A new version of the dangerous freeware Trojan known as Darktrace has been identified by security researchers.
Darktrace Is Free and Can Cause a Lot of Damage
Darktrace is a remote access Trojan that is distributed as a free download by a malicious developer known as Luckyduck. The security researchers that have identified the threat from the MalwareHunterTeam state that it is as dangerous as commercial malware available on the underground markets.
Most free Trojans do not contain advanced functions and are easy to detect by the security software. And intrusions often occur using exploits not rendered by the Trojan itself. Darktrace is different from these definitions.
The malware contains a lot of powerful features that can be exploited against networks of users. The malware creator has also created dedicated distribution channels on the Internet as well as social media profiles including a Facebook page, Twitter and Google+ pages. Videos with Darktrace tutorials have also been found on Youtube.
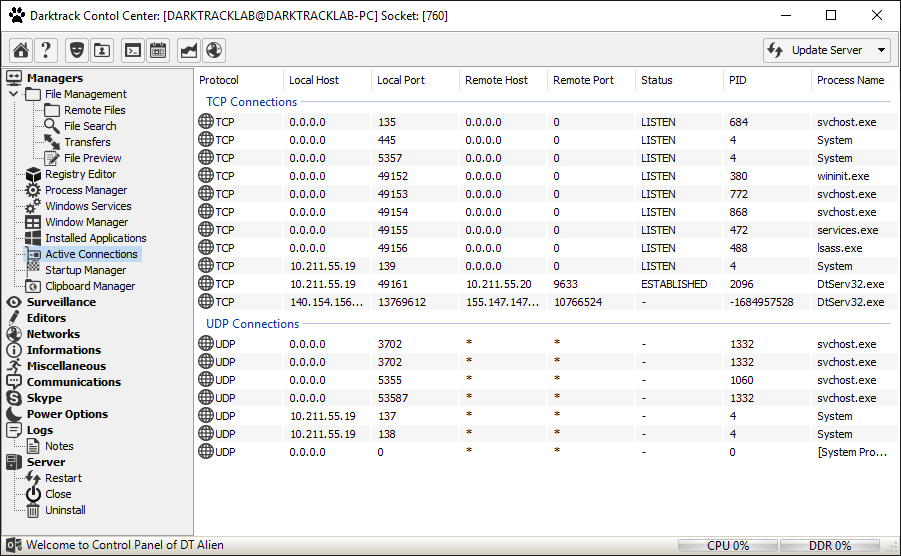
According to Luckyduck the Trojan can connect to remote computers, access their contents and infiltrate the systems and networks. Features include DOS attacks, keylogging, and spying on users (via webcam and keystroke recordings) as well as advanced options such as port scanning, system modification tools, and remote code execution. The program also can interact with the task scheduler of the victim host and manipulate the clipboard.
The developer has committed to updating the Darktrace code by including an auto updater option. Advanced information about the system can be obtained from the network logs and statistics that are recorded upon infection.
Darktrace can modify the registry values and various other system components such as the startup applications. This can be used in conjunction with other malware to induce even further damage to the infected computers.
The full list of Darktrace’s features is available from it’s easy to use graphical user interface:
Main Features
- Connection Manager
- Offline Client Viewer
- Thumbnail Desktop Viewer
- Broadcast Command Sender
- OnConnect Command Editor (on first execution)
- Socket Actions List (For All commands)
- Maps Viewer (Multiple Location Viewer on Google Maps)
- Bug Reporter
- Auto Updater (Version detector)
Main Tabs Features
- Connection Logs
- Network Stress Tester Tools (Http, UDP flooder)
- Statistics
Surveillance Features
- Remote Desktop (Live and control with keyboard and mouse)
- Record Desktop (Remote Desktop Video Recorder on avi format.)
- Webcam Streaming (Live)
- Record Webcam (Remote Webcam Video Recorder on avi format.)
- Microphone Capture
- Audio Recorder
- Keylogger (Online and Offline mode)
- Password Recovery (All versions of Chrome, Mozilla Firefox, Yandex, Comodo Dragon, Outlook, File Zilla)
- Download Executer (From web)
- Upload Executer (From Local)
- Remote Shell (Command Prompt)
Management Features
- File Manager (Download, Upload, Delete, Create etc.)
- File Search
- Text Files Preview
- Image Files Thumbnail Viewer
- Registry Editor (Regedit)
- Process Manager (Task Manager)
- Services Manager
- Windows Manager (+Print Window Image)
- Application Manager
- Startup Manager
- Clipboard Manager (Files and Contents)
Editor Features
- Hosts File Editor
- Fake Message Viewer
- Script Executer (vbs, bat, html)
Network Manager
- Net Shares Viewer
- Lan Computer Scanner
- Port Scanner
Information
- System Monitor (CPU, DDR Monitoring)
- System Privileges List
Miscellaneous
- Key Sender (to all windows or applications)
- Text to Speech
- Print File
Communications
- Skype Manager
- Contact List Viewer
- User Selector
- Transfer Viewer (Files)
- Conversations (All users)
User Chat
Power options
- Restart Computer
- Sleep
- Shut down
- Log Off
- Lock
Logs
- User Notes
Other Features
- Open Web Page
- Task Scheduler
- Command Executer
- Fun Menu
Server options
- Restart
- Close
- Uninstall
- Update (From web or Local Computer)