A new ransomware is on the rise. Dubbed Philadelphia ransomware, is created by the developer of Stampado ransomware and malicious intenders could buy it for $400 USD. The threat is distributed by the malware creator called The Rainmaker. Philadelphia crypto virus encrypts victim’s files probably using strong AES encryption and then demands ransom payment for delivering the key for decryption.
Closer Look at Philadelphia Ransomware
The predecessor of Philadelphia ransomware – Stampado ransomware had been spotted in July this year. Its samples were decrypted by the security specialist Fabian Wosar from Emsisoft. He has released a decryptor almost immediately after the release of threat. Both threats are written in AutoIT scripting language. This language is freeware, and Philadelphia’s components can be decomposed and analyzed for the weaknesses. Probably this troublesome crypto virus will have a free decryptor released soon.
Once Philadelphia is running on the infected PC, it leaves three files in the User’s profile folder. Two of the files are randomly named, and the third is an executable named Isass.exe.
Another interesting modification that the ransomware does is in the Windows Registry. This adjustment allows running the executable through the update service. It modifies the following key:
→ HKCU\Software\Microsoft\Windows\CurrentVersion\Run\Windows Update
Philadelphia ransomware probably uses the AES encryption algorithm as Stampado does. However, it may also use it in combination with other ciphers or completely different one.
The reported file type extensions encrypted by Philadelphia ransomware are:
At the end of the encryption process the extension .locked is appended in the end. Afterward, the ransomware drops a ransom note that informs the victim of what has just happened and how to proceed further in order to decrypt .locked files. The ransom note states:
“All your files have been encrypted!
All your documents (databases, texts, images, videos, musics, etc.) were encrypted. The encryption was done using a secret key that is now on our servers. To ecrypt your files, you will need to buy the secret key from us. We are the only on the world who can provide this for you.
What can I do?
Pay the ransom, in bitcoins, in the amount and wallet below. You can use LocalBitcoins.com to buy bitcoins.”
Cyber crooks who own Philadelphia ransomware can also take advantage of using the so-called “Russian roulette” mechanism. If the ransom required in BitCoins is not paid this mechanism deletes random files stored on the computer. Another interesting feature of the Philadelphia’s interface is the “Give Mercy” button that allows the cyber criminals to decrypt files for free.

Threat of Philadelphia Contagion
A user’s post in Bleeping Computer’s forums reveals the whole exchanged information between him and the creator of Stampado and Philadelphia ransomware. The conversation makes it clear that The Rainmaker have the intent to infect 20k users during the first release of the threat. We could expect that the distribution will be accomplished by the use of strong exploit kits like Angler and Neutrino. It is most likely the Philadelphia ransomware to be spread via phishing emails that contain malicious links or a javascript that will automatically download and execute the malicious payload of Philadelphia. Researchers at Bleeping Computer reported one spam campaign that distributes a fake payment notice from Brazil’s Ministry of Finance:
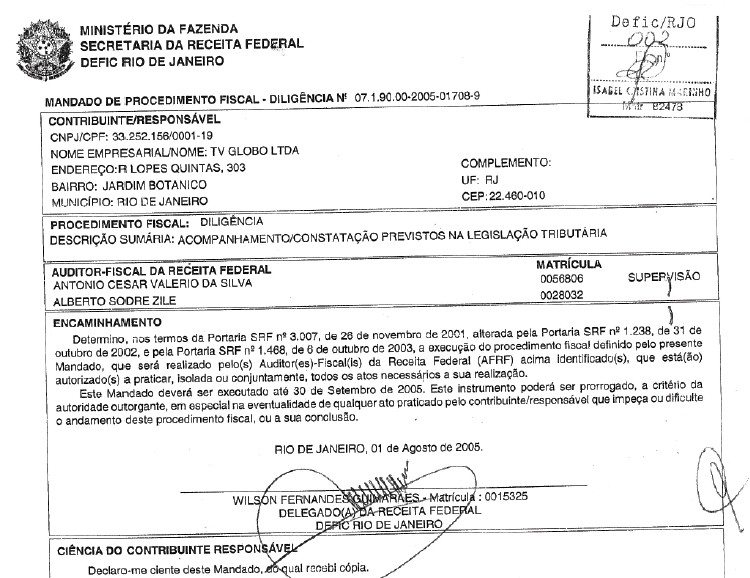
Source: Bleeping Computer
It is also possible to become a victim of Philadelphia contagion on social media sites and file sharing services.
Do’s and Don’ts in Case of Infection
Anyone who wants to be a cybercriminal has the opportunity to buy and own Philadelphia ransomware. So anyone who possesses the threat code can make some custom developments. Therefore the accurate operation of the ransomware could be disrupted. In a case of infection with Philadelphia ransomware, victims should not be tempted to pay the ransom. There is no guarantee that after the payment a decryption key will be sent. Even if the crooks sent the private key, there is a strong likelihood that it will not be working.
As Philadelphia is a serious threat to the regular PC performance and usability of the stored data as well, it should be instantly removed from the computer. For this purpose, we advise you to follow our step-by-step manual removal guide and get rid of this plague. Once Philadelphia is completely removed, we recommend victims to store the encrypted data in case a free decryptor is available soon.
Released on 7 September, Philadelphia ransomware has been decrypted on 10 September by Fabian Wosar, security specialist from Emsisoft.
“Turns out Philadelphia is not so innovative after all.” he tweeted.
Victims of Philadelphia ransomware could download the free decryptor provided by Emsisoft and decrypt .locked files. Keep in mind the “Russian roulette” mechanism of Philadelphia ransomware. If the decryption process is delayed, a lot of the files will be deleted.
Stay Safe
- Update all your software to patch existing vulnerabilities;
- Don’t visit suspicious websites;
- Don’t open doubtful emails;
- Use only updated AV, anti-malware programs;
- Be on the watch and check all suspicious files in VirusTotal before execution.



