FuckTheSystem Ransomware Description
Security researchers uncovered a new virus known as FuckTheSystem ransomware. In its current state it is rated as a very basic type of ransomware. Besides an encryption engine it has no other functionality. It is similar to other ransomware such as the Mikoyan ransomware and the Extractor ransomware that all share a basic encryption engine.We assume that its current version is a test release and not suitable for widespread attacks.
Upon infection with it, the built-in engine automatically starts the encryption process. Like other similar viruses, it uses a predefined list of target file type extensions. At the moment we don’t have access to the one used by the FuckTheSystem ransomware, however, we assume that it processes the most popular ones: music, photos, videos, documents, backups, archives, configuration files and etc.
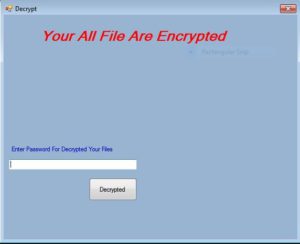
When all user files are encrypted, the .anon extension is used to rename all affected files. A ransomware message is then displayed in an application frame screenlocker. It prohibits ordinary computer interaction and cannot be removed before the virus is completely deleted from the infected computer. The title of the frame is “Decrypt” and it reads the following:
Your All File Are Encrypted
Enter Password For Decrypted Your Files
button [Decrypted]
The users can restore access to their computers by typing in the unlock password: hexobon. There are several important characteristics that can be outlined about the ransomware from its ransomware note:
- No Ransomware Fee – The hackers behind the virus have not specified a fixed ransomware fee. In cases of a contact email address or another form of communication with the criminal operators, the hackers can specify a sum based on the “sensitivity” of the processed victim data.
- No Contact Address – One of the reasons why the virus is still in an early stage of development is the fact that there is no email address provided.
- Unlockable Screenlocker – The security researchers were able to uncover the unlock password during the initial security analysis. Future updated versions will probably contain fully-featured screenlockers that can lock down the infected computers.
- Generic Ransomware Extension – The virus does not use an original extension or a complex pattern to indicate the affected files.
We suspect that a more advanced version will be made in the coming weeks or months. The developers can include major feature additions such as a revamped screenlocker or to even add surveillance modules. In the last few months such instances were used in large-scale attack campaigns that delivered various types of malware.
FuckTheSystem Ransomware Distribution
At the current moment the FuckTheSystem ransomware is delivered in a single binary file called “Crypto.exe”. As there are only a limited number of captured strains we have not been able to uncover the exact distribution strategy. We suspect that the hackers are using some of the most popular methods:
- Email Spam Messages – The criminals generate spam messages that either link the virus in the body of the text or attach it directly to them. In most cases the hackers use various social engineering strategies and attempt to trick the targets into infecting themselves.
- Infected Documents – Malicious office document files have become a very popular tactic for spreading virus. The hackers bundle the dangerous code in built-in scripts. When the users open the files they are presented with a notification prompt that asks them to enable the macros. If this is done the virus payload is downloaded from a remote server and executed on the local machine.
- Hacker-controlled Sites and P2P Networks – Hacked or hacker-controlled sites may pose as legitimate download portals or other counterfeit providers. P2P networks like BitTorrent are also a favorite place for distributing viruses. The criminals may either spread infected software, documents or the virus binary itself.
- Infected Software Installers – The FuckTheSystem ransomware can be bundled with software installers of popular free and trial versions of applicatons, games, utilities, patches and etc.
- Browser Hijacker Delivery – Malicious web browser extensions can deliver the ransomware to the infected computers.
- Dropper Delivery – Other viruse threats can download the malware during their installation routine.
- Direct Hacker Attacks – The hackers may opt to attempt direct hacker intrusions into the target systems.
Viruses like this one showcase that ransomware authors continue to develop malware at an increased rate. We have reported on this issue in a detailed article about ransomware attacks.
Summary of the FuckTheSystem
| Name |
FuckTheSystem Ransomware |
| File Extensions |
.anon |
| Ransom |
Varies |
| Easy Solution |
You can skip all steps and remove FuckTheSystem Ransomware ransomware with the help of an anti-malware tool. |
|
Manual Solution |
FuckTheSystem Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
FuckTheSystem Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely FuckTheSystem Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover FuckTheSystem Files
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
How To Restore FuckTheSystem Files
- 1) Use present backups
- 2) Use professional data recovery software
-
– Stellar Phoenix Data Recovery – a specialist tool that can restore partitions, data, documents, photos, and 300 more file types lost during various types of incidents and corruption.
- 3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

- 4) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



