An infection with the dangerous UEFI ransomware virus leads to serious security issues. With our removal guide, victims can try to restore and protect their computers.
Manual Removal Guide
Files Recovery Approaches
Skip all steps and download anti-malware tool that will safely scan and clean all harmful files it detects on your PC.
SpyHunter is a Windows application designed to scan for, identify, remove and block malware, potentially unwanted programs (PUPs) and other objects. By purchasing the full version, you will be able to remove detected malware instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
UEFI Ransomware Description
The UEFI Ransomware is a concept virus which has been demonstrated as part of a specialist security conference. Further details about the virus are going to be disclosed in an upcoming conference.
However, with the currently known data about it, we have constructed a removal guide which will help users protect themselves from any possible abuse. First of all, all security experts should consider that the virus is based on the concept of infecting the UEFI firmware. This is the next-generation replacement for the BIOS (Basic Input/Output System) which initializes the hardware during the boot process.
By infecting this part of the system the hackers can potentially even cause physical damage to the hardware components by configuring dangerously high voltages to the memory or processor (overclocking them). Proof-of-concept demonstrations were made available in which we can see victim machines that run an Intel Skylake CPU with Microsoft Windows 10 Enterprise (build 1607) with all updates installed. In addition, all security features have been activated: Secure Boot, Virtual Secure Mode (VSM) and the Device Guard running with its default policy. Over the last few years, there have been numerous publications and warnings of UEFI vulnerabilities which can lead to such infections. All of them allow computer hackers to compromise the security of their targets and as a consequence gain a very deep access to the machines.
There are several defense mechanisms that are going to be unveiled in the upcoming talk that can guard against possible intrusions. Still the use of specialist anti-malware solutions can enforce a strng protective layers that can prevent such virus infections. A succesful UEFI ransomware attack can lead to the following consequences:
- Deep Malware Infections – Such infections can be extremely difficult to remove after a succesful intrusion. The UEFI firmware is in control of the hardware and it is responsible for a lot of low-level system functions.
- Sabotage – Such ransomware can modify vital settings which can destroy hardware components.
- Hardware Persistence – By infecting the UEFI firmware the virus code can be very difficult to remove.
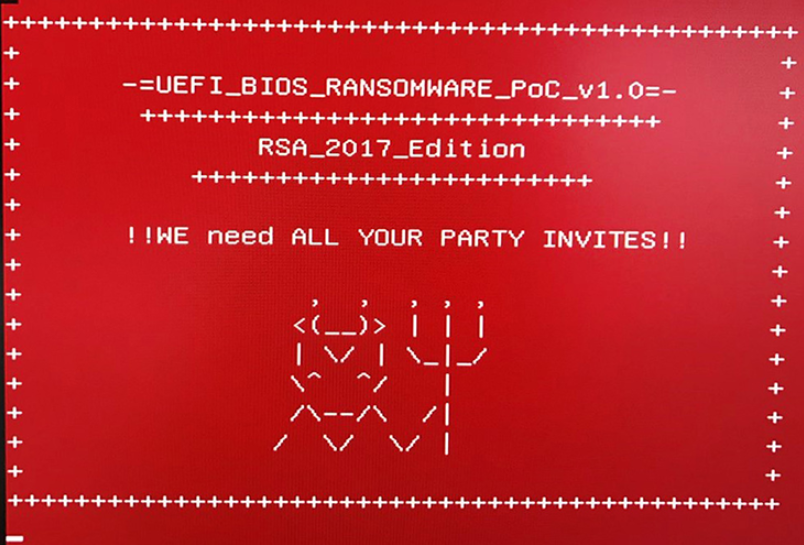
The shown proof-of-concept code displays a ransomware note when the computer boots with the following message:
-=UEFI_BIOS_RANSOMWARE_PoC_v1.0=-
+++++++++++++++++++++++++++++++RSA_2017_EDITION
+++++++++++++++++++++++++++++!!WE need ALL YOUR PARTY INVITES!!
It’s interesting to note that one of the main reasons for implementing the UEFI firmware over the old BIOS standard was the heightened security measures. This virus illustrates that even with different security features enabled such dangerous attacks are possible. Fortunately, to this date, no actual attack campaigns have reported.
UEFI Ransomware Distribution
The infection can be performed via different complex methods. One of them includes several code execution vulnerabilities which breaks the virtualization isolation provided by the Intel Software Guard Extensions (SGX) and other related technologies.
During a complex multi-stage payload delivery the UEFI ransomware can infect via several layers of exploits that deliver the dangerous payload. The demonstrated infection route follows this complex strategy:
- First-stage of attack (OS User-Mode) – The first-stage attack comes from an app exploit which delivers a dangerous payload that starts the infection process. These are remote code exploits which trigger an escalation of privileges for the virus.
- Second-stage attack (OS Kernel-Mode) – The payload with elevated privileges runs the next part of the attack which infects the Hardware Abstraction Services.
- UEFI Infection – The final stage involves writing the dangerous code to the UEFI firmware by flashing it via a rootkit.
Another attack scenario relies on sending out a phishing email message which poses as an important notification. The file in question is a Microsoft Word document containing an embedded PowerShell dropper. Like other similar threats, it shows a prompt that requests from the victim to engage the built-in macros. Once this is achieved the dropper downloads a BIOS updater which flashes the UEFI ransomware to the firmware.
Summary of the UEFI Ransomware
| Name |
UEFI Ransomware |
| File Extensions |
Varies |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove UEFI Ransomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
UEFI Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
Remove UEFI Ransomware Ransomware Virus and Restore PC
Please note that paying the requested ransom fee to cyber criminals does not really solve your problem with UEFI Ransomware crypto virus. In fact, you only encourage hackers to continue spreading ransomware of this kind. Instead, you must remove the threat immediately, and only then look for optional ways to recover your data.
WARNING! Manual removal of UEFI Ransomware ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
DOWNLOAD SpyHunter Anti-Malware ToolUEFI Ransomware Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps below are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover Encrypted Files
WARNING! All files and objects associated with UEFI Ransomware ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
SpyHunter is a Windows application designed to scan for, identify, remove and block malware, potentially unwanted programs (PUPs) and other objects. By purchasing the full version, you will be able to remove detected malware instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



