Malicious email campaigns spread the Locky ransomware to concerned users who are victims of the OPM (Office of Personnel Management) breach.
Scared OPM Breach Users Lured By Locky Via Emails
Last year’s major data breach which occurred in the Office of Personnel Management (OPM) has been used as a strategy for malicious hackers who spread Locky-infected binaries. The institution was hacked numerous times and this has caused major concerns for the affected users. OPT holds sensitive information including personally identifiable information for about 32 million federal employees as well as retired personnel. The cause of the serious incident was blamed on an obsolete IT infrastructure due to underfunding and a lack of investment in the computer security operations.
After every major data breach hackers try to utilize various strategies to profit from the security incidents. This may happen through one of the following scenarios:
- Using leaked information to target specific users using personalized social engineering emails and other forms of messaging.
- Harvesting user credentials from the leaked data and compromising accounts
- Selling the information for monetary gain
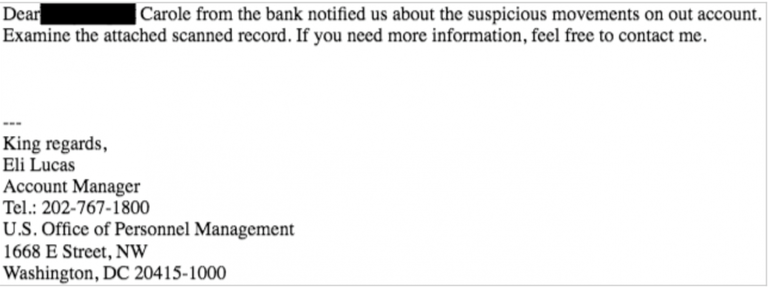
This has led to a large spam campaign that spreads the Locky ransomware. A group of criminals have used phishing emails to attempt to trick the users using a clever scheme. The targets receive emails which claim to originate from the OPM and notifying them of suspicious activity in their bank accounts. The message contents has a ZIP attachment which is disguised as containing information about the fake incident.
If you have been the victim of a Locky ransomware attack click here to read our in-depth removal guide.
The archived file actually contains a malicious JavaScript application which when executed will download and install the Locky ransomware on the local computer. The virus will then engage its encryption engine which compromises target user files and extorts the victims for a payment fee in Bitcoins to recover their files.
Previous noteworthy attacks used various other methods of social engineering against both individual users and companies. The numerous data breaches and hacker attacks have allowed computer criminals to utilize the ransomware in causing additional damage to the victims or to seek new targets.
The Locky malware family is one of the most popular ransomware types. It has caused millions of dollars of damage in this year alone and the fact that attack campaigns continue to utilize it means that the hackers are not going to stop soon. As its code is advanced it is very difficult to recover from active attacks.



