A new social engineering attack tries to trick you into installing malicious software. Its goal is to convince you that your Google Chrome browser is missing a critical component. The scam is designed to mess the content of a website you are visiting and then prompts you to download and install a missing Google Chrome font update that will help you to read the blog.
How could you recognize the scam?
“The font wasn’t found” Google Chrome Malware Scam
“The ‘HoeflerText’ font wasn’t found” – this is how the new Chrome hacking scam presents itself. The malicious scam compromises poorly secured websites by using JavaScript code which transforms the text on the pages. Thus when you land on a hacked site you see a messed text with symbols and other random characters. To fix the problem, you are prompted to update the “Chrome Font Pack”. The full text on the pop-up reads:
The “HoeflerText” font wasn’t found.
The web page you are trying to load is displayed incorrectly as it uses the “HoeflerText” font. To fix the error and show the text, you have to update the “Chrome Font Pack”.
Manufacturer: Google Inc. All Rights Reserved
Current version: Chrome Font Pack 53.0.2785.89
Latest version: Chrome Font Pack 57.2.5284.21
The good design and the implementation of the hack are likely to make you presume that you really need to update your browser. All features of the scam – the jumbled text on the webpage, the “missing” font HoeflerText, which is a real one, the clean well-formatted dialog box, the correct Chrome logo, the provided version numbers that give you the wrong idea your Chrome browser is somehow out-of-date, the proper spelling and grammar could encourage you to take further actions.
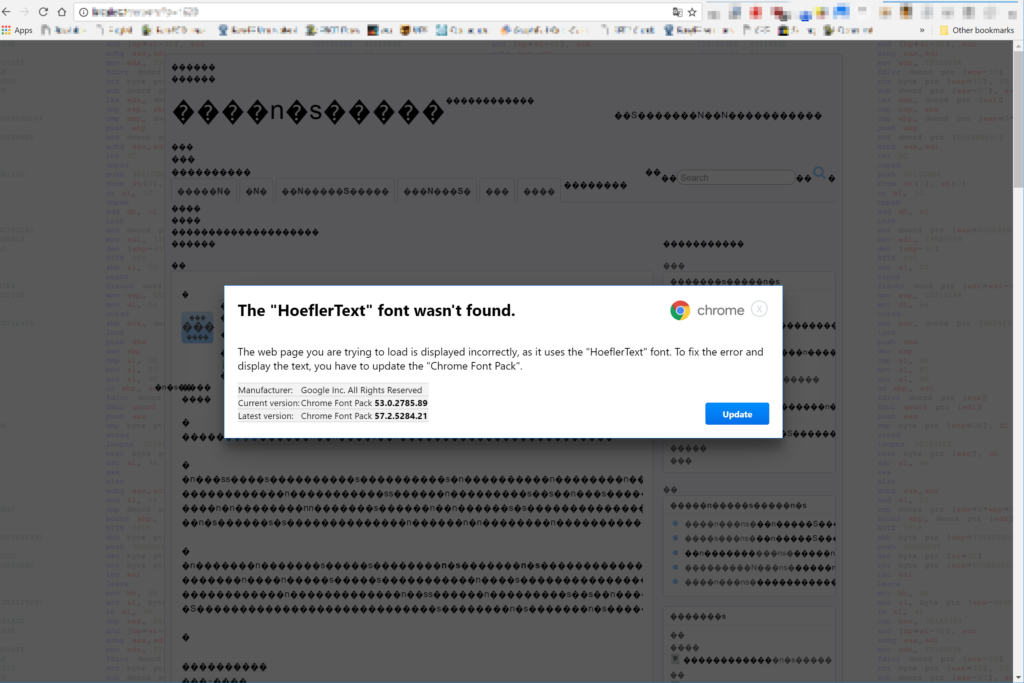
There is also an “Update” button at the bottom right corner which color is designed to be the same shade of blue used by Google. The shape also seems to be correct. However, if you click it, you will download a Trojan dropper on your PC.
The good news is the malicious software doesn’t execute itself automatically. Only your manual double-click on the app could trigger the malware infection.
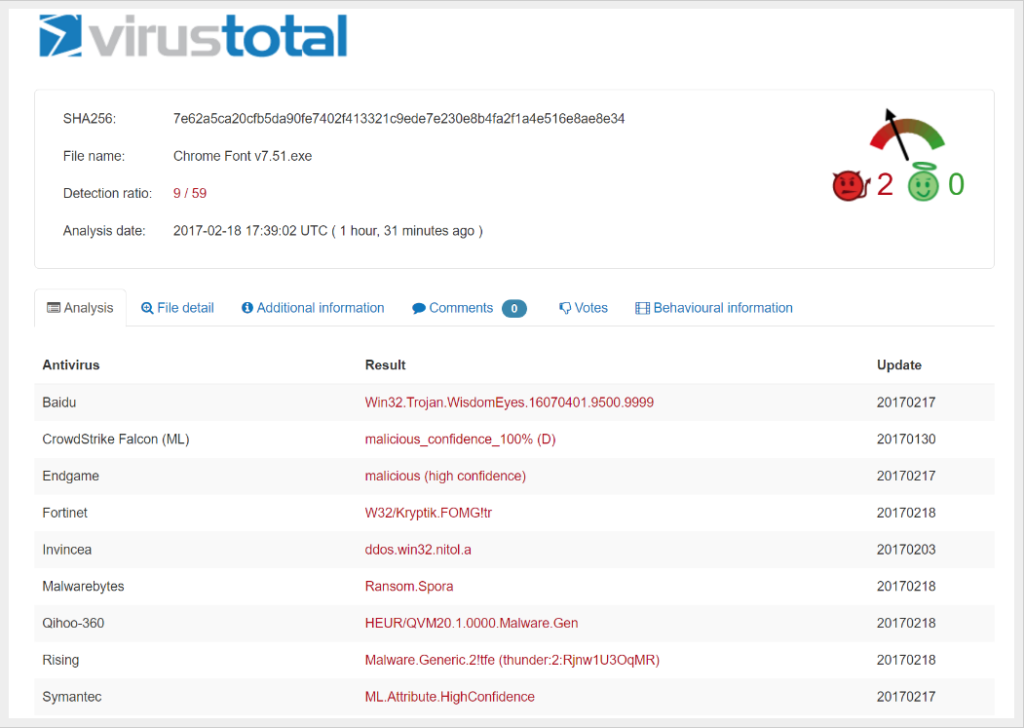
The bad news is that several security researchers have detected the highly sophisticated Spora ransomware to be one of the malware threats spread via this Google Chrome Font Update scam.
Traits That Reveal the Sneaking Purpose of Google Chrome Font Update
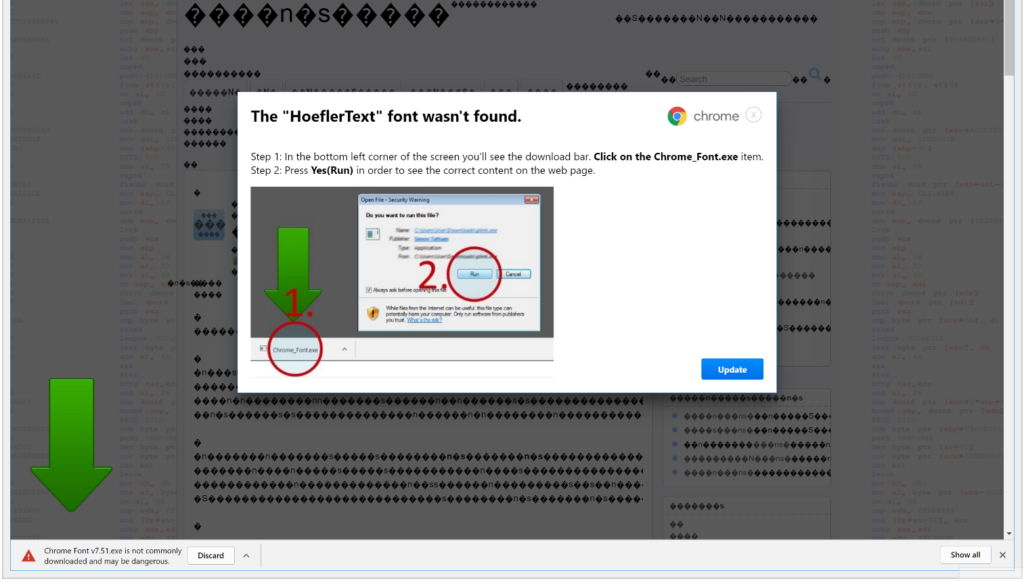
Once you click the “Update” button, you will download a file called “Chrome Font v7.5.1.exe” that will appear in your browser bar. The file will be saved to the default download folder. The pop-up screen displayed on the webpage will then show you “helpful” instructions how to find the file and encourage you to run it. And if you do it your computer becomes infected.
Trait one: The filename issue
The started download after clicking the “Update” button results in an executable file with name “Chrome Font v7.5.1.exe” on your computer. OK, but why then the “helpful” instruction image guides you how to run a file “Chrome_Font.exe“.
Ok, let’s guess that you download the suspicious file, but you do not run it yet. How could you prevent malware infection?
Find the exact folder location of the downloaded file. Then visit the website of VirusTotal and upload it for analysis. The antivirus scanners in its database will correctly identify whether the file is malicious one or not. The results will help you to make the right decision.
Another secure and reliable way to prevent malware infection is to have installed up-to-date professional anti-malware software.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Trait two: This file isn’t downloaded very often
Even though that Chrome doesn’t flag the download as malware, the browser blocks the file with a warning message “this file isn’t downloaded very often”. This is a standard warning and next time you notice it better skip the download process of the file. The timely reaction could save your computer from ransomware infection like Spora.
You already know everything you need to prevent a malware infection through Chrome Font Pack scam. Be cautious and if you see a pop-up that urges you to download a Chrome Font Pack and update your browser close the website immediately and do not visit it again. Don’t be scammed, stay cyber safe.



