Our removal guide gives details on recovering from the DCry Virus that encrypts user files with a strong cipher and renames them with the .dcry extension.
Manual Removal Guide
Recover Dcry Virus Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How Does Dcry Virus Infiltrate the System?
DCry virus infections can be acquired through several channels of distribution. As the number of reported infections is rather low at the moment the security experts cannot judge what is the primary method. We suspect that the criminals use the most popular strategies to increase the infection ratio.
One of them relies in the coordination of email spam messages. They use templates that feature stolen images and graphics from famous companies and government institutions. Usually the DCry virus is attached directly or linked in the body contents.
Another option is to use infected payloads that use scripts to deliver the infection. Usually they are in the form of software installers or documents.
The installers are usually modified legitimate binaries that are changed to include the DCry virus code. Depending on the case the code may be started when the victims double click on the file or after the installation itself.
The criminals can also include the scripts in different types of documents – spreadsheets, rich text documents, databases and etc. The malicious actions are executed once the users allow the macros.
Usually malicious instances are hosted on download servers and sites that may pose as legitimate sources. Redirects and ad networks can also confuse Internet users into getting infected.
Browser hijackers can also lead to a successful infection during their initial infection phase. Their aim is to modify the behavior of the most popular web browsers (Mozilla Firefox, Google Chrome, Microsoft Edge, Safari, Internet Explorer and Opera). During the initial infection important settings are changed such as the default home, search engine and new tabs. They lead the victims to a hacker-provided address that can seriously affect the privacy and security of the users. In addition the malware can be directly downloaded by the add-ons or inserted via the page scripts.
According to several research reports computer hackers can also utilize direct software vulnerability attacks. They primarily focus on the RDP protocol that is widely used to connect to computers remotely.
Related: ALL YOUR FILES HAVE BEEN LOCKED Fenrir Virus, AdWind Virus
Infection Flow of Dcry Virus
The DCry virus is a ransomware that has recently been identified by malware researchers. It does not feature any code from any of the famous malware families and we suspect that it is an original application. The identity of the hacker or criminal collective behind it is not known at the moment.
The security analysis reveals that the Dcry ransomware engine performs several checks before the malicious actions are executed. This includes a thorough scan for the presence of anti-virus products. If any are found then the sample automatically disables itself. Depending on the iteration it may also delete itself to remove any possibilities of detection.
Before engaging in any ransomware actions the DCry virus is able to harvest a lot of sensitive system information:
- Machine Time Query – This is used to attain information related to the time of infection. This is an important input value used in some of the algorithms related to the hash calculations.
- Machine Timezone – Provides additional information about the time of infection and the location of the machine.
- System Locale – The data shows the user regional settings. This information is used by the ransomware engine to determine the language and geographical location of the victims. If the DCry virus contains several ransomware notes then the most appropriate one is chosen and displayed.
- Volume Size – By querying all connected partitions the Dcry virus can impact as many devices as possible – hard drives, network shares, removable device and more.
Once this is done the DCry ransomware engine is immediately started. It contacts the malicious web servers and informs the hackers of the infection in an automated way. The addresses are built-in in the samples themselves.
The hackers have included the option of spawning processes and commands if the criminals send out such a task. This leads to the possibility of the following case scenarios – stealing sensitive user and system data (before the encryption phase), downloading additional malware and spying on the users.
The DCry virus is able to connect to LPC ports and communicate with external hardware and modify system-specific files in the Windows directory.
After this is done the Dcry ransomware engine is automatically started. Like other similar threats it starts to process files based on a built-in list of file type extensions. In most cases the idea is to target as many popular file formats as possible: music, videos, photos, documents, backups, archives, configuration files, databases and etc.
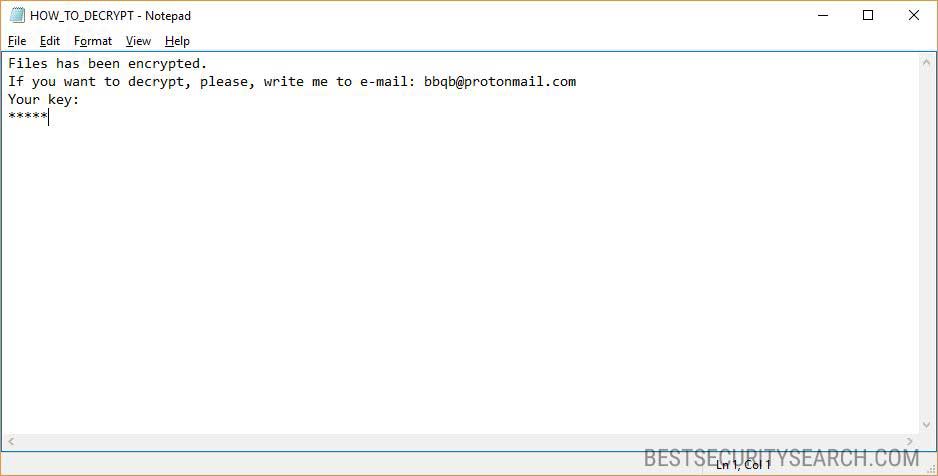
Once the prcess is complete the DCry ransomware note is crafted in a “HOT_TO_DECRYPT.txt” file that reads the following message:
Files has been encrypted.
If you want to decrypt, please, write me to e-mail: [email protected]
Your key:
*****
In addition a notification prompt created in an application frame is created. It displays another similar message:
Your files is crypted.
If you want to encypt, please, write me to e-mail: [email protected]
Your key: *****
The .dcry extension is automatically added to all processed files. The message does not explain much to the victims. Instead of the template notes that feature in-depth explanations about the infection. Instead the hackers have opted for the blackmail by email method – the victims are persuaded to email the criminals via the provided address. It is hosted on an anonymous and secure hosting solution that is privacy-centric. The victims only need to specify their hacker-generated unique victim ID quoted in the note.
Based on the quality and quantity of the affected files the criminals can adjust the ransomware fee. It is usually paid out using the Bitcoin digital currency where the transactions cannot be traced down to an individual.
All victims of the DCry virus should use a quality anti-spyware solution to remove the active infections. Do not pay the hackers as they will withdraw the money and leave the infections on. Once the Dcry ransomware virus has been removed a data recovery software can restore the affected data. Read our in-depth instructions below.
Remove Dcry Virus and Restore Data
WARNING! Manual removal of Dcry Virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Dcry Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Dcry Virus Files
WARNING! All files and objects associated with Dcry Virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD Dcry Virus Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



