include Экспорт из 1С.a01e743_рdf.hta which translates to “Scan-copy _ 10 Jan 2017“. They use double extensions, one of which is likely to be hidden as a way to trick the user into thinking that the file is an actual document file.
Other distribution techniques include malicious ads, browser hijackers and exploit kit attacks. Spora ransomware strains have been identified on various forums and other types of online communities. The virus is usually found in files that use the following naming patterns:
- special_phrase_in_English.random_chars_pdf.hta
- специальная_фраза_на_русском.random_chars_pdf.hta
- random.hta
Yet another infection vector of Spora ransomware virus distribution appears to be compromised websites. Security researchers have reported that the malicious Spora payloads are distributed via websites injected with nasty scripts by hackers. Once a victim lands on a compromised webpage the injected scripts can use an exploit kit like Rig EK that easily determines if the computer has any vulnerable browser-based applications. Then it sends an exploit for any vulnerable application, executes it as a background process and infects the victim’s host with Spora ransomware.
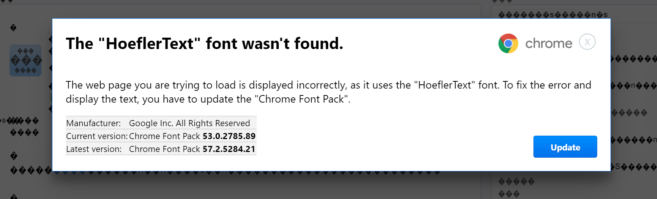
Recently a Google Chrome font update scam was used for the Spora ransomware distribution. The campaign is designed to display a pop up to Google Chrome users. The pop up says “The HoeflerText font wasn’t found” and prompts users to update their browsers with the missing font. However, once they download and run the file a Spora ransomware infection occurs.
Remove Spora Ransomware Virus and Restore Encrypted Files
WARNING! Manual removal of the Spora ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Spora Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover Encrypted Files
WARNING! All files and objects associated with Spora ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD Spora Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



