The vCrypt1 Virus Impact on an Infected PC
The vCrypt1 virus is a new version of the vCrypt. It drops the file vCrypt.exe on the system that starts the infection process once it is running on the system. vCrypt1 ransomware is a data locker ransomware similar to Extractor and Dharma Wallet.
Such kind of malware primarily aims to find files of particular types on the PC and encrypts them with strong cipher algorithm. It is known that the vCrypt1 uses the XOR algorithm to modify the following nineteen file types:
.ai, .cdr, .cdw, .doc, .docx, .dwg, .dxf, .jpg, .mdb, .mdf, .ods, .odt, .pdf, .ppt, .pptx, .psd, .rtf, .xls, .xlsx
The most visible impact of vCrypt1 virus infection is the extension .vCrypt1 that stands after the original file name and extension. Furthermore, the affected files look corrupted and cannot be accessed by any software except with a decryptor possessed by the hackers. Hackers demand to contact them at [email protected] and pay a ransom in exchange for the decryptor and the unique decryption key.
They have designed the ransomware to drop a file called КАК_РАСШИФРОВАТЬ_ФАЙЛЫ.txt as a way to inform victims what happened with their data and how they could restore their files.
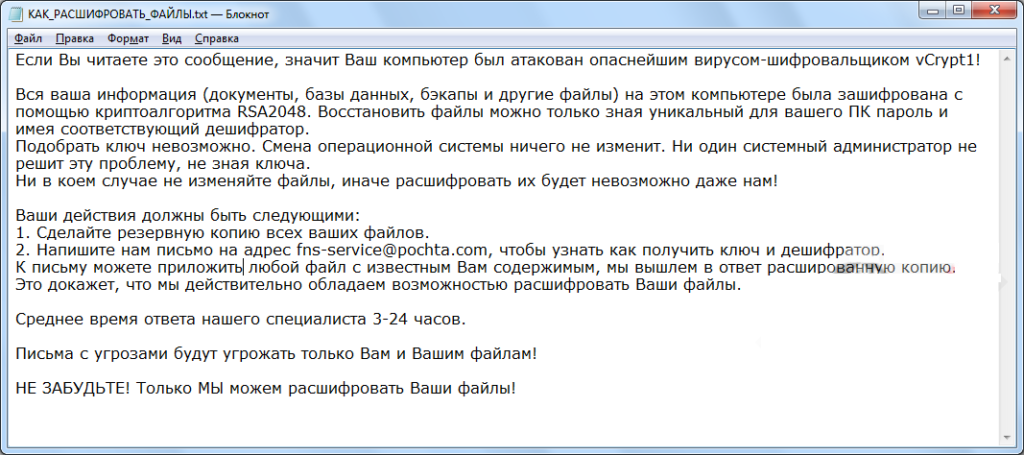
The analyzed vCrypt1 samples reveal that the text on the note is written in Russian and all that it reads is:
Если Вы читаете это сообщение, значит Ваш компьютер был атакован опаснейшим вирусом-шифровальщиком vCrypt1!
Вся ваша информация (документы, базы данных, бэкапы и другие файлы) на этом компьютере была зашифрована с помощью криптоалгоритма RSA2048. Восстановить файлы можно только зная уникальный для вашего ПК пароль и имея соответствующий дешифратор.
Подобрать ключ невозможно. Смена операционной системы ничего не изменит. Ни один системный администратор не решит эту проблему, не зная ключа.
Ни в коем случае не изменяйте файлы, иначе расшифровать их будет невозможно даже нам!
Ваши действия должны быть следующими:
1. Сделайте резервную копию всех ваших файлов.
2. Напишите нам письмо на адрес [email protected], чтобы узнать как получить ключ и дешифратор.
К письму можете приложить любой файл с известным Вам содержимым, мы вышлем в ответ расшированную копию.
Это докажет, что мы действительно обладаем возможностью расшифровать Ваши файлы.
Среднее время ответа нашего специалиста 3-24 часов.
Письма с угрозами будут угрожать только Вам и Вашим файлам!
НЕ ЗАБУДЬТЕ! Только МЫ можем расшифровать Ваши файлы!
With the help of an online translator it becomes clear that in English the ransom message informs the following:
If you are reading this message, then your computer was attacked by the most dangerous virus-encryptor vCrypt1!
All of your information (documents, databases, backups and other files) on this computer was encrypted using the RSA2048 cryptographic algorithm. You can recover files only knowing a unique password for your PC and having the appropriate decoder.
You can not find the key. Changing the operating system will not change anything. No system administrator will solve this problem without knowing the key.
Do not change the files at all, otherwise it will be impossible to decipher them even to us!
Your actions should be as follows:
1. Make a backup of all your files.
2. Write us a letter to [email protected] to find out how to get the key and decoder.
To the letter you can attach any file with the content known to you, we will send an decrypted copy in response.
This will prove that we really have the ability to decrypt your files.
The average response time of our specialist is 3-24 hours.
Threatened letters will threaten only you and your files!
DO NOT FORGET! Only we can decrypt your files!
There is a misleading moment that spoofs victims of data encryption with the RSA-2048 algorithm. However, .vCrypt1 files are encrypted with the help of XOR. It is better to avoid any negotiations with the criminals and clean the PC as soon as possible.
vCrypt1 Virus Distribution Methods
The malicious samples that trigger vCrypt1 ransomware virus may be delivered via a word document attached to an email or sent via a message on any social media channel. It is also possible the document to be added to a ZIP archive file. Once the file is started on the PC, it may ask you to enable macros which will start the vCrypt1 infection. The document may also be designed to display a system notification that misleads victims to click the “OK” button in order to open the content of the file.
Another commonly used trick of ransomware and malware dissemination is a spoofed link that redirects to a crafted web page that can automatically download the payloads on the PC. The sender itself may impersonate well-known companies and services.
However, the malicious traits can be revealed almost always. Online scanning services like ZipeZip (free online archive extractor and malware scanner) and VirusTotal (a free service that analyzes suspicious files and URLs) can help the detection of potential malware infections.
Remove vCrypt1 Virus and Restore .vCrypt1 Files
The vCrypt1 ransomware is an offensive threat that endangers the overall PC performance. For the sake of your PC security and your privacy, the threat should be removed completely. The detailed removal guide below contains detailed steps of vCrypt1 ransomware removal. In step 6 several alternative data recovery approaches may restore important .vCrypt1 files.
Summary of vCrypt1 Ransomware Virus
| Name |
vCrypt1 Ransomware |
| File Extension |
.vCrypt1 |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove vCrypt1 ransomware with the help of an anti-malware tool. |
| Manual Solution |
vCrypt1 ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam emails, malicious URLs, malicious attacments, exploit kits, freeware. |
vCrypt1 Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely vCrypt1 Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



