Security analysts detected a new derivative of the infamous Hidden Tear family of viruses. The Kee ransomware is a potent crypto virus that encrypts user data and blackmails the victims to pay a ransomware fee in the Bitcoin digital currency. It displays a ransomware note that is similar to WannaCry. You can remove Kee ransomware virus via:
DOWNLOAD KEE Virus Removal Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Once the Kee ransomware virus is removed successfully, you can try to restore your files following our instructions below.
The Kee Ransomware Virus Impact on an Infected PC
Malware researchers announced the discovery of a new virus called Kee ransomware. It is also known under the aliases @kee and Download Installer. According to the initial analysis it is a new strain of the Hidden Tear family of viruses. In its current iteraton the Kee virus contains only a basic encryption module that processes user data based on a predefined list. At the moment it targets the most popular extensions: documents,archves, music, videos, configuration files and etc. All temporary files are processed in a folder called TestFolder placed on the users desktop.
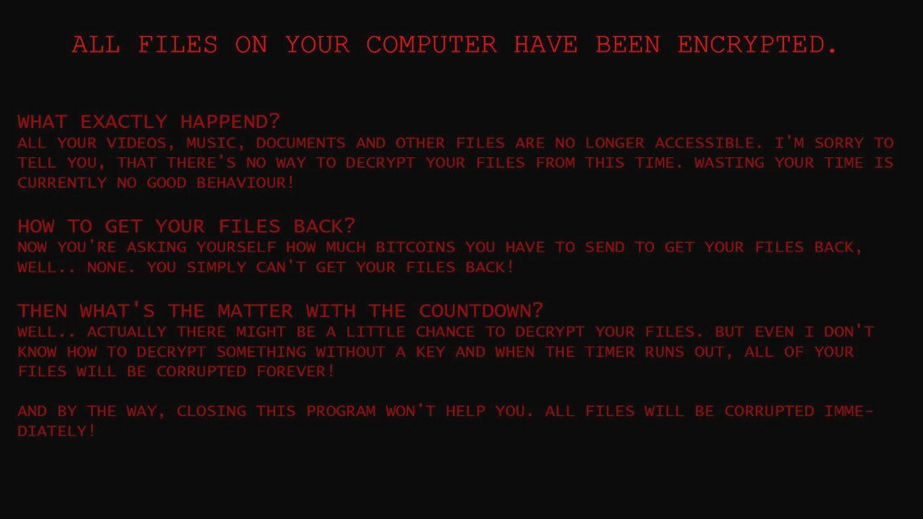
Upon infection it creates a file called killsw32l.dll which controls the malicious functions. The Kee virus starts to encrypt user files and once the process is complete displays both a wallpaper and a lockscreen that resemble the WannaCrypt0r 2.0 Ransomware. The lockscreen effectively prevents ordinary computer interaction until the malware is completely removed from the system. It reads the following message:
What exactly happend?
All your Videos, Music, Documents and other files are no longer accessible. I’m sorry to tell you, that there’s no way to decrypt your files from this time, wasting your time is currently no good behaviour!
How to get your files back?
Now you’re asking yourself how much Bitcoins you have to send to get your files back, well.. None. You simply can’t get your files back!
I see that you’re surprised. But let’s be honest, others are just fake. You send the money.. you get nothing.
I spare you time!
But I’m a good human being!
I don’t care what you are. I have nothing against you! it’s not just you, it’s everyone!
Then what’s the matter with the countdown?
Well.. actually there might be a little chance to decrypt your files. But even I don’t know how to decrypt something without a key and when the timer runs out, all of your files will be corrupted forever!
And by the way, closing this program won’t help you. All files will be corrupted immediately!
Find the kee!
There are two support links that are shown to the victims – “What is AES Encryption?” and “What is an encryption?”. A short time limit is also enforced to blackmail the victims into paying the ransomware fee.
The wallpaper reads a sligtly different message. This is very similar to the last few WannaCry virus iterations where the wallpaper message serves as a backup. In case the main application frame (lockscreen) is disabled the virus remains active on the compromised system.
ALL FILES ON YOUR COMPUTER HAVE BEEN ENCRYPTED.
WHAT EXACTLY HAPPEND?
ALL YOUR VIDEOS, MUSIC, DOCUMENTS AND OTHER FILES ARE NO LONGER ACCESSIBLE. I’M SORRY TO TELL YOU, THAT THERE’S NO WAY TO DECRYPT YOUR FILES FROM THIS TIME. WASTING YOUR TIME IS CURRENTLY NO GOOD BEHAVIOUR!
HOW TO GET YOUR FILES BACK?
NOW YOU’RE ASKING YOURSELF HOW MUCH BITCOINS YOU HAVE TO SEND TO GET YOUR FILES BACK, WELL.. NONE. YOU SIMPLY CAN’T GET YOUR FILES BACK!
THEN WHAT’S THE MATTER WITH THE COUNTDOWN?
WELL.. ACTUALLY THERE MIGHT BE A LITTLE CHANCE TO DECRYPT YOUR FILES. BUT EVEN I DON’T KNOW HOW TO DECRYPT SOMETHING WITHOUT A KEY AND WHEN THE TIMER RUNS OUT , ALL OF YOUR FILES WILL BE CORRUPTED FOREVER!
AND BY THE WAY, CLOSING THIS PROGRAM WON’T HELP YOU. ALL FILES WILL BE CORRUPTED IMMEDIATELY.
The ransomware note is also written in a ” Hello There! Fellow @kee User!.txt” file.
Similar Viruses: CerberTear Virus, Gruxer Ransomware Virus, BlackRose ransomware
Kee Ransomware Virus Distribution Methods
The majority of Kee virus strains are associated with malicious software installers that are distributed on hacker-controlled web sites. Files that include the malware include ones that are named download-installer.exe or under similar random names. The criminals behind the Kee virus can bundle the code in modified software installers that are then uploaded to download sites and portals that resemble the official sources.
Other ways to spread the Kee virus is by sending email spam campaigns that use social engineering tricks. The hackers bundle the malware directly as file attachments or links. Another way of distributing the Kee virus is by sending infected file documents that contain scripts that server as payload droppers. Upon interaction with them the malware is downloaded from a remote server.
Computers users need to be aware that P2P networks like BitTorrent are another source of infections.
Remove Kee Ransomware Virus and Restore .kee Encrypted Files
WARNING! Manual removal of the SecretSystem ransomware virus requires being familiar with system files and registries. Removing important data accidentally can lead to permanent system damage. If you don’t feel comfortable with manual instructions, download a powerful anti-malware tool that will scan your system for malware and clean it safely for you.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
Kee Virus – Manual Removal Steps
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely Kee Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



