Our detailed securesearch.site browser hijacker removal guide shows how victims of the redirect can restore their computers.
Remove securesearch.site Redirect and Restore PC
Manual Removal Guide
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Symptoms and Consequences of securesearch.site Infection
The securesearch.site browser hijacker is a dangerous computer malware that can lead to serious security and privacy implications. The alarming fact is that site interaction alone can cause issues to the victim computer. The primary reason why malware of this type remain one of the most popular ways to target computer users is that they come under the form of a toolbar or a browser plugin.
The hackers behind the securesearch.site browser hijacker usually distribute the code as counterfeit plugins for the most popular web applications: Mozilla Firefox, Internet Explorer, Google Chrome, Opera, Microsoft Edge and Safari. Once downloaded they cause different changes to the computers which include the following actions:
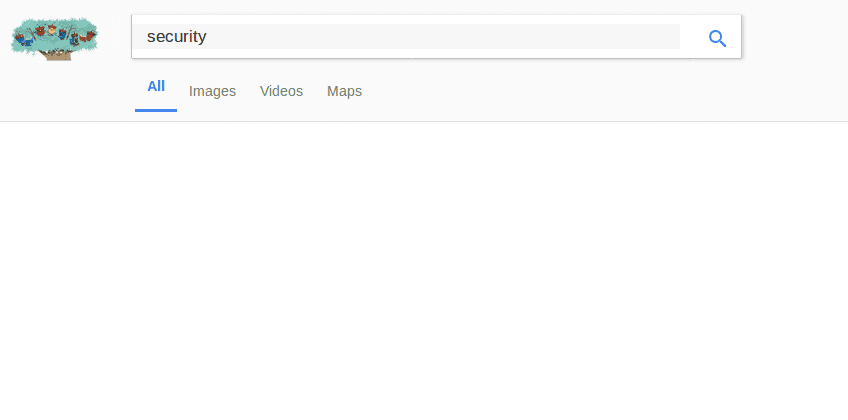
- Settings Modification ‒ In the initial infection stages the securesearch.site changes important settings of the affected web browsers. The list includes the default home page, new tabs page and default search engine. This is done in order to redirect the victims to the hacker-controlled site.
- Information Harvesting ‒ In the majority of cases browser hijackers like this one are used to retrieve sensitive information stored in the web browsers. This means that private data is transferred to the hacker operators, including bookmarks, history, form data, settings, passwords and account credentials.
When the infection is complete the victims will be redirected to the hacker-controlled site. When it it visited and interacted a tracking cookie is imposed which actively tracks their behavior.
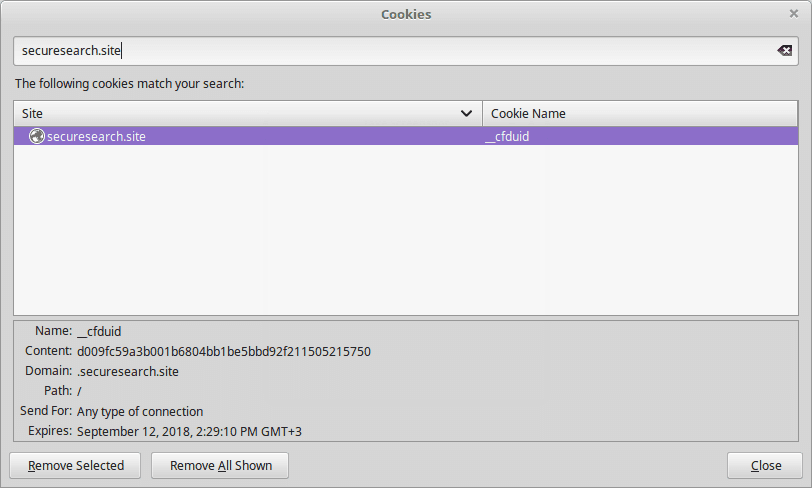
The site itself is designed using a template that resembles typical sites. There is a large search engine box placed in the center of the page, below it are links to various social networks and widely used services placed in a grid layout. On the bottom right side the privacy policy is linked. The posted links are showcased with large thumbail images so that they can be clearly seen by the site visitors. Depending on the hacker configuration the links can include affiliate links that generate income based on purchases made by the site targets. In other cases the securesearch.site hijacker can be used to retrieve the account credentials and passwords used on the services.
We remind our users that any interaction with the site will lead to privacy invasions. The privacy policy shows that the site is being operated by a company called Traffisco LLC. , providing this information from the privacy policy.
According to the document by using the securesearch.site browser hijacker, site scripts and the tracking cookie the operators extract information from the victims. The privacy policy reads that the data is divided into two main categories:
- Personal Information ‒ The site extracts information that can identify the users by harvesting private data. Examples include names, address, email address, telephone numbers and etc.
- Anonymous Information ‒ The anonymous data is used for analytical purposes and include data that is associated with the habits and statistical information. Examples of collected anonymous information are the number of clicks, login times and page views in a single browsing sessions.
Even though the privacy policy lists the two types of data as separate entries they can be combined along with the information provided by other sites, hijackers and affiliate companies to produce a “complete” profile of the victims. Bear in mind that by visiting the site and using the malware hijacker the hackers can obtain private information about the software configuration and the hardware components as well.
The data can be sold or shared with other companies and affiliates both partially or fully.
Where Did My PC Get Infected With The securesearch.site Browser Hijacker?
The securesearch.site browser hijacker can be acquired by computer users using several different ways. The current attack wave uses several different methods which does not give out the primary culprit.
A popular way is to use infected software installers that feature malicious scripts. The usual method is to take the legitimate application executables of free or trial versions apps and then bundle them with the scripts. The resulting files are appropriately uploaded to hacker-controlled sites. In most cases they are made to look like well-known portals or sites. Familiar-looking text, images and even domain names are employed to manipulate as many users as possible. The files can also be uploaded to P2P networks like BitTorrent as well where pirate content is usually found.
The securesearch.site malware code can also be embedded in infected documents. They appear as rich text documents, databases or spreadsheets. When they are a prompt notification asks the computer users to run the built-in scripts. If this is done the browser hijacker is downloaded from a remote server and executed on the local machine there by resulting in an active infection. The infected documents are spread using the same mechanisms as the software installers.
Note that in the last years there has been a significant rise in the number of redirects that bear the malware code. Computer users infected with viruses or have hacked accounts can be used as distributors of the securesearch.site browser hijacker through social media accounts, emails and other means.
As the securesearch.site is part of a larger establishment the hijacker can also be distributed through various pop-ups, ad networks and hyperlinks. Note that interaction with the search engine will not yield the best results. The hackers have customized the algorithm so that sponsored sites and ads are displayed rather than the legitimate results. This is the reason why we discourage users from using the site. Trusting the links may lead to false information and even virus infections.
Remove securesearch.site Redirect and Restore PC
WARNING! Manual removal of the Securesearch.site browser hijacker requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
securesearch.site – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Remove Securesearch.site from Windows
Here’s a way to remove the program. This method will work regardless if you’re on Windows 10, 8, 7, Vista or XP. Simply selecting the program and pressing delete won’t work, as it’ll leave a lot of small files. That’s bad because these leftovers can linger on and cause all sorts of problems. The best way to delete a program is to uninstall it. Here’s how you can do that:
1. Hold the “Windows” button (It’s between CTRL and Alt on most keyboards) and press “R”. You’ll see a pop-up window.

2. In the textbox, type “appwiz.cpl”, then press“ Enter ”.

3. The “Programs and features” menu should now appear. It’s a list of all the programs installed on the PC. Here you can find the program, select it, and press “Uninstall“.

Remove Securesearch.site Virus From Your Browser
Before resetting your browser’s settings, you should know that this action will wipe out all your recorded usernames, passwords, and other types of data. Make sure to save them in some way.
-
1. Start Mozilla Firefox. In the upper right corner, click on the Open menu icon and select “Add-ons“.

2. Inside the Add-ons Manager select “Extensions“. Search the list of extensions for suspicious entries. If you find any, select them and click “Remove“.

3. Click again on the Open menu icon, then click “Options“.

4. In the Options window, under “General” tab, click “Restore to Default“.

5. Select “Search” in the left menu, mark the unknown search engine and press “Remove”.

-
1. Start Google Chrome. On the upper-right corner, there a “Customize and Control” menu icon. Click on it, then click on “Settings“.

2. Click “Extensions” in the left menu. Then click on the trash bin icon to remove the suspicious extension.

3. Again in the left menu, under Chrome, Click on “Settings“. Go under “On Startup” and set a new page.

4. Afterward, scroll down to “Search“, click on “Manage search engines“.

5. In the default search settings list, find the unknown search engine and click on “X“. Then select your search engine of choice and click “Make default“. When you are ready click “Done” button in the right bottom corner.

2. In the “Manage add-ons” window, bellow “Add-on Types“, select “Toolbars and Extensions“. If you see a suspicious toolbar, select it and click “Remove“.

3. Then again in the “Manage Add-ons” window, in “Add-on Types“, Select “Search Providers“. Chose a search engine and click “Set as default“. Select the unknown search engine and click “Remove and Close”.

4. Open the Tools menu, select “Internet Options”.

5. In the “General” tab, in “Home page”, enter your preferred page. Click “Apply” and “OK”.

Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help



