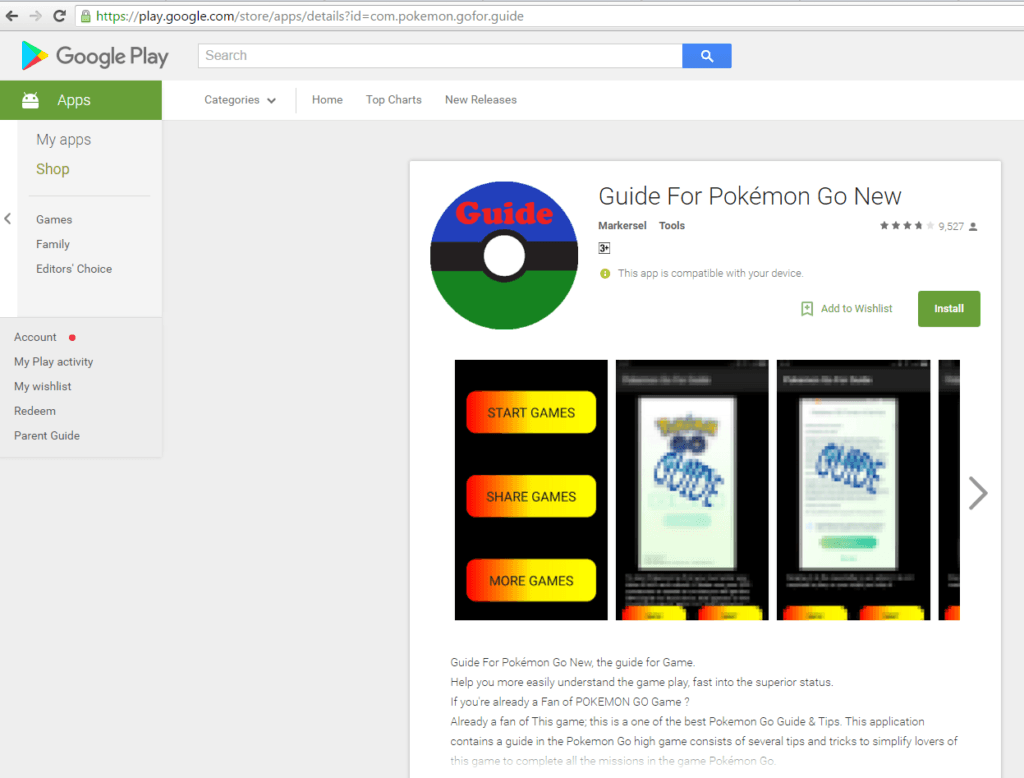
A new Pokemon Go themed malware threat has appeared on the Google Play Store titled Guide for Pokemon Go.
The Guide for Pokemon Go Is the Latest Threat That Scams Users on Google Play
A rogue application title Guide for Pokemon Go has appeared on the Google Play Store. Upon installation, it gives criminals remote root access to the victim Android device.The Trojan contains code that also roots the users. The malicious developers have encrypted the executable in a commercial packer to avoid detection.
The actual malicious code is started once the user opens the app’s browser. The obfuscated module is then engaged in the malware starts to run. A rather strange behaviour has been devised by the criminal developers, the malware waits two hours before executing. This is yet another trick to try to hide the malicious code from heuristic scans. The Trojan also makes pauses between the communication with the C&C servers. The server communicates with the Trojan with a specific ID string which acts as a command trigger.
The Trojan uses numerous exploits and backdoors that install modules into Android systems folders, modify installed application and institute unwanted ads to the victim users. The malware also sends the malicious operators detailed information about the infected devices, including the OS version, country, language and device model.
The malware has been downloaded more than 500 000 times before it was reported to Google and they removed it from the Play store. The statistics show that 6000 out of them were infected. The developers have targeted the malicious app to English-speaking countries, however, most of the victims were identified in Russia, India, and Indonesia.
Other applications that contain the same malicious modules have been identified as well. It seems that the Pokemon Go game will continue to be used as bait for phishing scams and counterfeit malicious apps by criminal operators.