The EnCrypt Ransomware is computer virus that encrypts files and marks them with the .en extension, read our removal guide to recover your PC.
Manual Removal Guide
Recover EnCrypt Ransomware Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How Does EnCrypt Ransomware Infiltrate the System?
EnCrypt Ransomware can be distributed using a variety of ways. The first reports of the malware were reported in the first week of July 2017. It targets primarily English-speaking users and is spread across the world.
Email spam messages can deliver the malware by utilizing social engineering tricks. Their goal is to confuse the targets into infecting themselves by falling for the scams. The EnCrypt ransomware is inserted as a file attachment or linked in the body content of messages that appear to be sent by government institutions or well-known companies.
Other ways of spreading the malicious binaries is by inserting the EnCrypt virus code in payloads. They can be either software installers or documents.
Infected documents are usually popular formats (rich text documents, spreadsheets or databases) that feature scripts (macros). When the victims open them a prompt notification asks them to enable them. If this is done the Encrypt ransomware is downloaded from a remote server and executed on the local machine.
Software installers that feature the malicious code are usually distributed on hacker-controlled download sites or P2P networks like BitTorrent where pirate content is usually found.
Browser hijackers are another possible source. They are malicious browser add-ons that seek to modify important settings such as the default home page, new tabs page and search engine to a hacker-provided address. They are usually made for the most popular browsers: Mozilla Firefox, Google Chrome, Opera, Safari, Internet Explorer and Microsoft Edge.
Direct hacker intrusion attempts are another possible source of EnCrypt ransomware infections. This is done by picking a software vulnerability and launching an automated tool that attempts to exploit them. This is the reason why we recommend that all computer users update all applications to their latest versions.
Related: Karo Virus , Hell Radiation Ransomware Virus
Infection Flow of EnCrypt Ransomware
EnCrypt Ransomware is a newly discovered malware of unknown origin. The initial analysis of the collected samples indicates that it is based on an unknown source. The experts have not discovered any code that is taken from the popular malware families. This means that the virus is probably made by its creators and not sourced from the underground hacker markets.
Upon infection it follows the usual behavior patterns associated with most other ransomware. The Encrypt virus does not differ from them by immediately starting its encryption engine after the infection has been made. Like other ransomware it seeks to process files using a strong cipher based on a built-in list of target file type extensions. They include data such as images, videos, photos, documents, backups, databases and more.
When this process is complete the ransomware extension .en is used to mark all affected files. A note is crafted in a “READ_THIS_FILE.txt” file that reads the following message:
YOUR DOCUMENTS, PHOTOS, DATABASES AND OTHER IMPORTANT FILES HAVE BEEN ENCRYPTED!
—
The only way to decrypt your files is to receive the private key and decryption program.
To decrypt your files you need to buy the private key
—
HOW TO GET THE PRIVATE KEY?
1. Create a Bitcoin Wallet (blockchain.info)
2. Buy necessary amount of Bitcoins (50$)
Do not forget about the transaction commission in the Bitcoin network
Here are our recommendations:
Korbit.co.kr – Bitcoin, Ethereum & Ripple Trading In Korea
btcdirect.eu – A good service for Europe
bittylicious.com – Get BTC via Visa / MC or SEPA (EU) bank transfer
localbitcoins.com – This service allows you to search for people that want to sell Bitcoins directly (WU, Cash, SEPA, Paypal, etc).
cex.io – Buy Bitcoins using Visa / Mastercard or Wire Transfer.
coincafe.com – It is recommended for the fast and easy service. Payment methods: Western Union, Bank of America, cash through FedEx, Moneygram, and/or wire transfer
bitstamp.net – Old and proven Bitcoin dealer
coinmama.com – Visa/Mastercard
btc-e.com – Bitcoins dealer (Visa/Mastercard, etc.)
Could not find Bitcoins in your region? Try searching here:
buybitcoinworldwide.com International catalog of Bitcoins exchanges
bitcoin-net.com – Another Bitcoins sellers catalog
howtobuybitcoins.info – International catalog of Bitcoins exchanges
bittybot.co/eu – A catalog for the European Union
3. Send 50$ to the following Bitcoin address:
1H9jjVku8RPzQ4gDsA4oBQLNw9tEYHaC5X
4. Go to the following site:
http://yfkhfomk3iqod5vb.onion
5. In there site insert:
ID ([redacted])
Your btc address (the same utilized for the payment)
Your email address (to receive the key and the program for decrypt)
6. Wait 24/48h and check your email (also the spam)
—
HOW TO ACCESS TO THE WEBSITE?
1. Download “Tor Browser” from https://www.torproject.org/ and install it.
2. In the “Tor Browser” open:
http://yfkhfomk3iqod5vb.onion
Note! This page is available via “Tor Browser” only.
—
Also you can use temporary addresses without using “Tor Browser”.
—
1. http://yfkhfomk3iqod5vb.tor2web.org
2. http://yfkhfomk3iqod5vb.onion.link
3. http://yfkhfomk3iqod5vb.onion.nu
4. http://yfkhfomk3iqod5vb.onion.cab
5. http://yfkhfomk3iqod5vb.onion.to
—
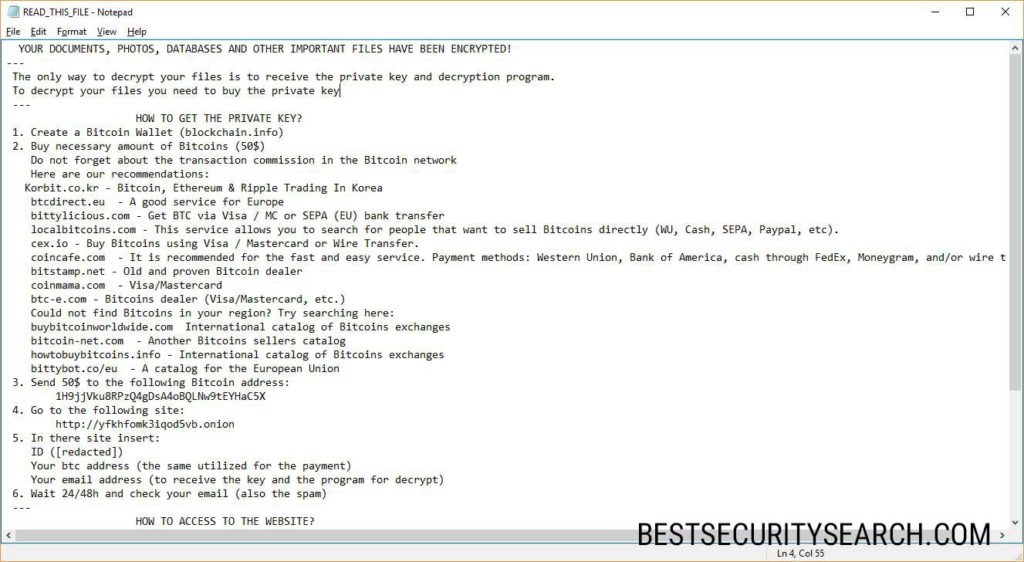
The hacker operators of the EnCrypt Ransomware include a thorough explanation that pressures the victims into paying the amount of 50 US Dollars in the Bitcoin digital currency. For those users who are unaware about this payment method a short explanation is provided along with the addresses of some of the most famous exchanges.
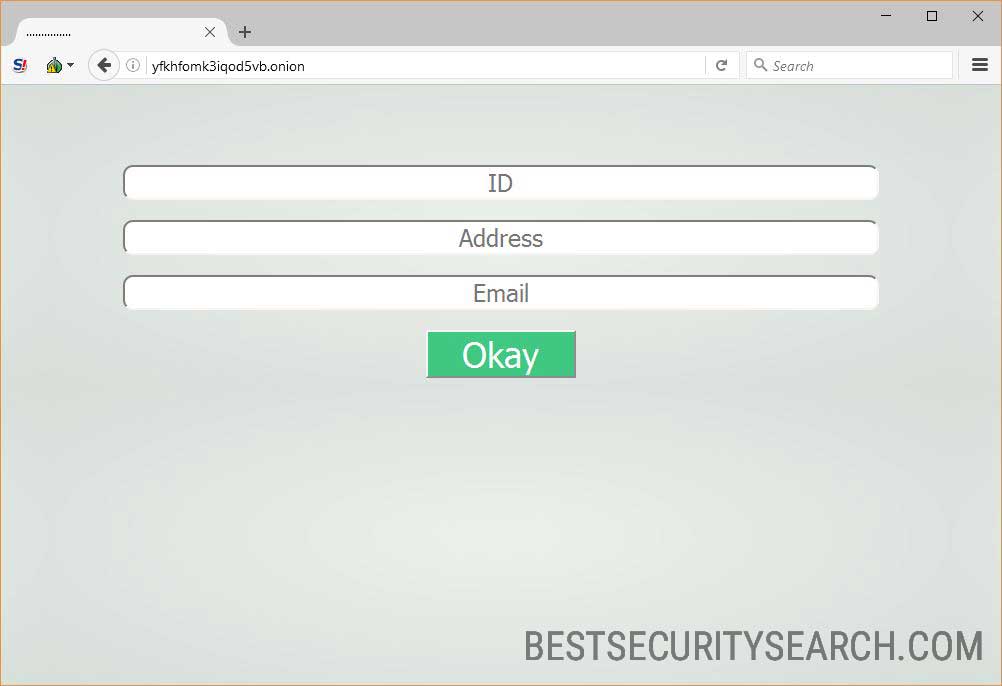
The Encrypt Ransomware note also shows several payment gateways located on the TOR hidden network. When the users enter the address in the browser they are asked to enter the following data: ID, Address and Email.
This means that during the initial infection phase the Encrypt virus engine has generated an unique victim ID for each infected host. This is usually done by harvesting system information that is processed using a provided algorithm. The type of extracted data can include both system information and user files.
As this is merely the initial version of the malware we expect to see future updates of the EnCrypt Ransomware can include the following modules:
- Trojan Component – Updated versions of the EnCrypt ransomware can include a feature-rich virus core that can add a Trojan component. It allows the hackers to remote control the infected machines and spy on the users in real time.
- Dangerous System Modification – The Encrypt virus engine may make changes to the Windows operating system that can render it partially working or disable certain functions.
- Lockscreen Addition – The inclusion of a lockscreen can make interaction with the infected computers impossible if the virus is not removed completely.
- Data & Identity Theft – The extracted files and stolen data can be used for other crimes such as identity theft.
- Additional Malware Delivery – Advanced ransomware variants of the EnCrypt virus may lead to infections with other threats.
Remove EnCrypt Ransomware and Restore Data
WARNING! Manual removal of EnCrypt Ransomware requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
EnCrypt Ransomware – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
EnCrypt Ransomware Files
WARNING! All files and objects associated with EnCrypt Ransomware should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD EnCrypt Ransomware Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



