Our searchtab.net browser hijacker removal guide shows how victims of the dangerous computer virus can effectively restore their computers of the threat.
Remove Searchtab.net Redirect and Restore PC
Manual Removal Guide
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Symptoms and Consequences of Searchtab.net Infection
Searchtab.net is a typical case of a browser hijacker that is usually deployed to victim computers via a malicious browser plugin infection. Such computer threats typically tend to change important settings of the installed web browsers and redirect to a hacker-specified address. In this example this is the primary hacker-controlled domain searchtab.net.
Upon infection important settings modifications are made which target the most popular web browsers. The list includes Microsoft Edge, Mozilla Firefox, Internet Explorer, Google Chrome, Opera and Safari. Once this is done important settings are changed, including the default home page, search engine and new tabs page. This is also the most obvious sign of a virus infection which is what this is.
Like other similar threats when the visitors open the site or are redirected to it several tracking cookies are imposed. They track the site interactions and record detailed information on the victims which is then relayed to the hacker operators. As the primary aim of the criminals is to redirect the visitors to the site in all cases data is recorded from each visitor, even if they are have simply opened and then closed the page.
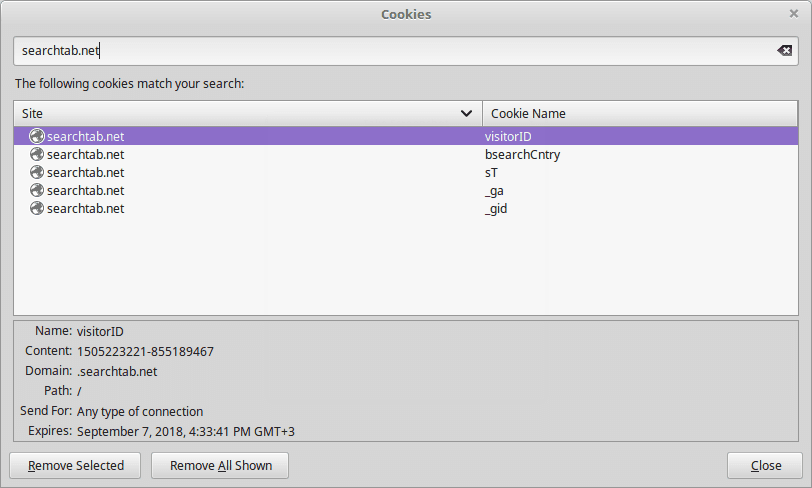
The tracking cookies gather two main types of data:
- Personal Information ‒ By using the cookies personally-identifiable data about the victims is harvested. Examples include the address, real name, age, location, preferences and other similar metrics.
- Anonymous Data ‒ Various analytical information is retrieved from the web browsing sessions to make adjustments to the web site and optimize the content.
As always templates are being used to design the main website. The top image shows the name of site, below it a small search engine is placed. Underneath it are placed two lists of popular terms which are dynamically adjusted to reflect the interest of the web audience. The bottom navigation bar features the four hyperlinks that are associated with the site itself, namely: About Us, Terms of Use, Privacy and Contact Us.
A careful review reveals that the site is being operated by a company called Apply Advanced Mobile Technologies Ltd. The short introductory description reveals the following statement:
SearchTab is a powerful independent search feed that offers phenomenal coverage and performance for Advertizers and Publishers, and gives accurate and relevant results to users.
As a result it is evident that the site is made primarily to provide marketing agencies with a useful platform to place sponsored links. The searchtab.net browser hijacker is an useful tool for targeting users with content that may not provide the best results. The operators state that they are open for negotiation about links placement for both media publishers and advertisers.
Combined with the fact that every site visitors is assigned an unique user ID (UUD) which profiles the interests of the victims makes it an useful platform for content providers.
Where Did My PC Get Infected With The Searchtab.net Browser Hijacker?
At the moment the computer criminals are using different tactics to infect victims with the Searchtab.net browser hijacker. Depending on the configuration of each attack wave the hackers may opt to customize the associated behavior of the malware code. We presume that the most popular tactics are used with the searchtab.net browser hijacker installations.
An effective way of infecting computer users is the coordination of large-scale email spam campaigns. In most cases social engineering tricks are used alongside the template content to manipulate the targets into infecting themselves with the searchtab.net browser hijacker code. Depending on the scope and intended victims the email messages may be of different types. The operators may opt to use direct hyperlinks that link to a hacker-controlled site where a virus file that carries the infection is found. Another option is to integrate it in the email message itself as a file attachment.
The searchtab.net payload can also be found within infected software installers. They constitute legitimate files that have been downloaded from the vendors sites and then modified to include the malicious code that installs the searchtab.net browser hijacker. They are then usually uploaded to hacker-controlled sites that use images and content that mimic or even clone legitimate site. At the same time P2P networks like BitTorrent can also be utilized to spread the files. They are usually renamed to appear just like the original files. In certain cases it is possible to prevent the infection by unchecking certain checkboxes during the installation process.
Browser hijackers like the searchtab.net are often uploaded under fake developer profiles on the official plugin repositories of the major web browsers. Advanced forms may include videos, screenshots and elaborate descriptions as well as fake comments to boost their reputation.
Simpler forms of distribution usually fall down to redirects via ad networks and scripts found on spam or hacked sites.
Remove Searchtab.net Redirect and Restore PC
WARNING! Manual removal of the Searchtab.net browser hijacker requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Searchtab.net – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Remove Searchtab.net from Windows
Here’s a way to remove the program. This method will work regardless if you’re on Windows 10, 8, 7, Vista or XP. Simply selecting the program and pressing delete won’t work, as it’ll leave a lot of small files. That’s bad because these leftovers can linger on and cause all sorts of problems. The best way to delete a program is to uninstall it. Here’s how you can do that:
1. Hold the “Windows” button (It’s between CTRL and Alt on most keyboards) and press “R”. You’ll see a pop-up window.

2. In the textbox, type “appwiz.cpl”, then press“ Enter ”.

3. The “Programs and features” menu should now appear. It’s a list of all the programs installed on the PC. Here you can find the program, select it, and press “Uninstall“.

Remove Searchtab.net Virus From Your Browser
Before resetting your browser’s settings, you should know that this action will wipe out all your recorded usernames, passwords, and other types of data. Make sure to save them in some way.
-
1. Start Mozilla Firefox. In the upper right corner, click on the Open menu icon and select “Add-ons“.

2. Inside the Add-ons Manager select “Extensions“. Search the list of extensions for suspicious entries. If you find any, select them and click “Remove“.

3. Click again on the Open menu icon, then click “Options“.

4. In the Options window, under “General” tab, click “Restore to Default“.

5. Select “Search” in the left menu, mark the unknown search engine and press “Remove”.

-
1. Start Google Chrome. On the upper-right corner, there a “Customize and Control” menu icon. Click on it, then click on “Settings“.

2. Click “Extensions” in the left menu. Then click on the trash bin icon to remove the suspicious extension.

3. Again in the left menu, under Chrome, Click on “Settings“. Go under “On Startup” and set a new page.

4. Afterward, scroll down to “Search“, click on “Manage search engines“.

5. In the default search settings list, find the unknown search engine and click on “X“. Then select your search engine of choice and click “Make default“. When you are ready click “Done” button in the right bottom corner.

2. In the “Manage add-ons” window, bellow “Add-on Types“, select “Toolbars and Extensions“. If you see a suspicious toolbar, select it and click “Remove“.

3. Then again in the “Manage Add-ons” window, in “Add-on Types“, Select “Search Providers“. Chose a search engine and click “Set as default“. Select the unknown search engine and click “Remove and Close”.

4. Open the Tools menu, select “Internet Options”.

5. In the “General” tab, in “Home page”, enter your preferred page. Click “Apply” and “OK”.

Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help



