LockedByte ransomware is a cryptovirus that encodes specified files and renames them with a .[random] extension. The culprits extort a ransom payment from victims whose corrupted data is out of rich. The threat is designed to drop a file that contains the ransom message and set it as desktop wallpaper. An infected PC is no longer safe to use. Victims have the opportunity to regain encrypted files via alternative recovery solutions upon the complete removal of LockedByte ransomware virus.
Manual Removal Guide
Recover Encrypted Files
Skip all steps and download anti-malware tool that will safely scan and clean your PC.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
LockedByte Ransomware Virus – Distribution Techniques
It is believed that LockedByte ransomware virus is generally distributed via spam emails that contain an attached file or suspicious link. Fake emails are usually designed in a way to resemble a lot the legitimate ones send by governmental institutions, banks, well-known websites, etc. The malicious LockedByte payload may also be spread via social media, file sharing services, and compromised advertisements.
More Details About LockedByte Ransomware Virus
LockedByte is a computer virus that belongs to an unknown ransomware family. Ransomware is a type of malware that damages the entire system and encrypts particular files that are part of its target list set in its malicious code. Once LockedByte virus payload lands on the computer, it usually spurs victims into action that triggers LockedByte ransomware infection by activating its malware code. At first LockedByte ransomware virus scans computer drives for all file types specified in its target data list. Microsoft Office documents, images, photos, videos, text files, PDF files, music, and archives are likely to be objects of LockedByte attack.
Upon encryption, the original code of each affected file is modified via XOR algorithm and renamed with a .[random] malicious extension. The modified files cannot be run by any software except the decryptor developed by hackers. It works with a decryption key which is generated during the encryption process. The key is individual and unique for each infected user. Victims can get it in return for a ransom payment of $1000 in Bitcoins.
At its last infection stage, the cryptovirus is designed to drop a ransom note on the PC. The file depicts information about the presence of LockedByte ransomware on the system and the damage it has just caused on sensitive data stored on the computer. Also victims are instructed how they are expected to act further to receive their data back. The whole text presented on the ransom note reads:
Your files have been encrypted by LockedByte
All your files have been encrypted and are now hold for ransom
To receive your files back you will have to pay 1000 dollars worth of bitcoin to the address:
17UomAvt4YEDwNYdpFjotdm7CV1i8jJ16Q
Good luck having your files back
>:-)
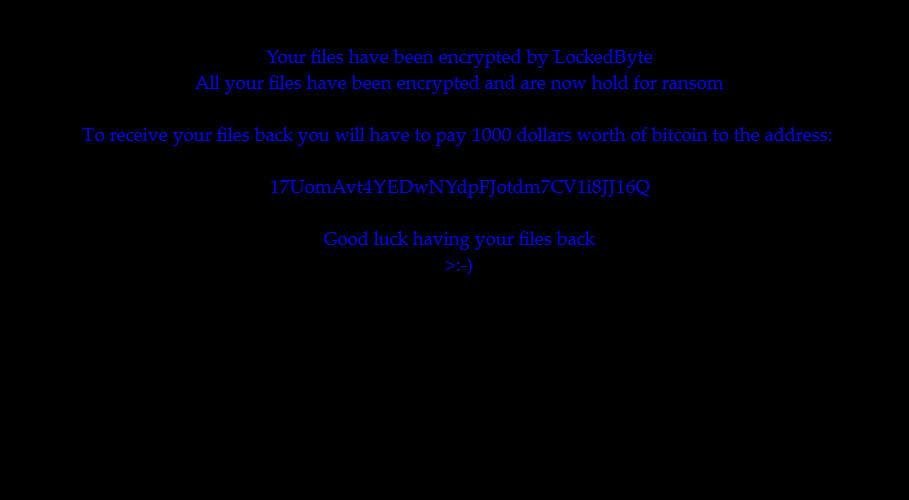
An image file may also replace the desktop wallpaper with the ransom message. Security experts always advise victims of ransomware attacks to avoid any negotiations and payment transactions to criminals. Most of the times the decryption key is not working or is absent at all. Furthermore, funding crooks is a precondition for continuing malicious actions that expose tens of thousands online individual and business users worldwide to offensive cyber attacks like LockedByte and WannaCry ransomware virus that hit the world earlier this month.
So it is better to backup all .[random] encrypted files and store them on an external drive. After the LockedByte virus removal, our recovery section below presents alternative data recovery approaches that may be used to restore some of the corrupted files. Eventually, white hats will come up with a free decryption solution soon. Expect us to update this article with useful information about the free LockedByte decryption tool as soon as it is available.
Stay on the state of security, learn how to get through the removal and recovery processes of LockedByte virus by yourself.
Remove LockedByte Virus and Restore Encrypted Files
WARNING! Manual removal of the LockedByte ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
LockedByte Ransomware Virus – Manual Removal Steps
Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently. The steps bellow are applicable to all Windows versions.
1. Hit the WIN Key + R
2. A Run window will appear. In it, write msconfig and then press Enter
3. A Configuration box shall appear. In it Choose the tab named Boot
4. Mark Safe Boot option and then go to Network under it to tick it too
5. Apply -> OK
Show Hidden Files
Some ransomware threats are designed to hide their malicious files in the Windows so all files stored on the system should be visible.
1. Open My Computer/This PC
2. Windows 7
-
– Click on Organize button
– Select Folder and search options
– Select the View tab
– Go under Hidden files and folders and mark Show hidden files and folders option
3. Windows 8/ 10
-
– Open View tab
– Mark Hidden items option

4. Click Apply and then OK button
Enter Windows Task Manager and Stop Malicious Processes
1. Hit the following key combination: CTRL+SHIFT+ESC
2. Get over to Processes
3. When you find suspicious process right click on it and select Open File Location
4. Go back to Task Manager and end the malicious process. Right click on it again and choose End Process
5. Next, you should go folder where the malicious file is located and delete it
Repair Windows Registry
1. Again type simultaneously the WIN Key + R key combination
2. In the box, write regedit and hit Enter
3. Type the CTRL+ F and then write the malicious name in the search type field to locate the malicious executable
4. In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Click for more information about Windows Registry and further repair help
Recover Encrypted Files
WARNING! All files and objects associated with LockedByte ransomware virus should be removed from the infected PC before any data recovery attempts. Otherwise the virus may encrypt restored files. Furthermore, a backup of all encrypted files stored on external media is highly recommendable.
1. Use present backups
2. Use professional data recovery software
Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
3. Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

4. Restore your personal files using File History
-
– Hit WIN Key
– Type restore your files in the search box
– Select Restore your files with File History
– Choose a folder or type the name of the file in the search bar
– Hit the “Restore” button



