The Extractor ransomware encrypts target user data and renames it with the .xxx extension and can be easily deleted by following our removal guide.
Extractor Ransomware Description
Malware researchers discovered a new virus threat called the Extractor ransomware. At the moment the initial security analysis does not show any correlation with any of the known virus families. This means that it is probably written by its creator, an unknown hacker or a hacker collective. The analysis only shows that it is written in the Delphi, a programming language that was popular a few decades ago. This gives out an indication that the person or people behind it is/are probably not young.
At the moment the malware features only a basic encryption engine. Like other similar threats it uses a built-in list of target file type extensions which are processed using a strong encryption cipher. At the moment we have not been able to extract the complete list. It is likely that it uses a complete list that affects the most commonly used user data: archives, documents, videos, music, photos and etc.
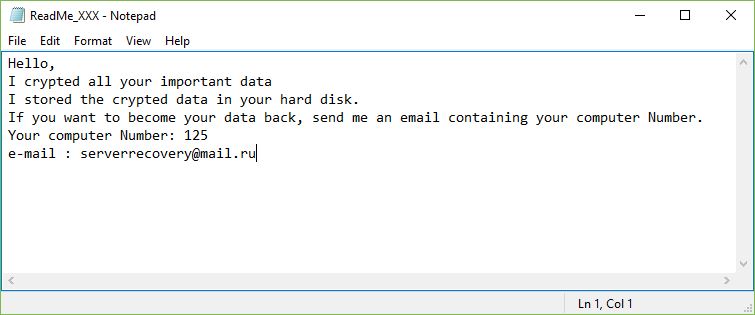
When the process is complete all affected files are renamed using the .xxx extension. The victims are then shown a ransomware note crafted in a ReadMe_XXX.txt file. Its contents read the following:
Hello,
I crypted all your important data
I stored the crypted data in your hard disk.
If you want to become your data back, send me an email containing your computer Number.
Your computer Number: 125
e-mail : [email protected]
At this point the malware is still in an early stage of development. We expect to see future updates that may include one of the following additions:
- Keylogger – Future updates of the virus engine may include various forms of surveillance upon the victims. One of the most popular ways is to include a keylogger that is able to capture the input keystrokes and mouse movement.
- Remote Control – Another surveillance option includes the ability to initiate full remote control of the infected hosts.
- Data Stealing – The remote attackers can steal arbitrary data to their own servers by issuing commands to the virus engine.
- Botnet Recruitment – Infected computers can be recruited to a worldwide botnet that is being isedby the operators or rented out to other criminals.
- Additional Payload Delivery – The virus may be used to deliver other threats to the infected computer.
- Persistence – The engine may create a persistent state of execution which effectively prevents all manual removal attempts.
By looking at the ransomware note we can conclude the following:
- The criminals assign an unique ID to each infected host. It is specified in the ransomware note.
- The Extractor ransomware is disguised as a network or system utility and is distributed as a single binary file.
- The hacker(s) behind the threat use an anonymous email service which hides the identity of the operators.
Extractor Ransomware Distribution
The Extractor ransomware is being distributed as a single binary file – ip topoloji.exe. From its file name we assume that the hackers behind it are distributing the file as a counterfeit system utility. Some of the strategies that can be employed in this case include the following:
- Email Spam Messages – Hackers can distribute the virus via various social engineering campaigns. The operators can disguise the virus as a legitimate app and it may be attached, linked in the body contents.
- Infected Documents – In the last few months infected docuemnts have become a popular tool for spreading all types of malware. The criminals craft documents that feature dangerous scripts. When they are opened a prompt asks them to enable the built-in scripts. If this is done the commands automatically downloads and starts the virus.
- Browser Hijackers – Malicious web browser extensions, also known as hijackers, can deliver the ransomware to the victim machines. Upon installation they modify the settings of the affected applications so that they redirect to a hacker-controlled site. In addition they may deliver the virus themselves.
- Web Scripts and Redirects – Dangerous web site code that is embedded in hacker-controlled domains.
- Direct Hacker Intrusions – Automated or manual vulnerability testing can be issued against potential victims using software frameworks or other means.
Summary of the Extractor Ransomware
| Name |
Extractor Ransomware |
| File Extensions |
.xxx |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove Extractor Ransomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
Extractor Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
Extractor Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Extractor Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Extractor Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore Extractor Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



