If all your necessary files have the .ransom virus extension and you can’t access them by no program, your computer has been infected with a ransomware infection. The .ransom virus is a type of ransomware that utilizes an encipher algorithm to encrypt target file types and make them out of reach until the unique decryption key is used. Hackers who disseminate the threat aim to extort a ransom from the victims in exchange for the decryption key.
This article aims to inform how to identify all .ransom virus file traits and remove it completely from the computer. Even though at this point there is no freely available decryption tool, the step six of the removal guide provided at the end suggests alternative data recovery approaches that may be efficient for the .ransom files recovery.
Manual Removal Guide
Files Recovery Approaches
Skip all steps and download anti-malware tool that will safely scan and clean all harmful files it detects on your PC.
SpyHunter is a Windows application designed to scan for, identify, remove and block malware, potentially unwanted programs (PUPs) and other objects. By purchasing the full version, you will be able to remove detected malware instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
What Does .Ransom Virus File Cause to the PC?
The infection is triggered by a malicious executable file that is designed to perform various system modifications and ensure stable persistence. One of the main .ransom virus features carries out a deep scan of all PC drives so the threat can locate all target files and enforce its built-in encryption module. Whenever the threat detects a file that is set to its target list, it utilizes a strong encipher algorithm, probably AES to transform the original code completely. Commonly used file types are likely to be set as encryption targets so .ransom virus file may corrupt files that has the following file extensions:
.jpeg, .jpg, .mp3, .mp4, .pdf, .php, .ppt, .pptx, .rar, .rtf, .sql, .tiff, .txt, 7z, .bmp, .doc, .docm, .docx, .html, .xls, .xlsx, .zip
All encrypted files cannot be accessed by any software until the unique decryption key is applied. The key is generated during the encryption process and then transferred to a remote server controlled by the crooks. Each file that has appended the malicious file extension .ransom is encrypted.
Another strain of the malicious file that handles .ransom virus infection is designed to drop a ransom note file that contains a text message from the hackers. The analyses of the .ransom virus samples acknowledge that the ransom note is translated into several languages. All confirmed variants of its name are:
- README_TO_DECRYPT_FILES.txt
- LEAME_PARA_DESCIFRAR_ARCHIVOS.txt
- PROCHTI_MENYA_DLYA_RASSHIFROVKI_FAYLOV.txt
- LEGGIMI_PER_DECIFRARE_I_FILES.txt
- LESEN_SIE_MICH_UM_DATIEIEN_ZU_ENTSCHLUSSELN.txt
- LISEZ_MOI_POUR_DECHIFFRER_LES_FICHIERS.txt
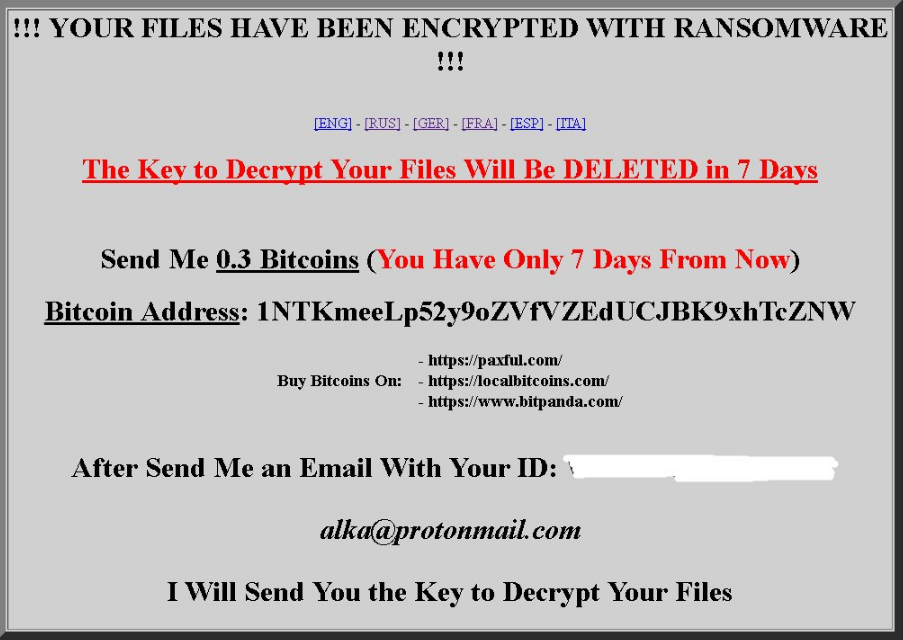
The English version of the ransom message reads the following:
WARNING Encrypted Files
!!! YOUR FILES HAVE BEEN ENCRYPTED WITH RANSOMWARE !!!
[ENG] – [RUS] – [GER] – [FRA] – [ESP] – [ITA] The Key to Decrypt Your Files Will Be DELETED in 7 Days
Send Me 0.3 Bitcoins (You Have Only 7 Days From Now)
Bitcoin Address: 1NTKmeeLp52y9oZVfVZEdUCJBK9xhTcZNW
Buy Bitcoins On:
– https://paxful.com/
– https://localbitcoins.com/
– https://www.bitpanda.com/
After Send Me an Email With Your ID: *******
[email protected]
I Will Send You the Key to Decrypt Your Files
The text makes it clear that the crooks demand a ransom of 0.3 BTC within a seven day period. It is not mentioned what would happen after the deadline, however, we recommend all of you who are victims of the ransomware to avoid any negotiations with cyber criminals as it may expose your privacy and cyber security at a serious risk.
Among the malicious .ransom activities are also likely to be modifications in the Windows Registry. For instance, the ransomware may create new values in the Run or RunOnce registry keys that will allow it to display the ransom message on the screen and auto-execute its malicious payloads whenever the Windows is booted up. The following registry keys may have new malicious values created by .ransom virus:
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\RunOnce
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce
Finally, it is believable that the crypto virus has the functionality to enter a command in the Command Prompt panel and dele all saved shadow volume copies. Thus eliminates one of the possible data recovery approaches. The syntax of the whole command is:
vssadmin.exe delete shadows /all /quiet
How Can the .Ransom Virus Plague the Computer?
The most common way of ransomware distribution is spam email campaigns that distribute the malware. The emails allow hackers to impersonate legitimate sources used by the users and easily convince their targets to interact with the content presented in the email. They may be disseminating the malicious .ransom payloads as email attachments that once opened on the PC automatically start the infection or compromised URLs that download the ransomware unnoticeably when clicked.
These malicious components may also be distributed via popular social networks like Twitter, Facebook, Reddit, WhatsApp, etc.
How to Remove .Ransom Virus File and Restore Data
Victims should remove all malicious files and objects associated with .ransom virus in order to avoid all unpleasant and unwanted effects. For better results, security experts favor the help of anti-malware software.
Remove .Ransom Virus Ransomware Virus and Restore PC
Please note that paying the requested ransom fee to cyber criminals does not really solve your problem with .Ransom Virus crypto virus. In fact, you only encourage hackers to continue spreading ransomware of this kind. Instead, you must remove the threat immediately, and only then look for optional ways to recover your data.
WARNING! Manual removal of .Ransom Virus ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
DOWNLOAD SpyHunter Anti-Malware Tool.Ransom Virus Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps below are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover Encrypted Files
WARNING! All files and objects associated with .Ransom Virus ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
SpyHunter is a Windows application designed to scan for, identify, remove and block malware, potentially unwanted programs (PUPs) and other objects. By purchasing the full version, you will be able to remove detected malware instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



