An infection with the dangerous Korean Locker Virus leads to serious security issues. Victims can restore and protect their computers by following our complete removal guide.
Remove Korean Locker Virus and Restore PC
Manual Removal Guide
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Distribution of Korean Locker Virus
The Korean Locker Virus is a new virus which has been sighted in attack campaign. At the moment the security researchers cannot determine the primary infection strategy. We presume that the most widely used tactics are going to be employed.
Among them are the email messages created in an automated way and sent to large lists of potential victims. The Korean Locker Virus can be directly attached to the messages. This is one of the easiest way for the criminals to attempt the infection. However a lot of email hosting providers usually capture the signatures of the virus and as such discard such messages or label them as dangerous or spam. Other infection methods related to this one is the option of inserting hyperlinks in the body content of the messages. The links are usually labelled as leading to a familiar website or a file of user interest. Redirects can redirect to hacker-controlled sites, infected payloads or other instances that can lead to an Korean Locker Virus infection.
The computer criminals behind the malware can create malicious sites or download portals which distribute malware of different kinds, including the Korean Locker Virus. A popular option is the use of infected documents which may be of different types ‒ spreadsheets, rich text documents, presentations and databases. They are modified to initiate the virus once the built-in scripts are run. Usually when the files are opened a notification will ask the users to run the macros (scripts). If this is done the infection follows.
The hacker-controlled sites are specialist portals that have been created either manually or automatically by the criminals behind the Korean Locker Virus. They can either directly distribute the threat by initiating various scripts or automated operations or link to such instances. Redirects are usually caused by email interaction, ad networks or other browsing activity. However one of the main sources is the availability of browser hijackers. They are malicious addons made for the most popular web browsers ‒ Mozilla Firefox, Google Chrome, Internet Explorer, Opera, Microsoft Edge and Safari. Once installed they not only infect the users with the malware, but also redirect the victims to a hacker-controlled site. Depending on the configuration the browser hijackers can also steal sensitive information such as any stored passwords, account credentials, history, bookmarks, form data and settings.
Impact of Korean Locker Virus
The Korean Locker virus is a newly discovered ransomware that encrypts target computers with the .locked extension as well as institutes a lockscreen instance. At the moment no information is available about the hacker or criminal collective behind it. However it is suspected that it may be someone from a Korean background.
An initial code analysis reveals that it does follow a complex behavior pattern that is similar to other threats. The code analysis shows that the Korean Locker virus automatically starts to gather sensitive data about the computer and host once the victim hosts have been infiltrated. This is done by extracting information related to the hardware components and user configuration. The programmer behind the Korean Locker virus includes the ability to protect itself from discovery and analysis by the means of guarded memory regions. This is effective against virtual machines, sandboxes and debugging environments. Another trick that is employed by the virus is the delayed start. This is an intentional act as such infections can fool the virus scanners and anti-spyware software that use ordinary heuristic scans.
Dangerous system changes are made so that the virus can access all removable storage devices connected to the machine, as well as available network shares. Its malware engine also has the ability to extract the regional and language preferences. This is used in the case where several versions of the ransomware note exist. The Korean Locker was also found to feature file manipulation capabilities which includes the ability to delete sensitive user data and system files.
Malware system modifications that are part of the code also include the following:
- Windows Registry Changes — The virus engine can alter values stored in the Windows registry which can cause certain applications to stop work. Users can also face severe performance issues.
- Hardware Interaction — The Korean Locker virus can propagate across other connected devices and possibly corrupt their memory.
- Additional Malware Delivery — The computer hackers can use it to instute other threats to the victim host.
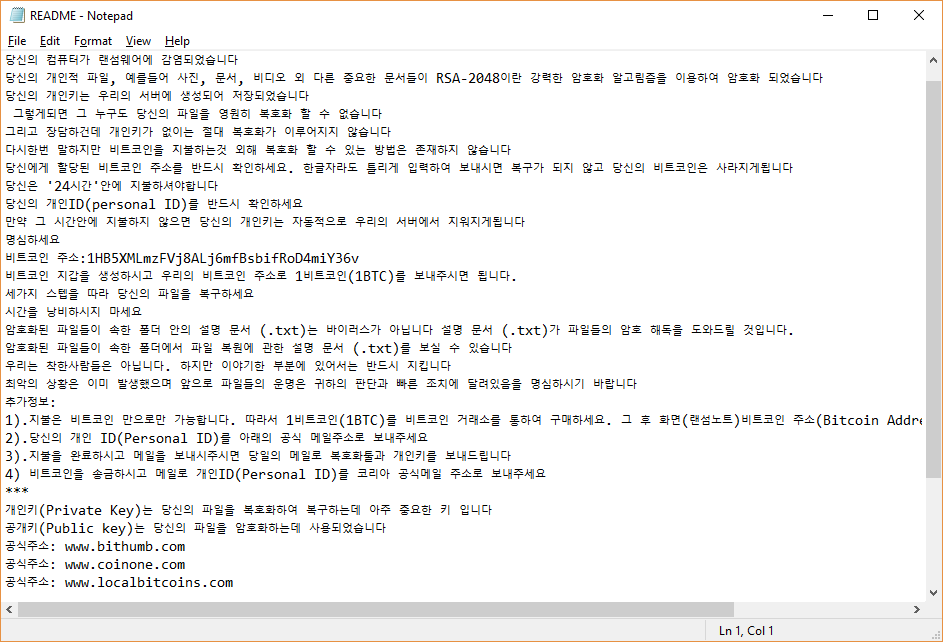
Once all processes have completed succesfully the ransomware engine is started. It uses a built-in list of target file type extensions that seeks to impact the most widely used user data: archives, documents, backups, images, music, videos and etc. All victim data is renamed with the .locked extension. The accompanying ransomware note is crafted in a README.txt file containing the following text message:
—————— koreanLocker Ransomware ——————
당신의 컴퓨터가 랜섬웨어에 감염되었습니다
당신의 개인적 파일, 예를들어 사진, 문서, 비디오 외 다른 중요한 문서들이 RSA-2048이란 강력한 암호화 알고림즘을 이용하여 암호화 되었습니다
당신의 개인키는 우리의 서버에 생성되어 저장되었습니다
그렇게되면 그 누구도 당신의 파일을 영원히 복호화 할 수 없습니다
그리고 장담하건데 개인키가 없이는 절대 복호화가 이루어지지 않습니다
다시한번 말하지만 비트코인을 지불하는것 외해 복호화 할 수 있는 방법은 존재하지 않습니다
당신에게 할당된 비트코인 주소를 반드시 확인하세요. 한글자라도 틀리게 입력하여 보내시면 복구가 되지 않고 당신의 비트코인은 사라지게됩니다
당신은 ’24시간’안에 지불하셔야합니다
당신의 개인ID(personal ID)를 반드시 확인하세요
만약 그 시간안에 지불하지 않으면 당신의 개인키는 자동적으로 우리의 서버에서 지워지게됩니다
명심하세요
비트코인 주소:1HB5XMLmzFVj8ALj6mfBsbifRoD4miY36v
비트코인 지갑을 생성하시고 우리의 비트코인 주소로 1비트코인(1BTC)를 보내주시면 됩니다.
세가지 스텝을 따라 당신의 파일을 복구하세요
시간을 낭비하시지 마세요
암호화된 파일들이 속한 폴더 안의 설명 문서 (.txt)는 바이러스가 아닙니다 설명 문서 (.txt)가 파일들의 암호 해독을 도와드릴 것입니다.
암호화된 파일들이 속한 폴더에서 파일 복원에 관한 설명 문서 (.txt)를 보실 수 있습니다
우리는 착한사람들은 아닙니다. 하지만 이야기한 부분에 있어서는 반드시 지킵니다
최악의 상황은 이미 발생했으며 앞으로 파일들의 운명은 귀하의 판단과 빠른 조치에 달려있음을 명심하시기 바랍니다
추가정보:
1).지불은 비트코인 만으로만 가능합니다. 따라서 1비트코인(1BTC)를 비트코인 거래소를 통하여 구매하세요. 그 후 화면(랜섬노트)비트코인 주소(Bitcoin Address)로 1비트코인(1BTC)를 송금하세요
2).당신의 개인 ID(Personal ID)를 아래의 공식 메일주소로 보내주세요
3).지불을 완료하시고 메일을 보내시주시면 당일의 메일로 복호화툴과 개인키를 보내드립니다
4) 비트코인을 송금하시고 메일로 개인ID(Personal ID)를 코리아 공식메일 주소로 보내주세요
***
개인키(Private Key)는 당신의 파일을 복호화하여 복구하는데 아주 중요한 키 입니다
공개키(Public key)는 당신의 파일을 암호화하는데 사용되었습니다
공식주소: www.bithumb.com
공식주소: www.coinone.com
공식주소: www.localbitcoins.com
암호화된 파일들이 속한 폴더 안의 설명 문서 (.txt)는 바이러스가 아닙니다 설명 문서 (.txt)가 파일들의 암호 해독을 도와드릴 것입니다.
비트코인 주소:1HB5XMLmzFVj8ALj6mfBsbifRoD4miY36v
Officail Mail: [email protected]
***
Best Regards
Korean Ransomware Team
—————— koreanLocker Ransomware ——————
A machine-translated copy of it reads the following:
Your computer is infected with Ransomware
Your personal files, such as photos, documents, videos and other important documents, are encrypted using strong encryption algorithms called RSA-2048
Your private key is created and stored on our server
No one can decrypt your files forever.
And I guarantee you will never be able to decrypt without a private key.
Again, there is no way to pay for a bit coin and decode it
Be sure to check the bit coin address assigned to you. If you send it wrong, it will not be recovered and your bit coin will disappear
You have to pay in ’24 hours’
Be sure to check your personal ID
If you do not pay within that time, your private key will be automatically deleted from our server
Please keep in mind
Bit coin address: 1HB5XMLmzFVj8ALj6mfBsbifRoD4miY36v
Create a bit coin purse and send us a bit coin (1BTC) to our bit coin address.
Follow the three steps to restore your files
Do not waste your time.
The explanatory document (.txt) in the folder to which the encrypted files belong is not a virus Explanation document (.txt) will help you decrypt the files.
You can see a document (.txt) about restoring files in the folder where the encrypted files belong
We are not good people. But in a part of the story,
Please note that the worst has already happened and that the fate of the files will depend on your judgment and quick action.
Additional information:
1) Payment is only possible with bit coin. Therefore, please purchase 1-bit coin (1BTC) through BITC. Then transfer the 1-bit coin (1BTC) to the screen (Random Note) bitcoin address
Please send your personal ID to the official e – mail address below.
3) .Please complete the payment and send us an e-mail, and we will send your decryption tool and private key to the e-mail of the day
4) Please send a bit coin and mail your personal ID to Korea official e-mail address.
***
Private key is the key to decrypting and recovering your files
The public key was used to encrypt your file
Official address: www.bithumb.com
Official address: www.coinone.com
Official address: www.localbitcoins.com
The explanatory document (.txt) in the folder to which the encrypted files belong is not a virus Explanation document (.txt) will help you decrypt the files.
Bit coin address: 1HB5XMLmzFVj8ALj6mfBsbifRoD4miY36v
The computer analysts note that some samples can also include lockscreen instances that can prevent ordinary computer interaction until the virus is completely removed.
Remove Korean Locker Virus and Restore PC
WARNING! Manual removal of the Korean Locker Virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Korean Locker Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Remove Korean Locker from Windows
Here’s a way to remove the program. This method will work regardless if you’re on Windows 10, 8, 7, Vista or XP. Simply selecting the program and pressing delete won’t work, as it’ll leave a lot of small files. That’s bad because these leftovers can linger on and cause all sorts of problems. The best way to delete a program is to uninstall it. Here’s how you can do that:
1. Hold the “Windows” button (It’s between CTRL and Alt on most keyboards) and press “R”. You’ll see a pop-up window.

2. In the textbox, type “appwiz.cpl”, then press“ Enter ”.

3. The “Programs and features” menu should now appear. It’s a list of all the programs installed on the PC. Here you can find the program, select it, and press “Uninstall“.

Remove Korean Locker Virus From Your Browser
Before resetting your browser’s settings, you should know that this action will wipe out all your recorded usernames, passwords, and other types of data. Make sure to save them in some way.
-
1. Start Mozilla Firefox. In the upper right corner, click on the Open menu icon and select “Add-ons“.

2. Inside the Add-ons Manager select “Extensions“. Search the list of extensions for suspicious entries. If you find any, select them and click “Remove“.

3. Click again on the Open menu icon, then click “Options“.

4. In the Options window, under “General” tab, click “Restore to Default“.

5. Select “Search” in the left menu, mark the unknown search engine and press “Remove”.

-
1. Start Google Chrome. On the upper-right corner, there a “Customize and Control” menu icon. Click on it, then click on “Settings“.

2. Click “Extensions” in the left menu. Then click on the trash bin icon to remove the suspicious extension.

3. Again in the left menu, under Chrome, Click on “Settings“. Go under “On Startup” and set a new page.

4. Afterward, scroll down to “Search“, click on “Manage search engines“.

5. In the default search settings list, find the unknown search engine and click on “X“. Then select your search engine of choice and click “Make default“. When you are ready click “Done” button in the right bottom corner.

2. In the “Manage add-ons” window, bellow “Add-on Types“, select “Toolbars and Extensions“. If you see a suspicious toolbar, select it and click “Remove“.

3. Then again in the “Manage Add-ons” window, in “Add-on Types“, Select “Search Providers“. Chose a search engine and click “Set as default“. Select the unknown search engine and click “Remove and Close”.

4. Open the Tools menu, select “Internet Options”.

5. In the “General” tab, in “Home page”, enter your preferred page. Click “Apply” and “OK”.

Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help



