Our detailed Searchpage(.)com browser hijacker removal guide shows how victims of the redirect can restore their computers.
Remove Searchpage(.)com Redirect and Restore PC
Manual Removal Guide
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Symptoms and Consequences of Searchpage(.)com Infection
The searchpage.com browser hijacker is a newly reported threat that has started to target computer users worldwide. According to the initial code analysis it follows the usual infection tactics. One of the main uses of malware such as this one is that its usage leads to a lot of security and privacy issues.
The reasons why browser hijackers are popular is because they have the ability to perform several actions at once:
- Privacy Invasion ‒ They are frequently used by criminals to extract sensitive information about the victims.
- Malware Infection ‒ Browser hijackers have the ability to drop various forms of computer viruses and related malware to the compromised machines.
- Settings Modification ‒ Infections with hijackers like this one can lead to a dangerous change in essential settings of the computer. As a result the users can experience performance issues and even applications failure.
One of the usual symptoms of browser hijacker infection start to get noticeable even at the first stages of deployment. Threats like this one are made for the most popular web browsers. Examples include: Mozilla Firefox, Google Chrome, Opera, Internet Explorer, Microsoft Edge, Safari and others. When this is complete the victims will find that important settings have been changed: the default home page, search engine and new tabs page. As a result the users are going to be redirected to the hacker-controlled site – Searchpage(.)com.
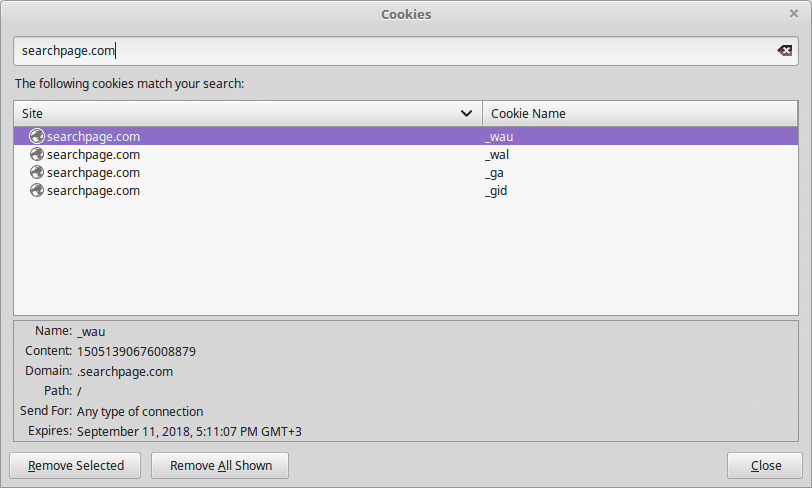
Every time the victims interact with the site in any way the stored cookies start to harvest the private data of the users. Every time the site is accessed several tracking cookies are imposed. The list includes the following entries: wau, wal, ga, gid. They track every interaction and this information is sent to the hacker operators. As a result of this every site visitors is being profiled, it is very likely that this site is a part of a wider network. This possibility makes it possible for the successful identification of the visitors.
The site’s design is made to look like a regular Internet portal. It features a top menu bar that is divided between a left side and a right logo. The left side includes several hyperlinks that lead to security search type settings (Web, Images, Videos and News), while the right side displays a “Results by Yahoo!” image. This is a symbol that showcases the fact that the hackers have used the popular search engine to power the site. This however does not indicate that the visitors are going to receive sponsored results.
In the center of the site there is a search engine that dominates the page. The reason why the site is designed in a such a way is to persuade the users into using it. On the bottom navigation bar there are several links to display the Privacy Policy, the Contact page and other similar links.
According to the available information the site is operated from Hong Kong, the following address is given:
SearchPage(.)com Headquarters
Room 1708, Kai Tak Commercial Building, 317-319 Des Voeux road, Central, Hong Kong
The privacy policy and the terms of use showcase that the site is part of the SearchPage network which is operated by a Canadian-based company. It is very likely that the data is shares between all service operated by the network. The privacy policy states that the site collects private information from visitors. This includes the following cases:
- Direct Information Harvesting ‒ Using the browser hijacker and the site directly downloads information about the site interaction. The list includes the following data: cookies, date and time of visit, Internet browser, hardware device and all visited sites.
- Hardware Information ‒ The site is able to harvest specific information about the site visitors that include the network card Mac Address, Drive serial number and default browser. This is used to create the unique user identifier. The Searchpage(.)com browser hijacker can use this information to showcase information about any system problems.
- Browser Configuration ‒ As the Searchpage(.)com browser hijacker is able to infiltrate the running browsers the operators obtain information on the installed plugins and their configuration.
The Searchpage(.)com is able to target the users via the harvested information. The data is used to send information about the service’s other sites and networks and generate the traffic to them. Its important to note that the collected information is also used for analytical purposes (web analytics for example) and can be shared with partners and affiliate companies. The privacy policy reads that the tracking companies are used for the following purposes:
- Delivering targeted content at the victims.
- Recording the preferences of the various services.
- The recorded data from the cookies showcase how the users interact with the services in general.
- Researching into how the website, browser hijacker and related services can be improved.
- Identifying all site interactions.
- The cookies are used to power certain functionalities of the services.
As a result of this the Searchpage(.)com browser hijacker should be avoided at all cost. The software and the site pose a serious threat to the security and privacy of the victims.
Where Did My PC Get Infected With The Searchpage(.)com Browser Hijacker?
The Searchpage(.)com browser hijacker can be acquired by falling victim to different infection methods. The current hacker attacks are run through different channels.
A popular way of infecting users is by distributing the malicious code in infected software installers. They are usually found on hacker-controlled sites or P2P networks like BitTorrent. In the most popular case the criminals download legitimate versions of free or trial programs that are then modified to include malicious code. These so-called “bundle installers” are placed on sites that pose as official sources or popular web portals. To further manipulate the victims into downloading copies the hackers utilize the same images and text in some of the attempts.
Email messages can also be used as a medium to serve hyperlinks to such software installers. The hackers use template messages and social engineering tricks to try and manipulate the targets into infecting themselves. Depending on the case several different schemes may be used:
- Attachments ‒ Direct file attachments to malware code or infected software installers can be bundled directly into the the emails to the recipients.
- Hyperlinks in the Body ‒ Another tactic is to insert the links in the body contents of the sent emails.
- Combination ‒ The hackers can use a combination of the above two methods to raise the infection ratio.
Another way of distributing the Searchpage(.)com browser hijacker is by spreading infected documents. They can be both placed on download sites, ads and sent via email messages in a similar way to software installers. The files can be of different types including: rich text documents, spreadsheets or databases. When they are opened a prompt notification appears which asks the users to run the built-in scripts. If this is done the Searchpage(.)com browser hijacker code is downloaded from a remote site and executed on the local computer.
Remove Searchpage(.)com Redirect and Restore PC
WARNING! Manual removal of the Searchpage.com browser hijacker requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Searchpage(.)com – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Remove Searchpage.com from Windows
Here’s a way to remove the program. This method will work regardless if you’re on Windows 10, 8, 7, Vista or XP. Simply selecting the program and pressing delete won’t work, as it’ll leave a lot of small files. That’s bad because these leftovers can linger on and cause all sorts of problems. The best way to delete a program is to uninstall it. Here’s how you can do that:
1. Hold the “Windows” button (It’s between CTRL and Alt on most keyboards) and press “R”. You’ll see a pop-up window.

2. In the textbox, type “appwiz.cpl”, then press“ Enter ”.

3. The “Programs and features” menu should now appear. It’s a list of all the programs installed on the PC. Here you can find the program, select it, and press “Uninstall“.

Remove Searchpage.com Virus From Your Browser
Before resetting your browser’s settings, you should know that this action will wipe out all your recorded usernames, passwords, and other types of data. Make sure to save them in some way.
-
1. Start Mozilla Firefox. In the upper right corner, click on the Open menu icon and select “Add-ons“.

2. Inside the Add-ons Manager select “Extensions“. Search the list of extensions for suspicious entries. If you find any, select them and click “Remove“.

3. Click again on the Open menu icon, then click “Options“.

4. In the Options window, under “General” tab, click “Restore to Default“.

5. Select “Search” in the left menu, mark the unknown search engine and press “Remove”.

-
1. Start Google Chrome. On the upper-right corner, there a “Customize and Control” menu icon. Click on it, then click on “Settings“.

2. Click “Extensions” in the left menu. Then click on the trash bin icon to remove the suspicious extension.

3. Again in the left menu, under Chrome, Click on “Settings“. Go under “On Startup” and set a new page.

4. Afterward, scroll down to “Search“, click on “Manage search engines“.

5. In the default search settings list, find the unknown search engine and click on “X“. Then select your search engine of choice and click “Make default“. When you are ready click “Done” button in the right bottom corner.

2. In the “Manage add-ons” window, bellow “Add-on Types“, select “Toolbars and Extensions“. If you see a suspicious toolbar, select it and click “Remove“.

3. Then again in the “Manage Add-ons” window, in “Add-on Types“, Select “Search Providers“. Chose a search engine and click “Set as default“. Select the unknown search engine and click “Remove and Close”.

4. Open the Tools menu, select “Internet Options”.

5. In the “General” tab, in “Home page”, enter your preferred page. Click “Apply” and “OK”.

Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help



