PSCrypt virus is an Ukrainian ransomware that renames data with the .pscrypt extension, continue reading our removal guide to restore your PC and Files.
Manual Removal Guide
Recover PSCrypt Virus Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How Does PSCrypt Virus Infiltrate the System?
The PSCrypt virus has been found to target commputers in Ukraine, Russia and The Netherlands. Other countries may also be targeted in other campaigns.
The primary methods of infection are not a surprise, the hackers use the most popular strategies for spreading viruses to end users. One of them is the use of email spam messages containing social engineering body text. The aim of the criminals is to confuse them by imitating popular companies. The PSCrypt virus is either attached directly or linked in the body contents.
The criminals behind the ransomware can also opt to create counterfeit download sites or upload PSCrypt ransomware samples to P2P networks like BitTorrent. All kinds of web redirects, ad networks and dangerous scripts can be used to install the binary files which leads to an active infection.
Other attack methods include delivery via browser hijackers or direct hacker attacks.
Related: Erebus 2017 Ransomware, DecrptOr Ransomware
Infection Flow of PSCrypt Virus Virus
A dangerous new ransomware threat has been identified. It is called the PSCrypt virus and according to the researchers and extracted contents it originates from Ukraine. At the moment the identity of its creator is not known, however we suspect that it is a new hacker as he has not revealed his identity. It may be possible that the PSCrypt virus has been made by a criminal collective as well, as it s code does not seem to contain traces from any of the famous malware families.
At the moment the collected samples associated with the PSCrypt ransomware engine show that only a basic encryption module is part of the malware. The virus follows the usual behavior associated with other similar threats by reading a built-in list of target file type extensions. The aim of the hackers is to encrypt as many popular file types as possible: documents, archives, backups, images, music, videos and etc. All of the affected files are renamed with the .pscrypt extension.
After this process is complete a ransomware note is crafted in a “Paxynok.html” file. It reads a message in Ukrainian:
ВАШ ЛИЧНЫЙ ИДЕНТИФИКАТОР
13 69 9B 5F 1E ***
ВАШІ ФАЙЛИ ТИМЧАСОВО НЕДОСТУПНІ.
ВСІ ВАШІ ДАНІ БУЛИ ЗАШІВРОВАННИ!
Для відновлення даних потрібно дешифратор.
Щоб отримати дешифратор, ви повинні:
Оплатити послуги розшифровки:
Оплата відбувається за коштами біткойн (BTC):
Вартість послуги складає 2500 гривень
Оплату можна провести в терміналі IBox.
Інструкція по оплаті:
1. Знайти найближчий термінал Айбокс Айбокс
за допомогою рядка пошуку знайти сервіс «Btcu.biz».
2. Ввести свій номер телефону.
3. Внести суму 2500 грн
4. Роздрукувати і зберегти чек.
5. Зайти на сайт btcu.biz.
6. У розділі «Купити» => «За готівку в терміналі» ввести код з чека (підкреслять червоним), ввести капчу, ознайомитися і погодитися з Умовами використання і натиснути кнопку «Оплатити».
Чек
Переконатися, що код прийнятий і сума збігається з внесеної в термінал.
7. Після того, як код був коректно прийнятий системою, натисніть «Далі» для вибору способу отримання коштів.
Сайт
8. Виберіть розділ «Поповнити ВТС-адреса», введіть адресу – 1AY8WvyqnHwDSqY2rp3LcE6sYTQkCu9oCY і капчу, натисніть кнопку «Відправити».
Сайт2
9. Після оплати:
Надіслати скріншот платежу на [email protected]
У листі вкажіть свій особистий ідентифікатор (подивіться на початок цього документа).
10. Після отримання дешифратора і інструкцій, зможете продожам роботу.
Додаткова інформація:
Програма можемо дешифрувати один файл як доказ того, що у неї є декодер. Для цього необхідно надіслати зашифрований файл на пошту: [email protected]
Увага!
Ні оплати = Немає розшифровки
Ви дійсно отримуєте дешифратор після оплати
Не намагайтеся видалити програму або запустити антивірусні інструменти
Спроби самодешіфрованія файлів приведуть до втрати ваших даних
Декодери інших користувачів не сумісні з вашими даними, оскільки унікальний ключ шифрування кожного користувача.
З повагою.
A machine-translated version in English reads the following message:
YOUR PERSONAL IDENTIFIER
13 69 9B 5F 1E ***
YOUR FILES ARE TEMPORARILY UNAVAILABLE.
ALL YOUR DATA HAS BEEN ENCRYPTED!
To recover data you need decryptor.
To get the decryptor you should:
pay for decrypt:
site for buy bitcoin:
https://localbitcoins.com
https://www.coinbase.com
https://xchange.cc
bitcoin adress for pay:
1AY8WvyqnHwDSqY2rp3LcE6sYTQkCu9oCY
Contact us by email : [email protected]. In the letter include your personal ID (look at the beginning of this document)
After answering your inquiry, our operator will give you further instructions, which will be shown what to do next (the answer you get as soon as possible)
In the letter include your personal ID (look at the beginning of this document).
After you will receive a decryptor and instructions
We can decrypt one file in quality the evidence that we have the decoder.
Attention!
No Payment = No decryption
You really get the decryptor after payment
Do not attempt to remove the program or run the anti-virus tools
Attempts to self-decrypting files will result in the loss of your data
Decoders other users are not compatible with your data, because each user’s unique encryption key.
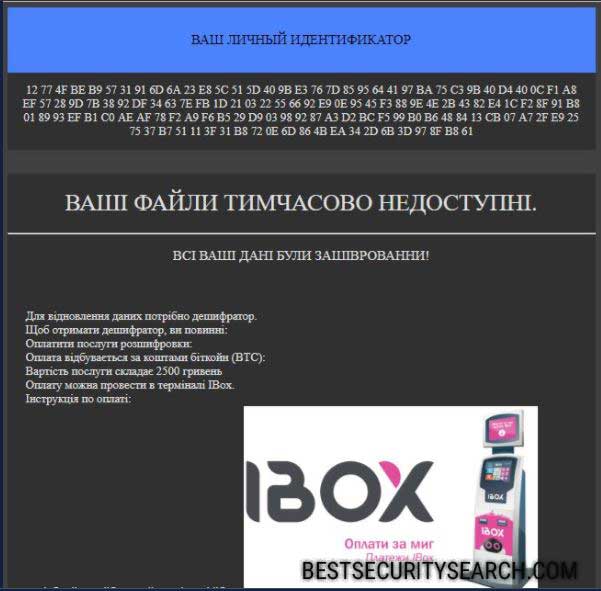
The note reveals details about some of the effects the PSCRypt virus does on the victim computer. It starts with a personal identifier that is assigned to each host. In most cases it is calculated based on gathered system and user data.
Unlike other viruses the hackers have not created a distinct payment gateway for the virus. They have opted to blackmail the users with the standard note that advice them to pay the ransomware sum directly in Bitcoins to the given address. The hackers extort a payment of 2500 Ukrainian hryvnas which is about 100 US Dollars. The money can either be paid via Bitcoins or the iBox system.
However the captured samples also feature the payment option of using iBox, a popular solution used in Ukraine.
During the infection process the researchers uncovered several characteristics about the way PSCrypt virus infects the system:
- The PSCrypt virus is able to maintain a persistent state of execution by writing data to a remote process.
- The ransomware engine is able to harvest information about the hardware components of the systems, installed software and related configuration.
- The virus starts its own process and may spawn additional ones if necessary.
- The ransomware engine can write files to the desktop configuration file. This is frequently used to hide folders or files during encryption.
- Several anti-debugging techniques have been used in the process of programming the PSCrypt virus. This allows the hackers to protect the malicious binary from analysis from sandboxing environments, debuggers or virtual machines.
The PSCrypt virus has also been found to delete all Shadow Volume Copies found on the computer. This means that the compromised files can only be recovered once the ransomware has been removed with a professional-grade data recovery solution.
All computer victims of the PSCrypt ransomware are advised not to pay the hackers and use a quality anti-spyware application to remove the active infection. Follow our removal instructions below.
Remove PSCrypt Virus and Restore Data
WARNING! Manual removal of PSCrypt Virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
PSCrypt Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover PSCrypt Virus Files
WARNING! All files and objects associated with PSCrypt Virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
DOWNLOAD PSCrypt Virus Removal ToolSpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



