Shark ransomware project surfaced in mid-July 2016. The ransomware service raised a few eyebrows with its generous 80% cut for its affiliates. Most experts claimed that the service looks like a scam. Shark has now rebranded itself as Atom due to the well-deserved negative publicity.
Image Is Important Even for Criminals
Back in August, our team reported on the Shark ransomware project. The large cut that the ransomware distributors were promised seemed too good to be true. By the looks of it, the large pay-off was created to lure would-be scammers into biting the bait.
The service offered flexible code that can be easily modified into whatever their shady customers felt like. The practice of offering ready-made ransomware is known as Ransomware-as-a-Service or RaaS for short. Shark was free to download, the only fee users paid was a cut of the profits to the ransomware’s developers.
Shark Transforms into Atom Builder
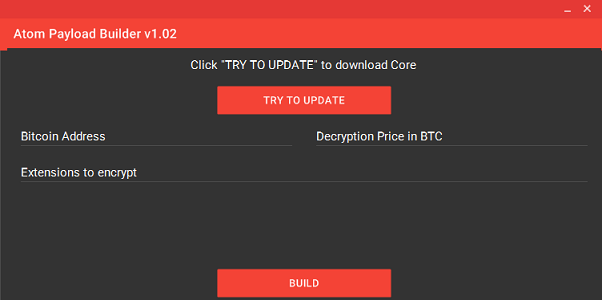
The new version of the Shark ransomware project was reported on Fortinet’s Blog. Atom Builder is made to be more (ab)user-friendly. It has an actual interface, replacing the command line of Shark. That’s a bit troubling, as we pointed out in our Shark summary. Crooks who aren’t even competent enough to work with ransom tools are somehow more frightening then those who do. Atom keeps the generous 20/80 split of its Shark predecessor. The new ransomware project also contains a monitoring software that lets the crooks know how many system they’ve infected and other information relevant to them. This is done via custom tracking ID codes.
The Atom Ransomware’s Scamming Process
Atom infects users through malicious email spam, as is usual for ransomware viruses. Important files on the infected PC then get encrypted using the complex AES-256 algorithm. The locked files will, predictably, have the “.locked” file extension.
The files will be locked until the crooks give the keys to the user, or a decryptor tool gets created. The crooks communicate with their victims mostly through email. Every user has a randomly generated key for their computer.
The Atom Builder’s Interface:
Atom Ransomware Service – Conclusion
All the payments that victims make to the scammers go through Bitcoin wallets owned by the Atom developers. In other words, they may decide to hold off payments to their affiliates. There’s nothing stopping them from doing it. What would scammers do if they get ripped off? Call the cyber-police? Sadly, users can’t do it also, as paying cyber criminals isn’t advisable. In a way, by paying the ransom, victims are also engaging in illegal activity, as they’re financing criminals.
As good as it would be to see the would-be scammers get nothing for their efforts, it also means that other crooks are getting paid. And that’s not OK. It wouldn’t be the first time cybercriminals took advantage from other cybercriminals, as the Pahan malware tools infections showed. It’s a dog-eat-dog business. The big cut that affiliates receive is bound to attract some hapless cybercrooks.



