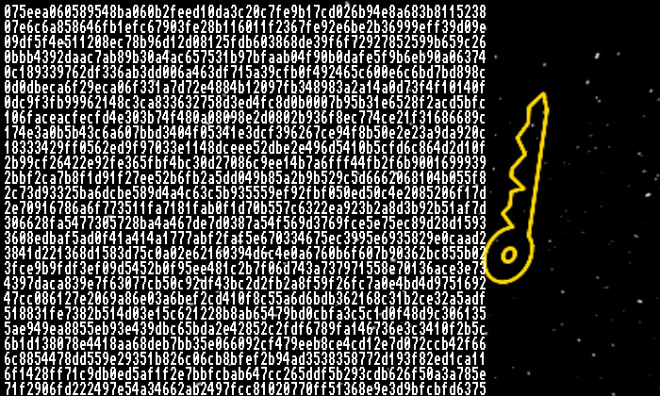
Two security researchers under the aliases My123 and Slipstream reported this week that Microsoft published by accident the security key to the Secure Boot feature in Windows. This allows anyone backdoor access and the ability to disable the UEFI firmware security features. The leak also lets malicious users load unsigned or self-signed code into the target systems. This is a very dangerous situation as it allows viruses and other computer vulnerabilities access to the system.
What is Secure Boot
Secure Boot is a security standard for Windows computers that uses verified digital signatures installed in system’s UEFI firmware. This is the core software that controls the basic computer components and communicates with the operating system (e.g. Microsoft Windows). With Secure Boot enabled the computer first checks that the firmware is signed by Microsoft and only after successful check proceeds with the bootup process.
The computer may not boot if the operating system, optional ROM drivers or applications are not trusted by the Secure Boot database. Some manufacturers also produce kernel-mode drivers for some components that must be signed to function properly.
For most computers, the Secure Boot option can be disabled in the UEFI Firmware setup tool. The Secure Boot database, however, cannot be changed by the user; it can only be amended by the PC manufacturer.
Secure Boot Is No Longer Secure
The two security researchers reported that Microsoft published the Secure Boot key in Windows update bulletins. This move originally posed to present debugging and testing functions. The problem is that it’s practically impossible to properly amend this issue. Most of the PC manufacturers, hardware vendors, and recovery media depend on the Secure Boot key to install and run the Windows operating system correctly.
Microsoft has tried to correct the problem in the MS-16-094 advisory in which they blacklisted some of the relevant security policies and procedures. Many123 and Slipstream stated that this does not offer complete protection because an attacker may still be able to manipulate the boot manager sequence and bypass the Secure Boot policy. The second attempt at fixing the problem has appeared in MS16-100 in which the Secure Boot database has been updated with additional hashes. Once again the two researchers commented that this does not amend the security vulnerability.
Secure Boot Failure
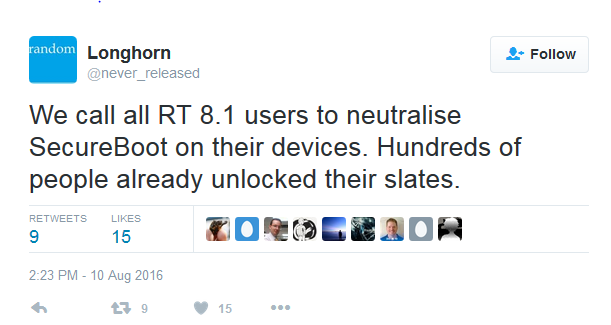
The researcher under the alias My123 posted on his Twitter page that disabling Secure Boot on Windows 8.1 RT devices can “unlock” them. In response to user comments about installing alternative operating systems, the researcher stated that “we are working on alternate OSes. Stay tuned.” They responded that the installation of Gnu/Linux distributions on Surface RT devices could be a valid possibility in the near future.



