An infection with the dangerous Bad Rabbit Virus leads to serious security issues. Victims can restore and protect their computers by following our complete removal guide.
Remove Bad Rabbit Virus and Restore PC
Manual Removal Guide
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Distribution of Bad Rabbit Virus
The initial attack wave carrying the Bad Rabbit virus was performed on October 24th this month. The main method associated with it an infected payload agent. This particular case used a fake Adobe Flash installer which was uploaded to fake download sites.
There are several options that can be used by the hacker operators, they all represent the most widely used tactics:
- Infected Documents ‒ The Bad Rabbit ransomware code can be embedded in some of the most widely used document types which can be customized to appear as interesting or important to the victims. Examples include rich text documents, spreadsheets, presentations and databases.
- Fake Software Installers ‒ This is the way the Bad Rabbit virus is being distributed to the victims. The hacker operators download legitimate software from their official sources and modify them to include the malware virus. In other cases the resulting files may not contain any legitimate data at all.
- Scripts ‒ They can be placed on web sites, small files or even interactive elements in email messages. Once clicked they execute a built-in sequence of commands which download the Bad Rabbit virus from a remote location and install it on the victim computers.
The observed campaign used a number of automatically generated sites which contain links or scripts leading to the infection. All of the sites were news or media portals hosted from different servers around the world. The files associated with the current wave are identified as install_flash_update.exe. The security researchers have also observed that JavaScript instances are being used on the automatically generated sites to deliver the infections. Another option which the hackers tend to use is the reconfiguration of other virus files to distribute the Bad Rabbit by themselves. Other strategies can also be implemented as the virus grows and spreads further. To this date we have confirmed infections from the folloing countries:
- Ukraine
- Turkey
- Germany
- Russia
- Bulgaria
- Japan
The Bad Rabbit virus targets primarily corporate clients and government agencies. One of the most prominent victims is the Odessa airport.
Some of the main distribution sites that host instances of the Bad Rabbit virus:
- myk104(dot)com (US Radio Station)
- montenegro-todaycom (Tourist Office of Montenegro)
- otbrana(dot)com (Bulgarian Defense Association)
- hercegnovi(dot)me (Hercegnovi Municipality website, Montenegro)
- Bahmut(dot)com(dot)ua (Bahmut Municipality website, Ukraine
- Ucarsoft(dot)com (Turkish web services)
- Pensionhotel(dot)de (German Booking Website)
- Tweetlerim(dot)gen(dot)tr (Turkish Twitter Trends site)
During the investigation security researchers note that a subset of the captured samples have used the Eternal Blue exploit which is the same one used by the Petya ransomware.
Impact of Bad Rabbit Virus
Once the victim files are used to attack the compromised files a series of complicated commands are executed. One of the most important steps in the infection sequence is the elevation of privileges, this ensures that the virus obtains administrative rights giving it unlimited access to the system. The attempt is made by issuing the standard UAC prompt. If it passes a malicious DLL is saved as C:\Windows\infpub.dat and launched using the system rundll32 file.
Another dangerous component of the Bad Rabbit virus is capable of brute-forcing the NTLM login credentials of Windows machines which have pseudo-random IP addresses. This file is also capable of installing a dangerous malicious executable into the Windows system folder and create a scheduled task. This is an option for setting up a persistent installation. The security analysis also detected that the modules and components that make up the Bad Rabbit virus showcase stealth detection features. They are placed to protect the virus from being detected. Several registry entries are added to the Windows registry which are used by the modules during the later stages of infection.
All of this leads to the execution of infpub.dat, a module of the Bad Rabbit virus which launches the encryption process. Like other similar strains it uses a built-in file list of target file extensions. The captured strains so far indicate the following:
.3ds .7z .accdb .ai .asm .asp .aspx .avhd .back .bak .bmp .brw .c .cab
.cc .cer .cfg .conf .cpp .crt .cs .ctl .cxx .dbf .der .dib .disk .djvu .doc
.docx .dwg .eml .fdb .gz .h .hdd .hpp .hxx .iso .java .jfif .jpe .jpeg .jpg
.js .kdbx .key .mail .mdb .msg .nrg .odc .odf .odg .odi .odm .odp .ods .odt .ora
.ost .ova .ovf .p12 .p7b .p7c .pdf .pem .pfx .php .pmf .png .ppt .pptx .ps1 .pst
.pvi .py .pyc .pyw .qcow .qcow2 .rar .rb .rtf .scm .sln .sql .tar .tib .tif .tiff
.vb .vbox .vbs .vcb .vdi .vfd .vhd .vhdx .vmc .vmdk .vmsd .vmtm .vmx .vsdx .vsv .work
.xls .xlsx .xml .xvd .zip
Some of the code is believed to have been taken from DiskCryptor from the Mamba ransomware strain. It uses the same disk encryption module which installs a superimposed bootloader and prevents the normal boot-up process. The code analysis reveals that the hacker operators behind the threat have used references that bear a resemblance to Game of Thrones characters, some of the strings are the following: Viserion, Drogon, Rhaegal, GrayWorm and etc.
Once all of this is done the victims will be faced with a ransomware note once the machine is restarted. The following message appears instead of the usual boot-up screen:
Oops! Your files have been encrypted.
If you see this text, your files are no longer accessible.
You might have been looking for a way to recover your files.
Don’t waste your time. No one will be able to recover them without our decryption service.
We guarantee that you can recover all your files safely.All you need to do is submit the payment and get the decryption password.
Visit our web service at caforssztxqzf2nm.onion
Your personal installation key#l:
ZORqoZdoI+vr6*****
If you have already got the password, please enter it below.
Password#1:
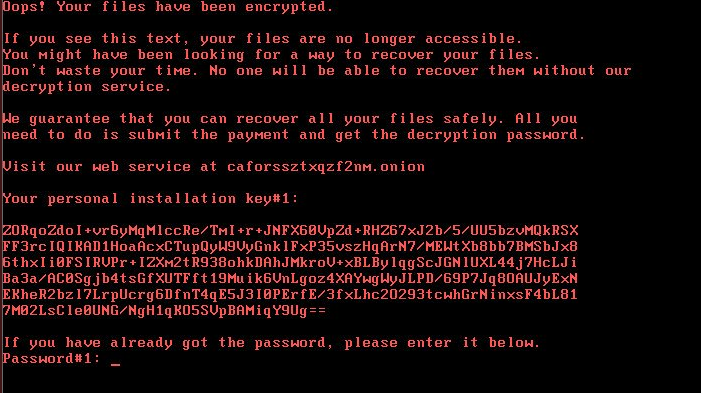
This effectively removes the possibility of starting up the computer normally. The victims are given an unique infection ID (UID) which is usually generated from information harvested from the computers. It may include any of the following: hardware components, installed software versions and user settings.
The victims are redirected to a site located on the anonymous TOR network which displays the blackmail text. It reads the following:
BAD RABBIT
If you access this page your computer has been encrypted. Enter the appeared personal key in the field below. If succeed, you’ll be provided with a bitcoin account to transfer payment. The current price is on the right.
Once we receive your payment you’ll get a password to decrypt your data. To verify your payment and check the given passwords enter your assigned bitcoin address or your personal key.
Time left before the price goes up
36-25-48
Price for decryption:
฿ 0.05
As usual the victims are extorted to pay a ransomware fee of 0.05 Bitcoins which is the equivalent of about $280. We recommend that all users rely on a secure anti-spyware solution which is able to effectively remove detected infections only with a few mouse clicks.
One of the most dangerous actions associated with the Bad Rabbit virus is its ability to try and spread itself on the network that is accessible via the compromised machines. The infection module uses a list of hardcoded usernames and passwords to try and intrude onto other computers and distribute the malware into them. The following usernames were identified as part of the code:
Admin, Administrator, alex, asus, backup, boss, buh, ftp, ftpadmin, ftpuser, Guest, manager, nas, nasadmin, nasuser, netguest, operator, other user, rdp, rdpadmin, rdpuser, root,superuser, support, Test, User, User1, user-1, work
The following credentials are trialed with the above-mentioned list:
111111, 123, 123321, 1234, 12345, 123456, 1234567, 12345678,123456789, 1234567890, 321, 55555, 777, 77777, Admin, Admin123, admin123Test123, Administrator, administrator, Administrator123, administrator123, adminTest, god, Guest, guest, Guest123, guest123, love, password, qwe, qwe123, qwe321, qwer, qwert, qwerty, qwerty123, root, secret, sex, test, test123, uiop, User, user, User132, user123, zxc, zxc123, zxc321,zxcv
A researcher has confirmed that a preventative measure for some of the Bad Rabbit virus strains exists. The following steps are to be taken:
- Once the virus has infected the system the following precautions can be taken to prevent the malware from infecting the machine.
- Create the following file ‒ C:\Windows\infpub.dat
- Create the following file ‒ C:\Windows\cscc.dat
- Remove all inherited permissions from the files which disables interaction with the system.
Note that this method may not work in all cases, for a guaranteed way to delete found instances refer to our intsructions below.
Remove Bad Rabbit Virus and Restore PC
WARNING! Manual removal of the Bad Rabbit Virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Bad Rabbit Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Remove Bad Rabbit from Windows
Here’s a way to remove the program. This method will work regardless if you’re on Windows 10, 8, 7, Vista or XP. Simply selecting the program and pressing delete won’t work, as it’ll leave a lot of small files. That’s bad because these leftovers can linger on and cause all sorts of problems. The best way to delete a program is to uninstall it. Here’s how you can do that:
1. Hold the “Windows” button (It’s between CTRL and Alt on most keyboards) and press “R”. You’ll see a pop-up window.

2. In the textbox, type “appwiz.cpl”, then press“ Enter ”.

3. The “Programs and features” menu should now appear. It’s a list of all the programs installed on the PC. Here you can find the program, select it, and press “Uninstall“.

Remove Bad Rabbit Virus From Your Browser
Before resetting your browser’s settings, you should know that this action will wipe out all your recorded usernames, passwords, and other types of data. Make sure to save them in some way.
-
1. Start Mozilla Firefox. In the upper right corner, click on the Open menu icon and select “Add-ons“.

2. Inside the Add-ons Manager select “Extensions“. Search the list of extensions for suspicious entries. If you find any, select them and click “Remove“.

3. Click again on the Open menu icon, then click “Options“.

4. In the Options window, under “General” tab, click “Restore to Default“.

5. Select “Search” in the left menu, mark the unknown search engine and press “Remove”.

-
1. Start Google Chrome. On the upper-right corner, there a “Customize and Control” menu icon. Click on it, then click on “Settings“.

2. Click “Extensions” in the left menu. Then click on the trash bin icon to remove the suspicious extension.

3. Again in the left menu, under Chrome, Click on “Settings“. Go under “On Startup” and set a new page.

4. Afterward, scroll down to “Search“, click on “Manage search engines“.

5. In the default search settings list, find the unknown search engine and click on “X“. Then select your search engine of choice and click “Make default“. When you are ready click “Done” button in the right bottom corner.

2. In the “Manage add-ons” window, bellow “Add-on Types“, select “Toolbars and Extensions“. If you see a suspicious toolbar, select it and click “Remove“.

3. Then again in the “Manage Add-ons” window, in “Add-on Types“, Select “Search Providers“. Chose a search engine and click “Set as default“. Select the unknown search engine and click “Remove and Close”.

4. Open the Tools menu, select “Internet Options”.

5. In the “General” tab, in “Home page”, enter your preferred page. Click “Apply” and “OK”.

Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help



