The CYR-Locker ransomware is a newly developer scareware virus which poses as a serious threat while not actually a serious one at all. Our comprehensive removal guide will guide you in removing it easily.
CYR-Locker Ransomware Description
Security experts have uncovered a new scareware virus known as the CYR-Locker which poses as a dangerous malware. The initial reports indicate that it has been based on unknown code. The complete is not yet available and we do not know if it features a working encryption engine.
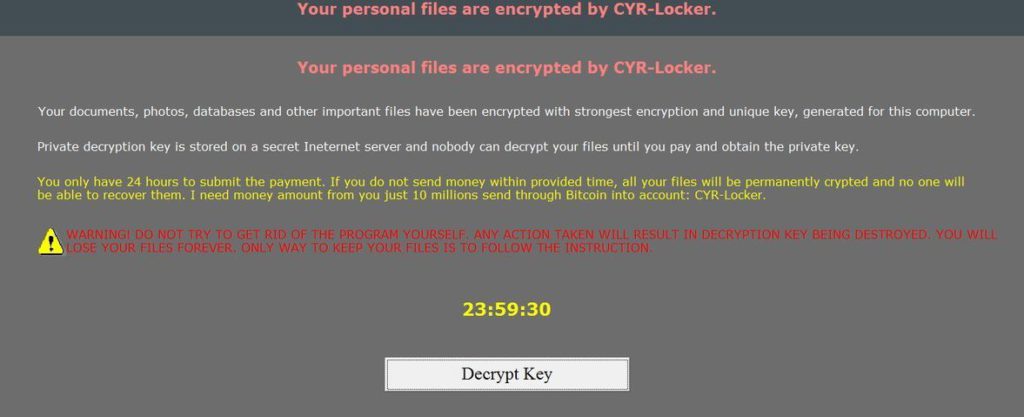
Upon infection the CYR-Locker ransomware creates and launches a screenlocker. This is an application overlay that prohibits ordinary interaction with the victim computer. They are popular with advanced viruses as they can easily scare most users into paying the ransom fee.
The following message is displayed:
Your personal files are encrypted by CYR-Locker.
Your documents, photos, databases and other important files have been encrypted with strongest encryption and unique key, generated for this computer.
Private decryption key is stored on a secret Ineternet server and nobody can decrypt your files until you pay and obtain the private key.
You only have 24 hours to submit the payment. If you do not send money within provided time, all your files will be permanently crypted and no one will be able to recover them. I need money amount from you just 10 millions send through Bitcoin into account: CYR-Locker.
WARNING! DO NOT TRY TO GET RID OF THE PROGRAM YOURSELF. ANY ACTION TAKEN WILL RESULT IN DECRYPTION KEY BEING DESTROYED. YOU WILL LOSE YOUR FILES FOREVER. ONLY WAY TO KEEP YOUR FILES IS TO FOLLOW THE INSTRUCTION.
Note that the virus code mentions that a powerful encryption engine is used however at this moment we cannot confirm this. If a false key is entered an error message is displayed:
Invalid key. Do not be tried any decrypt key if you have not be received the unique key from. Your personal data will be destroyed immediately if you did it failed many time.
Many of the fake ransomware variants can easily be removed by entering a random key if they are of the basic type. This one however does not seem to be of this type. Manual removal can be performed if the security analysts are able to extract a hardcoded key from its code once the complete analysis is complete.
Until then the best removal options is to use a quality anti-malware solution. As the current version does not encrypt user files we might see an updated iteration in the future.
CYR-Locker Ransomware Distribution
The CYR-Locker ransomware is distributed as a single malicious executable file. The first malware samples were reported in the end of February 2017 and the security experts suggest that it probably uses the most popular infections strategies.
Malware such as this one can be delivered via bulk email spam campaigns. They are performed by hackers by either attaching the virus directly to the body of a message or included as a hyperlink in the message or another file related to it. Lately viruses such as this one are often payloads of malicious scripts and macros. They can be carried by infected Office documents (Rich text files or Spreadsheets for example) and hacked sites and advertising services.
Notable sources of infections also include browser hijackers which can modify the settings of the installed web browsers on the infected host. This means that the default home page, new tabs page and default search engine can lead to such infections.
Summary of the CYR-Locker Ransomware Ransomware
| Name |
CYR-Locker Ransomware |
| File Extensions |
Unknown |
| Ransom |
10 Million units of an unspecified amount paid in Bitcoins |
| Easy Solution |
You can skip all steps and remove CYR-Locker Ransomware ransomware with the help of an anti-malware tool. |
| Manual Solution |
CYR-Locker Ransomware ransomware can be removed manually, though it can be very hard for most home users. See the detailed tutorial below. |
Special Feature |
Screen Lock Function |
| Distribution |
Spam Email Campaigns, malicious ads & etc. |
CYR-Locker Ransomware Ransomware Removal
STEP I: Start the PC in Safe Mode with Network
This will isolate all files and objects created by the ransomware so they will be removed efficiently.
-
1) Hit WIN Key + R

- 2) A Run window will appear. In it, write “msconfig” and then press Enter
3) A Configuration box shall appear. In it Choose the tab named “Boot”
4) Mark “Safe Boot” option and then go to “Network” under it to tick it too
5) Apply -> OK
Or check our video guide – “How to start PC in Safe Mode with Networking”
STEP II: Show Hidden Files
-
1) Open My Computer/This PC
2) Windows 7
-
– Click on “Organize” button
– Select “Folder and search options”
– Select the “View” tab
– Go under “Hidden files and folders” and mark “Show hidden files and folders” option
3) Windows 8/ 10
-
– Open “View” tab
– Mark “Hidden items” option

4) Click “Apply” and then “OK” button
STEP III: Enter Windows Task Manager and Stop Malicious Processes
-
1) Hit the following key combination: CTRL+SHIFT+ESC
2) Get over to “Processes”
3) When you find suspicious process right click on it and select “Open File Location”
4) Go back to Task Manager and end the malicious process. Right click on it again and choose “End Process”
5) Next you should go folder where the malicious file is located and delete it
STEP IV: Remove Completely CYR-Locker Ransomware Ransomware Using SpyHunter Anti-Malware Tool
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter
STEP V: Repair Windows Registry
-
1) Again type simultaneously the Windows Button + R key combination
2) In the box, write “regedit”(without the inverted commas) and hit Enter
3) Type the CTRL+F and then write the malicious name in the search type field to locate the malicious executable
4) In case you have discovered registry keys and values related to the name, you should delete them, but be careful not to delete legitimate keys
Further help for Windows Registry repair
STEP VI: Recover Encrypted Files
-
1) Use present backups
2) Restore your personal files using File History
-
– Hit WIN Key
– Type “restore your files” in the search box
– Select “Restore your files with File History”
– Choose a folder or type the name of the file in the search bar

- – Hit the “Restore” button
3) Using System Restore Point
-
– Hit WIN Key
– Select “Open System Restore” and follow the steps

STEP VII: Preventive Security Measures
-
1) Enable and properly configure your Firewall.
2) Install and maintain reliable anti-malware software.
3) Secure your web browser.
4) Check regularly for available software updates and apply them.
5) Disable macros in Office documents.
6) Use strong passwords.
7) Don’t open attachments or click on links unless you’re certain they’re safe.
8) Backup regularly your data.
SpyHunter anti-malware tool will diagnose all current threats on the computer. By purchasing the full version, you will be able to remove all malware threats instantly. Additional information about SpyHunter / Help to uninstall SpyHunter



