A new ELF backdoor Trojan dubbed Mirai has been spotted by MalwareMustDie’s specialists. It is targeting IoT devices and Linux servers. Several attacks by Mirai Trojan have been detected in the wild.
The name of this new ELF backdoor Trojan comes from its discovered binaries that contain the string “mirai.()”. The threat infects IoT devices, routers, DVR or WebIP Camera and the Linux with BusyBox binary in embedded platforms. Mirai has its predecessors which are Gafgyt, BASHLITE, Bash0day, Lizkebab, Bashdoor, and Torlus Trojans. The researchers have observed many similarities in the functionalities of these Trojans.
Some of the Mirai’s binaries presented by MalwareMustDie’s researchers are:
- Mirai.arm
- Mirai.arm7
- Mirai.mips
- Mirai.ppc
- Mirai.sh4
- Mirai.x86
They have collected them from multiple direct and indirect sources. Furthermore, in their report, they have provided information on the malware hashes. Platforms on which IoT devices are usually built, such as ARM, ARM7, MIPS, PPC, SH4, SPARC, and x86 are reported to be on the target list of Mirai Linux Trojan.
It seems that currently Mirai is a really cunning threat as only few AV software detect its malicious files. The researchers explain this fact by the lack of enough Mirai samples. The malicious files of Mirai Linux Trojan are difficult to fetch from the infected systems. The low detection ratio can also be explained by the Mirai feature to delete all malware files once it successfully sets the backdoor port into the system. It leaves only the delayed process where the malware is running after being executed.
Last month another Linux Trojan called Linux.PNScan had been discovered. It targets routers based on x86 Linux in an attempt to install backdoors on them. Unfortunately, Mirai Linux Trojan analyzed by MalwareMustDie’s specialists appears to be even more sophisticated.
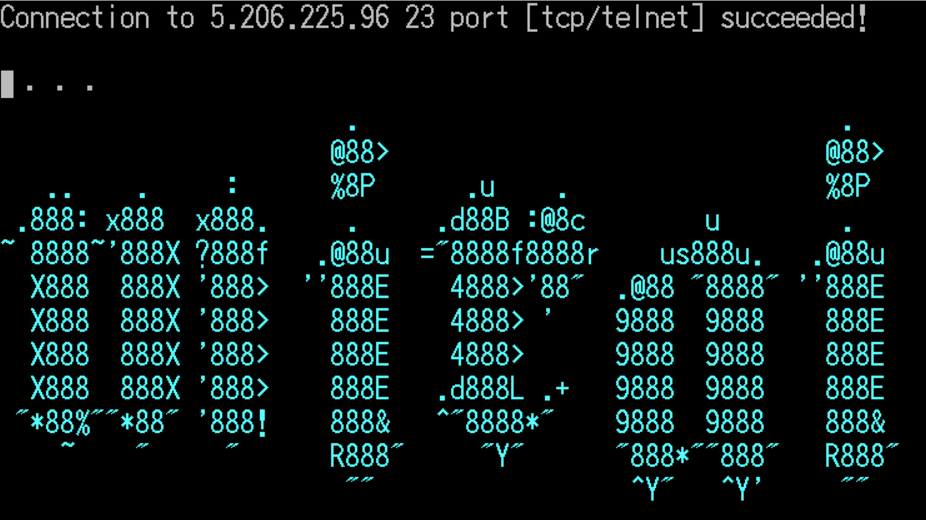
The vulnerability that allows the attackers to insert malware in the IoT devices running BusyBox is the unchanged default password set for the SSH and Telnet account. It determines which devices have an unchanged built-in password by using its embedded list of default admin credentials. Then Mirai executes brute-force attacks on the Telnet port to infect the devices. Once it is running on the device, Mirai connects to its C&C server, reports information and waits for next commands. As reported Mirai Linux Trojan can launch DDoS attacks. Furthermore, it launches brute-force attacks to spread itself to other IoT devices. Thus cybercriminals can easily utilize botnet attack via Mirai Trojan infection.



