The LOPTR ransomware virus is the the latest iteration of the Locky malware family that has just been identified in an ongoing attack. The virus encrypts user data and adds the .loptr file extension to the affected files. The hackers extort the victims to pay a fee to restore their files. Victims can remove LOPTR virus in 2 ways:
DOWNLOAD LOPTR Virus Removal Tool
Once LOPTR ransomware virus is removed successfully, you can try to restore your files following our instructions below.
Loptr Ransomware Virus Description
The LOPTR ransomware virus has been identified by malware researchers. As it stems from an advanced malware family it may cause other issues, including performance problems and dangerous system modifications. The LOPTR ransomware virus follows the behavior patterns of the last major version of Locky – the .Aesir Locky ransomware virus.
The aim of the LOPTR ransomware virus is to modify the system thereby achieving a persistent state of execution. This means that the malicious core engine is able to monitor the victims actions and guard itself against manual removal. Most of the viruses associated with this family are customized copies of the same core. This means that the LOPTR is also able to cause additional damage to the victim computers upon infection.
A popular tactic is the inclusion of stealth protection features. This means that the LOPTR virus is able to check if the infected host is running in a virtual machine, sandbox environment or a debugging testing machine.Every infected machine is assigned a unique victim during the initial infection. It uses harvested system information to calculate the value.
It may also search for any installed or running security software that are disabled and potentially removed. Depending on the configuration of the individual malware samples the engine might perform additional checks and actions. After the initial vectors are complete the LOPTR ransomware virus begins to encrypt a predefined list of files. The encryption module uses a built-in list of target file type extensions that are marked with the .loptr file extension. Previous versions of the Locky malware family have targeted a large list of file type extensions that are due to be processed:
.yuv, .ycbcra, .xis, .x3f, .x11, .wpd, .tex, .sxg, .stx, .st8, .st5, .srw, .srf, .sr2, .sqlitedb, .sqlite3, .sqlite, .sdf, .sda, .sd0, .s3db, .rwz, .rwl, .rdb, .rat, .raf, .qby, .qbx, .qbw, .qbr, .qba, .py, .psafe3, .plc, .plus_muhd, .pdd, .p7c, .p7b, .oth, .orf, .odm, .odf, .nyf, .nxl, .nx2, .nwb, .ns4, .ns3, .ns2, .nrw, .nop, .nk2, .nef, .ndd, .myd, .mrw, .moneywell, .mny, .mmw, .mfw, .mef, .mdc, .lua, .kpdx, .kdc, .kdbx, .kc2, .jpe, .incpas, .iiq, .ibz, .ibank, .hbk, .gry, .grey, .gray, .fhd, .fh, .ffd, .exf, .erf, .erbsql, .eml, .dxg, .drf, .dng, .dgc, .des, .der, .ddrw, .ddoc, .dcs, .dc2, .db_journal, .csl, .csh, .crw, .craw, .cib, .ce2, .ce1, .cdrw, .cdr6, .cdr5, .cdr4, .cdr3, .bpw, .bgt, .bdb, .bay, .bank, .backupdb, .backup, .back, .awg, .apj, .ait, .agdl, .ads, .adb, .acr, .ach, .accdt, .accdr, .accde, .ab4, .3pr, .3fr, .vmxf, .vmsd, .vhdx, .vhd, .vbox, .stm, .st7, .rvt, .qcow, .qed, .pif, .pdb, .pab, .ost, .ogg, .nvram, .ndf, .m4p, .m2ts, .log, .hpp, .hdd, .groups, .flvv, .edb, .dit, .dat, .cmt, .bin, .aiff, .xlk, .wad, .tlg, .st6, .st4, .say, .sas7bdat, .qbm, .qbb, .ptx, .pfx, .pef, .pat, .oil, .odc, .nsh, .nsg, .nsf, .nsd, .nd, .mos, .indd, .iif, .fpx, .fff, .fdb, .dtd, .design, .ddd, .dcr, .dac, .cr2, .cdx, .cdf, .blend, .bkp, .al, .adp, .act, .xlr, .xlam, .xla, .wps, .tga, .rw2, .r3d, .pspimage, .ps, .pct, .pcd, .m4v, .fxg, .flac, .eps, .dxb, .drw, .dot, .db3, .cpi, .cls, .cdr, .arw, .ai, .aac, .thm, .srt, .save, .safe, .rm, .pwm, .pages, .obj, .mlb, .md, .mbx, .lit, .laccdb, .kwm, .idx, .html, .flf, .dxf, .dwg, .dds, .csv, .css, .config, .cfg, .cer, .asx, .aspx, .aoi, .accdb, .7zip, .1cd, .xls, .wab, .rtf, .prf, .ppt, .oab, .msg, .mapimail, .jnt, .doc, .dbx, .contact, .n64, .m4a, .m4u, .m3u, .mid, .wma, .flv, .3g2, .mkv, .3gp, .mp4, .mov, .avi, .asf, .mpeg, .vob, .mpg, .wmv, .fla, .swf, .wav, .mp3, .qcow2, .vdi, .vmdk, .vmx, .wallet, .upk, .sav, .re4, .ltx, .litesql, .litemod, .lbf, .iwi, .forge, .das, .d3dbsp, .bsa, .bik, .asset, .apk, .gpg, .aes, .ARC, .PAQ, .tar.bz2, .tbk, .bak, .tar, .tgz, .gz, .7z, .rar, .zip, .djv, .djvu, .svg, .bmp, .png, .gif, .raw, .cgm, .jpeg, .jpg, .tif, .tiff, .NEF, .psd, .cmd, .bat, .sh, .class, .jar, .java, .rb, .asp, .cs, .brd, .sch, .dch, .dip, .pl, .vbs, .vb, .js, .asm, .pas, .cpp, .php, .ldf, .mdf, .ibd, .MYI, .MYD, .frm, .odb, .dbf, .db, .mdb, .sql, .SQLITEDB, .SQLITE3, .011, .010, .009, .008, .007, .006, .005, .004, .003, .002, .001, .pst, .onetoc2, .asc, .lay6, .lay, .ms11 (Security copy), .ms11, .sldm, .sldx, .ppsm, .ppsx, .ppam, .docb, .mml, .sxm, .otg, .odg, .uop, .potx, .potm, .pptx, .pptm, .std, .sxd, .pot, .pps, .sti, .sxi, .otp, .odp, .wb2, .123, .wks, .wk1, .xltx, .xltm, .xlsx, .xlsm, .xlsb, .slk, .xlw, .xlt, .xlm, .xlc, .dif, .stc, .sxc, .ots, .ods, .hwp, .602, .dotm, .dotx, .docm, .docx, .DOT, .3dm, .max, .3ds, .xml, .txt, .CSV, .uot, .RTF, .pdf, .XLS, .PPT, .stw, .sxw, .ott, .odt, .DOC, .pem, .p12, .csr, .crt, .key
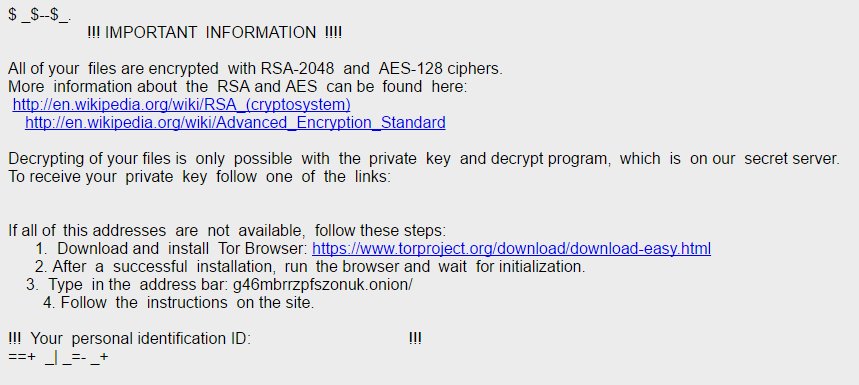
A ransomware note is then generated in a loptr-*4characters*.htm file that reads that following message:
$__$==$_.
!!! IMPORTANT INFORMATION !!!!
All of your files are encrypted with RSA-2048 and AES-128 ciphers. More information about the RSA and AES can be found here: http://en.wikipedia.org/wiki/RSA (cryptosystern) http://en.wikipedia.org/wiki/Advanced Encryption Standard
Decrypting of your files is only possible with the private key and decrypt program, which is on our secret server. To receive your private key follow one of the links:
If all of this addresses are not available, follow these steps: 1. Download and install Tor Browser: https://www.torproject.org/download/download-easv.html 2. After a successful installation, run the browser and wait for initialization. 3. Type in the address bar: g46mbrrzpfszonuk.onion/ 4. Follow the instructions on the site.
it Your personal identification ID: !!! ==+
As usual the victims are extorted to pay a ransomware fee in the Bitcoins digital currency. The exact sum is displayed in the crafted payment gateway that is hosted on the anonymous TOR network. The hidden service may present a varying fee depending on the size and nature of the affected user data.
The computer users are instructed to visit the LOPTR ransomware virus site where other tricks may be imposed – a time limit, trial decryption options and etc.
Loptr Ransomware Virus Distribution
The LOPTR ransomware virus is usually delivered via email spam campaigns or exploit kits. Examples include the Rig Exploit Kit and hacker intrusion attempts such as OPM breach.
Other LOPTR ransomware virus spreda tactics include direct intrusion attempts using automated software vulnerability testing frameworks. Computer users can protect themselves from any incoming attacks by using a quality anti-spyware solution as well as ensuring that they have updated all installed software to the latest available versions.
The LOPTR virus can also be found in modified software installers. Hackers take legitimate software packages and bundle the malicious code on them. The executables are then posted on various download sites and portals that pose as official sources. In a similar manner the criminals create infected Office documents that download the LOPTR ransomware virus when the victims interact with the built-in scripts (macros).
According to the research performed by the security specialists often P2P networks like BitTorrent also serve a large part of the virus samples.
How to Remove Loptr Ransomware Virus
As mentioned earlier, you can remove Loptr ransomware virus by following the manual instructions below.
WARNING! Manual removal of Loptr ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
LOPTR Ransomware – Manual Removal Steps
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely LOPTR Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
How To Restore .loptr Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



